InfoSec MASHUP - Week 16/2024
Zero-day exploit hits Palo Alto Networks; Delinea Scrambles to Patch Critical Flaw; PuTTY SSH Client Vulnerability; TP-Link Archer AX21 (AX1800) routers hunted; Data stolen from UN Agency;
Partners and affiliates section
🔐 NordVPN’s Spring Sale Campaign (Mar 21 - Jun 12)
Special offer: up to 69% off + 3 months extra.
Breaches & Security Incidents
🔓 🇺🇸 MITRE says state hackers breached its network via Ivanti zero-days
The incident was discovered after suspicious activity was detected on MITRE's Networked Experimentation, Research, and Virtualization Environment (NERVE), an unclassified collaborative network used for research and development.
MITRE has since notified affected parties of the breach, contacted relevant authorities, and is now working on restoring "operational alternatives."
🔓 🌍 ‘Large volume’ of data stolen from UN agency after ransomware attack
Alarge volume of United Nations Development Programme data related to staffers and other internal operations was stolen and posted to a ransomware website in late March, the agency announced this week.
The UNDP issued a statement Tuesday saying that “local IT infrastructure in UN City, Copenhagen, was targeted,” and that a “data extortion actor had stolen data which included certain human resources and procurement information.”
The statement did not detail the kind of data that was stolen from the UN’s lead agency on international development. But notifications shared with affected parties and viewed by CyberScoop said attackers were able to “access a number of servers” and steal “a large volume of data.”
🔓 🇺🇸 Who Stole 3.6M Tax Records from South Carolina?
For nearly a dozen years, residents of South Carolina have been kept in the dark by state and federal investigators over who was responsible for hacking into the state’s revenue department in 2012 and stealing tax and bank account information for 3.6 million people. The answer may no longer be a mystery: KrebsOnSecurity found compelling clues suggesting the intrusion was carried out by the same Russian hacking crew that stole of millions of payment card records from big box retailers like Home Depot and Target in the years that followed.
🇫🇷 ⚕️ 840-bed hospital in France postpones procedures after cyberattack
The Hospital Simone Veil in Cannes (CHC-SV) has announced that it was targeted by a cyberattack on Tuesday morning, severely impacting its operations and forcing staff to go back to pen and paper.
The Hospital announced that it was forced to take all computers offline earlier this week due to a cyberattack, leaving only telephone systems available for communication.
The facility didn't disclose many details about the attack but said it has received no ransom demands by cybercriminals yet.
"The cyberattack is currently being analyzed with the help of expert partners (ANSSI, Cert Santé, Orange CyberDefense, GHT06)," reads the announcement.
"So far, there has been no demand for ransom nor any data theft identified. Investigations are ongoing."
🎰 ⚖️ MGM Resorts sues FTC, agency chair over cyberattack investigation
In the four-count action, MGM also alleges the FTC failed to follow its own conflict-of-interest guidelines.
The lawsuit, filed in U.S. District Court for the District of Columbia, seeks an injunction to stop the FTC from seeking a civil investigative demand in its investigation of MGM related to the cyberattack unless Khan disqualifies herself from the matter. The demand is an administrative subpoena that allows federal agencies to request large amounts of information from private companies without going through court procedures.
🔓 🇺🇸 Cisco Duo warns third-party data breach exposed SMS MFA logs
Duo's homepage reports that it serves 100,000 customers and handles over a billion authentications monthly, with over 10,000,000 downloads on Google Play.
In emails sent to customers, Cisco Duo says an unnamed provider who handles the company's SMS and VOIP multi-factor authentication (MFA) messages was compromised on April 1, 2024.
The notice explains that a threat actor obtained employee credentials through a phishing attack and then used those credentials to gain access to the telephony provider's systems.
The intruder then downloaded SMS and VoIP MFA message logs associated with specific Duo accounts between March 1, 2024, and March 31, 2024.
🔓 🇺🇸 Ransomware gang starts leaking alleged stolen Change Healthcare data
After BlackCat shut down, the affiliate, Notchy, partnered with the RansomHub ransomware gang to extort Change Healthcare once again, even though the company allegedly already paid a ransom.
The threat actor issued a statement on the RansomHub data leak site saying that all the data would be released if Change Healthcare and United Health did not "reach a deal" with them.
Today, a week later, the threat actors have begun to leak screenshots of files they claim were stolen from Change Healthcare during the February ransomware attack.
🔓 🇳🇱 Nexperia IT Breach
Nijmegen -- Nexperia has become aware that an unauthorized third party accessed certain Nexperia IT servers in March 2024.
We promptly took action and disconnected the affected systems from the internet to contain the incident and implemented extensive mitigation. We also launched an investigation with the support of third-party experts to determine the nature and scope of the incident and took strong measures to terminate the unauthorized access.
In addition, we have reported the incident to the competent Authorities, including the ‘Autoriteit Persoonsgegevens’ and the police, and are keeping them informed of the progress of our investigation.
Related: Chipmaker Nexperia confirms breach after ransomware gang leaks data
🔓 🇺🇸 Hacker claims Giant Tiger data breach, leaks 2.8M records online
The threat actor behind the post claims to have uploaded the "full" database of Giant Tiger customer records stolen in March 2024.
"In March 2024, the Canadian discount store chain Giant Tiger Stores Limited... suffered a data breach that exposed over 2.8 million clients," states the threat actor.
"The breach includes over 2.8 million unique email addresses, names, phone numbers and physical addresses."
Cybercrime, Cyber Espionage, APT’s
💰💰 Akira Ransomware Made Over $42 Million in One Year
Since early 2023, Akira ransomware has made over 250 victims worldwide and received more than $42 million in ransom payments, according to CISA, the FBI, Europol, and the Netherlands’ National Cyber Security Centre (NCSC-NL).
Akira ransomware operators have been observed targeting organizations in various industries, including services and goods, manufacturing, education, construction, critical infrastructure, finance, healthcare, and legal sectors.
🇪🇺 ❌ Phishing Platform LabHost Shut Down by Law Enforcement
According to Europol, which coordinated the years-long operation, LabHost infrastructure was compromised and the law enforcement action culminated in several surface web sites being taken down and 37 individuals being arrested between April 14 and April 17.
Investigators searched 70 addresses across the world. The list of arrested individuals includes four from the UK who are believed to have run the site, including LabHost’s original developer.
In addition, 800 of the platform’s alleged users were contacted by law enforcement and notified that they were under active investigation.
🇷🇺 🇺🇸 Notorious Russian hacking unit linked to breach of Texas water facility
Wednesday’s report concludes that Sandworm is behind a set of online personas — including Xaknet, Cyber Army of Russia Reborn and Solntsepek — that have been linked to a string of recent attacks on critical infrastructure, including a water system in Texas. The personas claim the attacks as their own and often exaggerate their impact, while attempting to put distance between the incidents and one of Russia’s most notorious hacking crews.
Sandworm is suspected of controlling the work of a pro-Russian hacktivist group that calls itself the CyberArmyofRussia_Reborn (CARR) that has targeted U.S. water utilities, according to Mandiant. On January 18, the hacktivist group posted a splashy video to Telegram that targeted water tanks in Muleshoe, Texas, appearing to use the human-machine interface (HMI) to turn on the pumps, causing the tank water level to overflow.
Related: Kapeka: A New Backdoor in Sandworm’s Arsenal of Aggression
🇺🇸 ⚖️ Alleged cryptojacking scheme consumed $3.5M of stolen computing to make just $1M
The indictment, filed in US District Court for the Eastern District of New York and unsealed on Monday, charges Charles O. Parks III—45 of Omaha, Nebraska—with wire fraud, money laundering, and engaging in unlawful monetary transactions in connection with the scheme. Parks has yet to enter a plea and is scheduled to make an initial appearance in federal court in Omaha on Tuesday. Parks was arrested last Friday.
Prosecutors allege that Parks defrauded “two well-known providers of cloud computing services” of more than $3.5 million in computing resources to mine cryptocurrency. The indictment says the activity was in furtherance of a cryptojacking scheme, a term for crimes that generate digital coin through the acquisition of computing resources and electricity of others through fraud, hacking, or other illegal means.
Related: Hive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
🇺🇸 ⚖️ Ex-Security Engineer Jailed 3 Years for $12.3 Million Crypto Exchange Thefts
Shakeeb Ahmed, the defendant in question, pled guilty to one count of computer fraud in December 2023 following his arrest in July.
"At the time of both attacks, Ahmed, a U.S. citizen, was a senior security engineer for an international technology company whose resume reflected skills in, among other things, reverse engineering smart contracts and blockchain audits, which are some of the specialized skills Ahmed used to execute the hacks," the U.S. Department of Justice (DoJ) noted at the time.
🇺🇸 🇵🇸 U.S. Treasury Hamas Spokesperson for Cyber Influence Operations
The U.S. Treasury Department's Office of Foreign Assets Control (OFAC) on Friday announced sanctions against an official associated with Hamas for his involvement in cyber influence operations.
Hudhayfa Samir 'Abdallah al-Kahlut, 39, also known as Abu Ubaida, has served as the public spokesperson of Izz al-Din al-Qassam Brigades, the military wing of Hamas, since at least 2007.
"He publicly threatened to execute civilian hostages held by Hamas following the terrorist group's October 7, 2023, attacks on Israel," the Treasury Department said.
Government, Politics, and Privacy
🇺🇦 🦠 Decade-old malware haunts Ukrainian police
More than 100 documents containing potentially confidential information related to government and police activities in Ukraine were uploaded to a publicly accessible repository recently as the result of nearly decade-old malware, an unusual case in which an old and imperfect virus has escaped detection, allowing it to persist and continue to pose a threat.
🇷🇺 🇺🇸 Kremlin-backed actors spread disinformation ahead of US elections
The most prolific of the influence-peddling groups, Microsoft said, is tied to the Russian Presidential Administration, which according to the Marshal Center think tank, is a secretive institution that acts as the main gatekeeper for President Vladimir Putin. The affiliation highlights the “the increasingly centralized nature of Russian influence campaigns,” a departure from campaigns in previous years that primarily relied on intelligence services and a group known as the Internet Research Agency.
“Each Russian actor has shown the capability and willingness to target English-speaking—and in some cases Spanish-speaking—audiences in the US, pushing social and political disinformation meant to portray Ukrainian President Volodymyr Zelensky as unethical and incompetent, Ukraine as a puppet or failed state, and any American aid to Ukraine as directly supporting a corrupt and conspiratorial regime,” the analysts wrote.
Related: After a sleepy primary season, Russia enters 2024 U.S. election fray
Related: US Government Releases Guidance on Securing Election Infrastructure
🇺🇸 😬 Why the US government’s overreliance on Microsoft is a big problem
That state of affairs is unlikely to change even in the wake of a new report by the Cyber Safety Review Board (CSRB), a group of government and industry experts, which lambasts Microsoft for failing to prevent one of the worst hacking incidents in the company’s recent history. The report says Microsoft’s “security culture was inadequate and requires an overhaul.”
Microsoft’s almost untouchable position is the result of several intermingling factors. It is by far the US government’s most important technology supplier, powering computers, document drafting, and email conversations everywhere from the Pentagon to the State Department to the FBI. It is a critical partner in the government’s cyber defense initiatives, with almost unparalleled insights about hackers’ activities and sweeping capabilities to disrupt their operations. And its executives and lobbyists have relentlessly marketed the company as a leading force for a digitally safer world.
🇺🇸 💰 FTC Fines Mental Health Startup Cerebral $7 Million for Major Privacy Violations
The U.S. Federal Trade Commission (FTC) has ordered mental telehealth company Cerebral from using or disclosing personal medical data for advertising purposes.
It has also been fined more than $7 million over charges that it revealed users' sensitive personal health information and other data to third-parties for advertising purposes and failed to honor its easy cancellation policies.
"Cerebral and its former CEO, Kyle Robertson, repeatedly broke their privacy promises to consumers and misled them about the company's cancellation policies," the FTC said in a press statement.
🕵🏻♂️ 💰 A Spy Site Is Scraping Discord and Selling Users’ Messages
An online service is scraping Discord servers en masse, archiving and tracking users’ messages and activity across servers including what voice channels they join, and then selling access to that data for as little as $5. Called Spy Pet, the service’s creator says it scrapes more than ten thousand Discord servers, and besides selling access to anyone with cryptocurrency, is also offering the data for training AI models or to assist law enforcement agencies, according to its website.
🇬🇧 👺 New UK law targets “despicable individuals” who create AI sex deepfakes
On Tuesday, the UK government announced a new law targeting the creation of AI-generated sexually explicit deepfake images. Under the legislation, which has not yet been passed, offenders would face prosecution and an unlimited fine, even if they do not widely share the images but create them with the intent to distress the victim. The government positions the law as part of a broader effort to enhance legal protections for women.
ICS & OT
Malware & Threats
🎣 🔓 LastPass users targeted in phishing attacks good enough to trick even the savvy
Password-manager LastPass users were recently targeted by a convincing phishing campaign that used a combination of email, SMS, and voice calls to trick targets into divulging their master passwords, company officials said.
The attackers used an advanced phishing-as-a-service kit discovered in February by researchers from mobile security firm Lookout. Dubbed CryptoChameleon for its focus on cryptocurrency accounts, the kit provides all the resources needed to trick even relatively savvy people into believing the communications are legitimate. Elements include high-quality URLs, a counterfeit single sign-on page for the service the target is using, and everything needed to make voice calls or send emails or texts in real time as targets are visiting a fake site. The end-to-end service can also bypass multi-factor authentication in the event a target is using the protection.
🎣 💸 Google ad impersonates Whales Market to push wallet drainer malware
A legitimate-looking Google Search advertisement for the crypto trading platform 'Whales Market' redirects visitors to a wallet-draining phishing site that steals all of your assets.
Whales Market is a decentralized OTC trading platform allowing users to exchange assets across blockchains.
This phishing site replicates the legitimate website, including its trading platform. Once you connect your wallet, though, malicious scripts will drain it of all assets.
💥💥 Attackers are pummeling networks around the world with millions of login attempts
Attacks coming from nearly 4,000 IP addresses take aim at VPNs, SSH and web apps.
📥 🦠 After XZ Utils, More Open-Source Maintainers Under Attack
The OpenJS Foundation reports being recently targeted by a social engineering attack reminiscent of the malicious subversion of XZ Utils discovered last month. The foundation promotes and hosts 35 critical JavaScript projects - including Appium, Dojo, jQuery, Node.js and webpack - used by many of the world's websites and their billions of users.
Members of the OpenJS Foundation Cross Project Council recently "received a suspicious series of emails with similar messages, bearing different names and overlapping GitHub-associated emails," says a joint statement issued by the Open Source Security Foundation and the OpenJS Foundation.
💸 ❌ A crypto wallet maker’s warning about an iMessage bug sounds like a false alarm
A crypto wallet maker claimed this week that hackers may be targeting people with an iMessage “zero-day” exploit — but all signs point to an exaggerated threat, if not a downright scam.
Trust Wallet’s official X (previously Twitter) account wrote that “we have credible intel regarding a high-risk zero-day exploit targeting iMessage on the Dark Web. This can infiltrate your iPhone without clicking any link. High-value targets are likely. Each use raises detection risk.”
🦠 🌁 New SteganoAmor attacks use steganography to target 320 orgs globally
A new campaign conducted by the TA558 hacking group is concealing malicious code inside images using steganography to deliver various malware tools onto targeted systems.
TA558 is a threat actor that has been active since 2018, known for targeting hospitality and tourism organizations worldwide, focusing on Latin America.
The attacks begin with malicious emails containing seemingly innocuous document attachments (Excel and Word files) that exploit the CVE-2017-11882 flaw, a commonly targeted Microsoft Office Equation Editor vulnerability fixed in 2017.
🦠 🇨🇳 Chinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
"The latest iteration of LightSpy, dubbed 'F_Warehouse,' boasts a modular framework with extensive spying features," the BlackBerry Threat Research and Intelligence Team said in a report published last week.
There is evidence to suggest that the campaign may have targeted India based on VirusTotal submissions from within its borders.
🦠 🚪 Hackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
Threat actors have been exploiting the newly disclosed zero-day flaw in Palo Alto Networks PAN-OS software dating back to March 26, 2024, nearly three weeks before it came to light yesterday [Apr. 12].
The security vulnerability, tracked as CVE-2024-3400 (CVSS score: 10.0), is a command injection flaw that enables unauthenticated attackers to execute arbitrary code with root privileges on the firewall.
It's worth noting that the issue is applicable only to PAN-OS 10.2, PAN-OS 11.0, and PAN-OS 11.1 firewall configurations that have GlobalProtect gateway and device telemetry enabled.
Related:
Palo Alto Networks zero-day exploited since March to backdoor firewalls
Palo Alto Networks Releases Fixes for Firewall Zero-Day as First Attribution Attempts Emerge
Palo Alto Networks’ firewall bug under attack brings fresh havoc to thousands of companies
22,500 Palo Alto firewalls "possibly vulnerable" to ongoing attacks
➝ Great Analysis by the watchTowr Labs team! ★
AI, Tech & Tools
🤦🏻♂️ Microsoft’s VASA-1 can deepfake a person with one photo and one audio track
On Tuesday, Microsoft Research Asia unveiled VASA-1, an AI model that can create a synchronized animated video of a person talking or singing from a single photo and an existing audio track. In the future, it could power virtual avatars that render locally and don't require video feeds—or allow anyone with similar tools to take a photo of a person found online and make them appear to say whatever they want.
While the Microsoft researchers tout potential positive applications like enhancing educational equity, improving accessibility, and providing therapeutic companionship, the technology could also easily be misused. For example, it could allow people to fake video chats, make real people appear to say things they never actually said (especially when paired with a cloned voice track), or allow harassment from a single social media photo.
🤖 🔐 Five Eyes Agencies Release New AI Security Guidance
The joint guidance, announced this week, expands on previous work and outlines methodologies for protecting data and AI systems.
While the guidance is intended for national security purposes, the information can be used by any organization and it can be particularly useful to those with high-risk/high-value environments.
The document focuses on securing the deployment environment, continuously protecting the AI system, and secure AI operation and maintenance.
🇨🇳 💬 Apple deletes WhatsApp, Threads from China app store on orders from Beijing
“We are obligated to follow the laws in the countries where we operate, even when we disagree,” an Apple spokesperson told CNN on Friday. “The Cyberspace Administration of China ordered the removal of these apps from the China storefront based on their national security concerns. These apps remain available for download on all other storefronts where they appear.”
🔓 ☁️ AWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
The vulnerability has been codenamed LeakyCLI by cloud security firm Orca.
"Some commands on Azure CLI, AWS CLI, and Google Cloud CLI can expose sensitive information in the form of environment variables, which can be collected by adversaries when published by tools such as GitHub Actions," security researcher Roi Nisimi said in a report shared with The Hacker News.
Microsoft has since addressed the issue as part of security updates released in November 2023, assigned it the CVE identifier CVE-2023-36052 (CVSS score: 8.6).
🐛 🔑 Widely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
The maintainers of the PuTTY Secure Shell (SSH) and Telnet client are alerting users of a critical vulnerability impacting versions from 0.68 through 0.80 that could be exploited to achieve full recovery of NIST P-521 (ecdsa-sha2-nistp521) private keys.
The flaw has been assigned the CVE identifier CVE-2024-31497, with the discovery credited to researchers Fabian Bäumer and Marcus Brinkmann from the Ruhr University Bochum.
"The effect of the vulnerability is to compromise the private key," the PuTTY project said in an advisory.
Vulnerabilities, Research, and Threat Intelligence
🐛 🔓 CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
"CrushFTP v11 versions below 11.1 have a vulnerability where users can escape their VFS and download system files," CrushFTP said in an advisory released Friday. "This has been patched in v11.1.0."
That said, customers who are operating their CrushFTP instances within a DMZ (demilitarized zone) restricted environment are protected against the attacks.
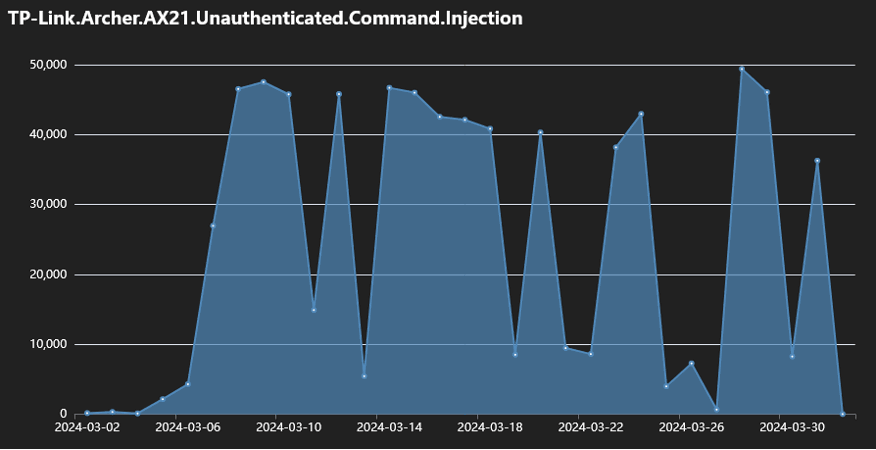
🤖 🛜 Multiple botnets exploiting one-year-old TP-Link flaw to hack routers
At least six distinct botnet malware operations are hunting for TP-Link Archer AX21 (AX1800) routers vulnerable to a command injection security issue reported and addressed last year.
Tracked as CVE-2023-1389, the flaw is a high-severity unauthenticated command injection problem in the locale API reachable through the TP-Link Archer AX21 web management interface.
🩹 😬 Delinea Scrambles to Patch Critical Flaw After Failed Responsible Disclosure Attempt
On April 12, Delinea informed customers that it had started investigating a “security incident” and that there may be some service disruptions.
The next day, the company clarified that it had become aware of a critical authentication bypass vulnerability in the Secret Server SOAP API. Delinea initially prevented exploitation by blocking the impacted SOAP endpoints for Secret Server Cloud customers. In addition, it released indicators of compromise (IoCs) to enable customers to detect potential exploitation attempts.
🩹 Intel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
While the original shortcoming was discovered and patched by the Lighttpd maintainers way back in August 2018 with version 1.4.51, the lack of a CVE identifier or an advisory meant that it was overlooked by developers of AMI MegaRAC BMC, ultimately ending up in products made by Intel and Lenovo.
The silent fix for Lighttpd concerns an out-of-bounds read vulnerability that could be exploited to exfiltrate sensitive data, such as process memory addresses, thereby allowing threat actors to bypass crucial security mechanisms like address space layout randomization (ASLR).
🔓 🔑 Crickets from Chirp Systems in Smart Lock Key Leak
The U.S. government is warning that “smart locks” securing entry to an estimated 50,000 dwellings nationwide contain hard-coded credentials that can be used to remotely open any of the locks. The lock’s maker Chirp Systems remains unresponsive, even though it was first notified about the critical weakness in March 2021. Meanwhile, Chirp’s parent company, RealPage, Inc., is being sued by multiple U.S. states for allegedly colluding with landlords to illegally raise rents.