InfoSec MASHUP - Week 15/2024
Second Ransomware Group Extorting Change Healthcare; Big Patch Tuesday; AT&T notifies regulators after breach; Sisense breach shakes the world; Failed deepfake CEO call at LastPass;
Partners and affiliates section
🔐 NordVPN’s Spring Sale Campaign (Mar 21 - Jun 12)
Special offer: up to 69% off + 3 months extra.
Breaches & Security Incidents
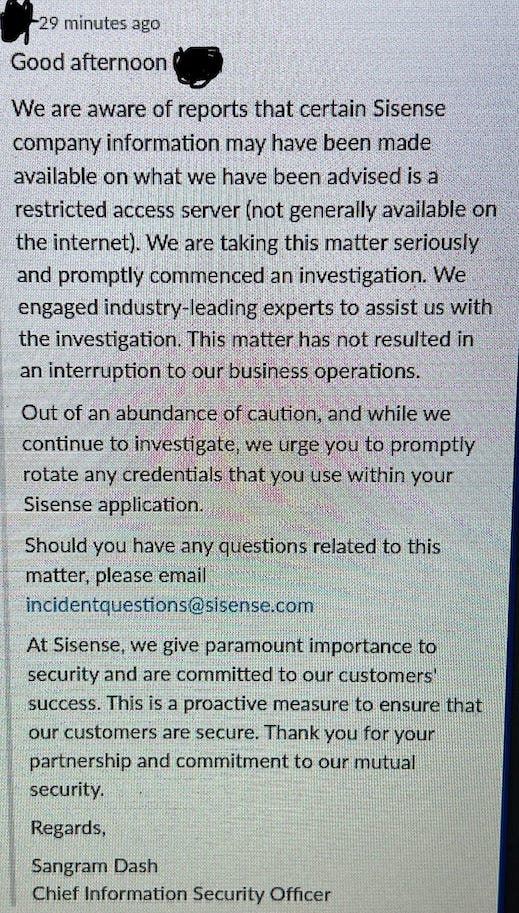
🔓 🇺🇸 CISA says Sisense hack impacts critical infrastructure orgs
"CISA is collaborating with private industry partners to respond to a recent compromise discovered by independent security researchers impacting Sisense, a company that provides data analytics services," the cybersecurity agency said.
"CISA is taking an active role in collaborating with private industry partners to respond to this incident, especially as it relates to impacted critical infrastructure sector organizations. We will provide updates as more information becomes available."
Related: Sisense breach exposes customers to potential supply chain attack
Related: Sisense Data Breach Triggers CISA Alert and Urgent Calls for Credential Resets
Related: Why CISA is Warning CISOs About a Breach at Sisense
🔓 📺 Roku warns 576,000 accounts hacked in new credential stuffing attacks
"After concluding our investigation of [the] first incident, we [..] continued to monitor account activity closely [and] we identified a second incident, which impacted approximately 576,000 additional accounts," Roku said on Friday.
"There is no indication that Roku was the source of the account credentials used in these attacks or that Roku's systems were compromised in either incident."
"In less than 400 cases, malicious actors logged in and made unauthorized purchases of streaming service subscriptions and Roku hardware products using the payment method stored in these accounts, but they did not gain access to any sensitive information, including full credit card numbers or other full payment information."
☎️ 🥸 LastPass: Hackers targeted employee in failed deepfake CEO call
"In our case, an employee received a series of calls, texts, and at least one voicemail featuring an audio deepfake from a threat actor impersonating our CEO via WhatsApp," LastPass intelligence analyst Mike Kosak said.
"As the attempted communication was outside of normal business communication channels and due to the employee’s suspicion regarding the presence of many of the hallmarks of a social engineering attempt (such as forced urgency), our employee rightly ignored the messages and reported the incident to our internal security team so that we could take steps to both mitigate the threat and raise awareness of the tactic both internally and externally."
🔓 🇺🇸 530k Impacted by Data Breach at Wisconsin Healthcare Organization
“Our discovery was confirmed when the attacker, a foreign ransomware gang, contacted GHC-SCW claiming responsibility for the attack and stealing our data,” the company says in a notification letter to the impacted individuals, a copy of which was submitted to the Maine Attorney General’s Office.
“We have no indication that information has been used or further disclosed,” the organization says.
🔓 🇺🇸 AT&T notifies regulators after customer data breach
AT&T has begun notifying U.S. state authorities and regulators of a security incident after confirming that millions of customer records posted online last month were authentic.
In a legally required filing with Maine’s attorney general’s office, the U.S. telco giant said it sent out letters notifying more than 51 million people that their personal information was compromised in the data breach, including around 90,000 individuals in Maine.
AT&T has still not identified the source of the leak.
🔓 🇺🇸 Microsoft employees exposed internal passwords in security lapse
Security researchers Can Yoleri, Murat Özfidan and Egemen Koçhisarlı with SOCRadar, a cybersecurity company that helps organizations find security weaknesses, discovered an open and public storage server hosted on Microsoft’s Azure cloud service that was storing internal information relating to Microsoft’s Bing search engine.
The Azure storage server housed code, scripts and configuration files containing passwords, keys and credentials used by the Microsoft employees for accessing other internal databases and systems.
But the storage server itself was not protected with a password and could be accessed by anyone on the internet.
💸 🇺🇸 Second Ransomware Group Extorting Change Healthcare
One month after paying cybercriminals to prevent the public release of data stolen in a February 2024 ransomware attack, Change Healthcare is being extorted again, by a different cybercrime group.
🔓 🇬🇧 Cyberattack on UK’s CVS Group disrupts veterinary operations
In an announcement published on the London Stock Exchange site, CVS Group warns that threat actors gained unauthorized access to some of its IT systems. The firm responded to the situation by shutting down its IT systems, which impacted its operations.
"CVS Group announces it has recently detected and intercepted a cyber incident which had involved unauthorised external access to a limited number of its IT systems," reads the announcement.
"Upon discovery of the incident, CVS took immediate steps to isolate the issue and, to prevent wider unauthorised access, took its IT systems temporarily offline, as part of the Group's response plan."
🔓 🇺🇸 Hackers stole 340,000 Social Security numbers from government consulting firm
U.S. consulting firm Greylock McKinnon Associates (GMA) disclosed a data breach in which hackers stole as many as 341,650 Social Security numbers.
The data breach was disclosed on Friday on Maine’s government website, where the state posts data breach notifications.
In its data breach notice sent by mail to affected victims, GMA said it was hit by an unspecified cyberattack in May 2023 and “promptly took steps to mitigate the incident.”
🔓 🇺🇸 Targus discloses cyberattack after hackers detected on file servers
As part of this attack, a threat actor gained access to Targus' file systems, causing the company to initiate incident response protocols.
"Upon discovery and with assistance from external cybersecurity counsel and consultants, Targus immediately activated its incident response and business continuity protocols to investigate, contain and remediate the incident," reads the 8-K filing.
"Through this process, proactive containment measures to disrupt unauthorized access resulted in a temporary interruption in the business operations of the Targus network."
🔓 🇺🇸 Home Depot confirms third-party data breach exposed employee info
Home Depot has confirmed that it suffered a data breach after one of its SaaS vendors mistakenly exposed a small sample of limited employee data, which could potentially be used in targeted phishing attacks.
On Thursday, a threat actor known as IntelBroker leaked limited data for approximately 10,000 Home Depot employees on a hacking forum.
"In April 2024, Home Depot suffered a data breach that exposed the corporate information belonging to 10K employees of the company," reads the forum post.
"A third-party Software-as-a-Service (SaaS) vendor inadvertently made public a small sample of Home Depot associates' names, work email addresses and User IDs during testing of their systems," Home Depot told BleepingComputer.
Cybercrime, Cyber Espionage, APT’s
🇺🇦 🇷🇺 Ukrainian Hackers Launch Cyberattacks on Moscow Sewage System
Blackjack, a Ukrainian hacker group affiliated with the Security Service of Ukraine (SBU), said it had launched a cyberattack on Moskollector, a company that operates the communication system for Moscow’s sewage network.
The alleged cyberattack on Moskollector follows another hack from the same group two days ago, on April 8, against Russian data center OwenCloud.ru, which saw the destruction of more than 300 terabytes of data used by the Russian military-industrial complex, oil and gas, and telecom in what the hacker group called a “retaliatory” strike in response to January’s Russian hack on Ukraine’s data center.
Related: How Ukraine’s cyber police fights back against Russia’s hackers
🇺🇸 🇷🇺 US says Russian hackers stole federal government emails during Microsoft cyberattack
U.S. Cybersecurity and Infrastructure Security Agency (CISA) has confirmed that Russian government-backed hackers stole emails from several U.S. federal agencies as a result of an ongoing cyberattack at Microsoft.
In a statement published Thursday, the U.S. cyber agency said the cyberattack, which Microsoft initially disclosed in January, allowed the hackers to steal federal government emails “through a successful compromise of Microsoft corporate email accounts.”
The hackers, which Microsoft calls “Midnight Blizzard,” also known as APT29, are widely believed to work for Russia’s Foreign Intelligence Service, or SVR.
🎣 🇩🇪 TA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer
A threat actor tracked as TA547 has targeted dozens of German organizations with an information stealer called Rhadamanthys as part of an invoice-themed phishing campaign.
"This is the first time researchers observed TA547 use Rhadamanthys, an information stealer that is used by multiple cybercriminal threat actors," Proofpoint said. "Additionally, the actor appeared to use a PowerShell script that researchers suspect was generated by a large language model (LLM)."
🍏 👀 Apple Updates Spyware Alert System to Warn Victims of Mercenary Attacks
Apple on Wednesday revised its documentation pertaining to its mercenary spyware threat notification system to mention that it alerts users when they may have been individually targeted by such attacks.
It also specifically called out companies like NSO Group for developing commercial surveillance tools such as Pegasus that are used by state actors to pull off "individually targeted attacks of such exceptional cost and complexity."
"Though deployed against a very small number of individuals — often journalists, activists, politicians, and diplomats — mercenary spyware attacks are ongoing and global," Apple said.
💸 ☎️ Ransomware gang’s new extortion trick? Calling the front desk
The phone call between the hacker, who claims to represent the ransomware gang DragonForce, and the victim company employee was posted by the ransomware gang on its dark web site in an apparent attempt to put pressure on the company to pay a ransom demand. In reality, the call recording just shows a somewhat hilarious and failed attempt to extort and intimidate a company’s rank-and-file employees.
Government, Politics, and Privacy
🇺🇸 👀 Key Lawmakers Float New Rules for Personal Data Protection; Bill Would Make Privacy a Consumer Right
Two influential lawmakers from opposing parties have crafted a deal on legislation designed to strengthen privacy protections for Americans’ personal data.
The sweeping proposal announced Sunday evening would define privacy as a consumer right and create new rules for companies that collect and use personal information. It comes from the offices of Democratic Sen. Maria Cantwell and Republican Rep. Cathy McMorris Rodgers, both of Washington state.
🇺🇸 🪖 NSA Appoints Dave Luber as Cybersecurity Director
Luber was announced as the next cybersecurity director of the NSA when Joyce’s retirement was revealed in February.
Joyce, a highly respected member of the cybersecurity community, was appointed the NSA’s cybersecurity director in early 2021 and retired after 35 years of service.
🇺🇸 ⚕️ US Health Dept warns hospitals of hackers targeting IT help desks
The sector alert issued by the Health Sector Cybersecurity Coordination Center (HC3) this week says these tactics have allowed attackers to gain access to targeted organizations' systems by enrolling their own multi-factor authentication (MFA) devices.
In these attacks, the threat actors use a local area code to call organizations pretending to be employees in the financial department and provide stolen ID verification details, including corporate ID and social security numbers.
🇮🇱 👀 Top Israeli spy chief exposes his true identity in online security lapse
The identity of the commander of Israel’s Unit 8200 is a closely guarded secret. He occupies one of the most sensitive roles in the military, leading one of the world’s most powerful surveillance agencies, comparable to the US National Security Agency.
Yet after spending more than two decades operating in the shadows, the Guardian can reveal how the controversial spy chief – whose name is Yossi Sariel – has left his identity exposed online.
ICS & OT
🩹 ICS Patch Tuesday: Siemens Addresses Palo Alto Networks Product Vulnerabilities
Siemens published eight new advisories covering a total of roughly 80 vulnerabilities. One advisory covers nearly 50 flaws found in the company’s Telecontrol Server Basic product, particularly in third-party components.
The company also announced patches for three critical arbitrary code execution vulnerabilities in Scalance W1750D access points, which are rebranded Aruba devices.
Schneider Electric has published one new advisory this month, informing customers of a high-severity privilege escalation vulnerability affecting its Easergy Studio product.
Malware & Threats
🦠 👨🏻💻 GitHub's Fake Popularity Scam Tricking Developers into Downloading Malware
"Attackers create malicious repositories with popular names and topics, using techniques like automated updates and fake stars to boost search rankings and deceive users," security researcher Yehuda Gelb said.
The idea is to manipulate the search rankings in GitHub to bring threat actor-controlled repositories to the top when users filter and sort their results based on the most recent updates and increase the popularity via bogus stars added via fake accounts.
🦠 💳 Sneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
Sucuri said that the malware is injected into websites through tools that allow for custom code, such as WordPress plugins like Simple Custom CSS and JS or the "Miscellaneous Scripts" section of the Magento admin panel.
"Custom script editors are popular with bad actors because they allow for external third party (and malicious) JavaScript and can easily pretend to be benign by leveraging naming conventions that match popular scripts like Google Analytics or libraries like JQuery," security researcher Matt Morrow said.
🦠 👀 'eXotic Visit' Spyware Campaign Targets Android Users in India and Pakistan
"Downloaded apps provide legitimate functionality, but also include code from the open-source Android XploitSPY RAT," ESET security researcher Lukáš Štefanko said in a technical report released today.
The campaign is said to be highly targeted in nature, with the apps available on Google Play having negligible number of installs ranging from zero to 45. The apps have since been taken down.
🦠 Raspberry Robin Returns: New Malware Campaign Spreading Through WSF Files
"Historically, Raspberry Robin was known to spread through removable media like USB drives, but over time its distributors have experimented with other initial infection vectors," HP Wolf Security researcher Patrick Schläpfer said in a report shared with The Hacker News.
Raspberry Robin, also called QNAP worm, was first spotted in September 2021 that has since evolved into a downloader for various other payloads in recent years, such as SocGholish, Cobalt Strike, IcedID, BumbleBee, and TrueBot, and also serving as a precursor for ransomware.
🦠 🇲🇦 Hackers Targeting Human Rights Activists in Morocco and Western Sahara
Human rights activists in Morocco and the Western Sahara region are the targets of a new threat actor that leverages phishing attacks to trick victims into installing bogus Android apps and serve credential harvesting pages for Windows users.
Cisco Talos is tracking the activity cluster under the name Starry Addax, describing it as primarily singling out activists associated with the Sahrawi Arab Democratic Republic (SADR).
Starry Addax's infrastructure – ondroid[.]site and ondroid[.]store – is designed to target both Android and Windows users, with the latter involving fake websites masquerading as login pages for popular social media websites.
AI, Tech & Tools
🛠️ MISP 2.4.189 RELEASED WITH BUG FIXES, PERFORMANCE IMPROVEMENTS AND A NEW BLOCKLIST FEATURE.
The OWASP Foundation today announced the availability of CycloneDX v1.6. This significant release strengthens software supply chain security with the introduction of two innovative capabilities: Cryptographic Bill of Materials (CBOM), developed by IBM Research, and CycloneDX Attestations (CDXA).
CycloneDX v1.6 builds upon the existing strengths of the CycloneDX standard, which provides a machine-readable format for capturing the components that comprise software (SBOM), hardware (HBOM), services (SaaSBOM), and AI/ML models (AI/ML-BOM). CycloneDX builds upon a legacy of innovation, empowering organizations to reduce risk and enhance software and system transparency.
💻 🔐 Google Chrome Adds V8 Sandbox - A New Defense Against Browser Attacks
Google has announced support for what's called a V8 Sandbox in the Chrome web browser in an effort to address memory corruption issues.
The sandbox, according to V8 security technical lead Samuel Groß, aims to prevent "memory corruption in V8 from spreading within the host process."
The search behemoth has described V8 Sandbox as a lightweight, in-process sandbox for the JavaScript and WebAssembly engine that's designed to mitigate common V8 vulnerabilities.
Vulnerabilities, Research, and Threat Intelligence
🗓️ Patch Tuesday:
SAP’s April 2024 Updates Patch High-Severity Vulnerabilities
Microsoft April 2024 Patch Tuesday fixes 150 security flaws, 67 RCEs
Microsoft fixes two Windows zero-days exploited in malware attacks
Fortinet Rolls Out Critical Security Patches for FortiClientLinux Vulnerability
Palo Alto Networks Patches Vulnerabilities Allowing Firewall Disruption
Google Pays Out $41,000 for Three Serious Chrome Vulnerabilities
🐛 🧱 CVE-2024-3400 PAN-OS: OS Command Injection Vulnerability in GlobalProtect Gateway
A command injection vulnerability in the GlobalProtect feature of Palo Alto Networks PAN-OS software for specific PAN-OS versions and distinct feature configurations may enable an unauthenticated attacker to execute arbitrary code with root privileges on the firewall.
Fixes for PAN-OS 10.2, PAN-OS 11.0, and PAN-OS 11.1 are in development and are expected to be released by April 14, 2024. Cloud NGFW, Panorama appliances, and Prisma Access are not impacted by this vulnerability. All other versions of PAN-OS are also not impacted.
🐛 ❌ Hackable Intel and Lenovo hardware that went undetected for 5 years won’t ever be fixed
Hardware sold for years by the likes of Intel and Lenovo contains a remotely exploitable vulnerability that will never be fixed. The cause: a supply chain snafu involving an open source software package and hardware from multiple manufacturers that directly or indirectly incorporated it into their products.
🐍 Python's PyPI Reveals Its Secrets
PyPI, short for the Python Package Index, hosts over 20 terabytes of files that are freely available for use in Python projects. If you've ever typed pip install [name of package], it likely pulled that package from PyPI. A lot of people use it too. Whether it's GitHub, PyPI, or others, the report states, "open-source packages make up an estimated 90% of the code run in production today." It's easy to see why that is when these packages help developers avoid the reinvention of millions of wheels every day.
In the 2024 report, GitGuardian reported finding over 11,000 exposed unique secrets, with 1,000 of them being added to PyPI in 2023. That's not much compared to the 12.8 million new secrets added to GitHub in 2023, but GitHub is orders of magnitude larger.
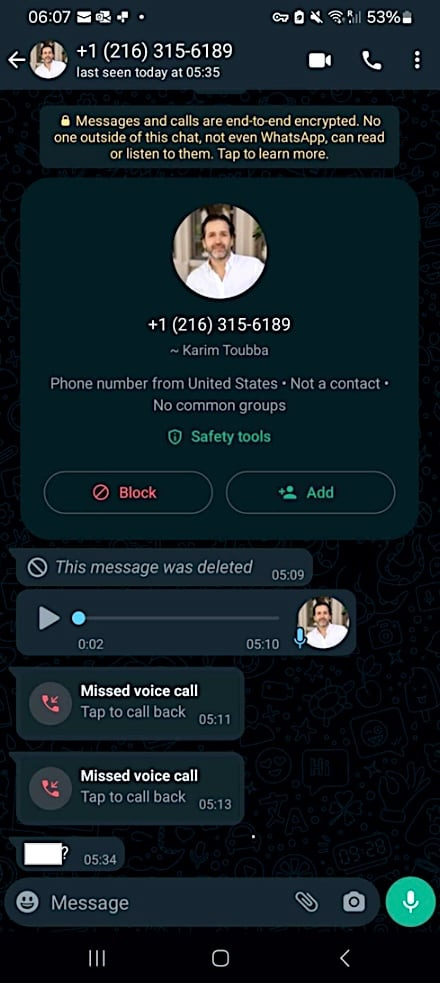
🔓 📺 Over 90,000 LG Smart TVs may be exposed to remote attacks
Security researchers at Bitdefender have discovered four vulnerabilities impacting multiple versions of WebOS, the operating system used in LG smart TVs.
The flaws enable varying degrees of unauthorized access and control over affected models, including authorization bypasses, privilege escalation, and command injection.
The potential attacks hinge on the ability to create arbitrary accounts on the device using a service that runs on ports 3000/3001, which is available for smartphone connectivity, using a PIN.
🐛 🔓 Thousands of Ivanti VPN Appliances Impacted by Recent Vulnerability
The vulnerability, tracked as CVE-2024-21894 (CVSS 8.2), is described as a heap overflow bug in the IPSec component of Ivanti Connect Secure (formerly Pulse Connect Secure) and Policy Secure that could be exploited by remote, unauthenticated attackers to cause a denial-of-service (DoS) condition or execute arbitrary code.
On April 2, Ivanti released software updates to address this flaw and three other vulnerabilities in its two VPN appliances, including CVE-2024-22053, another high-severity heap overflow bug leading to DoS.
🔓 🚪 Over 92,000 exposed D-Link NAS devices have a backdoor account
A threat researcher has disclosed a new arbitrary command injection and hardcoded backdoor flaw in multiple end-of-life D-Link Network Attached Storage (NAS) device models.
The researcher who discovered the flaw, 'Netsecfish,' explains that the issue resides within the'/cgi-bin/nas_sharing.cgi' script, impacting its HTTP GET Request Handler component.
The two main issues contributing to the flaw, tracked as CVE-2024-3273, are a backdoor facilitated through a hardcoded account (username: "messagebus" and empty password) and a command injection problem via the "system" parameter.
When chained together, any attacker can remotely execute commands on the device.
💰 Price of zero-day exploits rises as companies harden products against hackers
[…] startup Crowdfense published its updated price list for these hacking tools, which are commonly known as “zero-days,” because they rely on unpatched vulnerabilities in software that are unknown to the makers of that software. Companies like Crowdfense and one of its competitors Zerodium claim to acquire these zero-days with the goal of re-selling them to other organizations, usually government agencies or government contractors, which claim they need the hacking tools to track or spy on criminals.
Crowdfense is now offering between $5 and $7 million for zero-days to break into iPhones, up to $5 million for zero-days to break into Android phones, up to $3 million and $3.5 million for Chrome and Safari zero-days respectively, and $3 to $5 million for WhatsApp and iMessage zero-days.
Related: Company Offering $30 Million for Android, iOS, Browser Zero-Day Exploits