InfoSec MASHUP - Week 17/2024
China spies in Germany; State-sponsored criminals exploiting Cisco 0-day flaws; Russian group claims attack on US wastewater plant; Change Healthcare saga continues; Samourai went down;
Partners and affiliates section
🔐 NordVPN’s Spring Sale Campaign (Mar 21 - Jun 12)
Special offer: up to 69% off + 3 months extra.
Breaches & Security Incidents
🔓 🇺🇸 Cyberattack hits Georgia county at center of voting software breach
In a statement Friday, the Coffee County Board of Commissioners said that the county was notified by the Cybersecurity and Infrastructure Security Agency on April 15 about unusual cyber activity in Coffee County’s IT infrastructure.
“Upon examination, Coffee County’s IT infrastructure showed no evidence of exfiltration of data/files, but did indicate cyber-activity by an unknown malicious actor,” the county board said, adding that it declared a cyber incident and took steps to secure its systems.
🔓 🇺🇸 Kaiser Permanente: Data breach may impact 13.4 million patients
“Kaiser Permanente has determined that certain online technologies, previously installed on its websites and mobile applications, may have transmitted personal information to third-party vendors Google, Microsoft Bing, and X (Twitter) when members and patients accessed its websites or mobile applications” - Kaiser Permanente
🇨🇳 🇩🇪 China hacked Volkswagen: Threat actors associated with the Chinese government are believed to have hacked into Volkswagen systems in an effort to steal valuable data, according to an investigation by German news outlets. Hackers had access to the carmaker’s systems between 2011 and 2014 and stole thousands of documents, including ones related to engines and transmissions. Volkswagen confirmed the intrusion, but said it has since improved the security of its systems [H/T SecurityWeek].
🔓 🇺🇸 Ransomware Gang Leaks Data Allegedly Stolen From Government Contractor
The group claims to be in the possession of 800Gb of data pertaining to DISB, the US Securities and Exchange Commission (SEC), Delaware banking institutions, and other financial entities, and threatens to release it unless DISB pays a ransom.
The data appears to have been stolen from DISB’s STAR system client in late March, during a cyberattack on Tyler Technologies, a software and services provider for the public sector.
🔓 🇺🇸 Stolen Change Healthcare data could contain information on ‘a substantial portion’ of Americans
Nearly two dozen screenshots purportedly from roughly 4 terabytes of Change Healthcare data were posted April 7 to the website operated by RansomHub, a website whose operators either auction off previously hacked data or conduct attacks themselves. RansomHub gave Change Healthcare until April 20 to buy the data before it was to be sold to the highest bidder.
The screenshots, viewed by CyberScoop on April 15, included alleged partner agreements between Change Healthcare and other companies, invoices, Medicare claims data, individual patient records, an audit and other material.
Related: UnitedHealth Says Patient Data Exposed in Change Healthcare Cyberattack
Related: UnitedHealth confirms it paid ransomware gang to stop data leak
🔓 🇮🇹 Synlab Italia suspends operations following ransomware attack
Late last week, the company announced that it had suffered a security breach in the early hours of April 18, which forced it to shut down all computers to limit the damaging activity.
"As soon as they became aware, the IT department proceeded to exclude the entire corporate infrastructure from the network and to shut down all the machines in compliance with the company's IT security procedures," reads the company's announcement.
Although the company has not confirmed, some sensitive medical data may have been exposed to the attackers.
Cybercrime, Cyber Espionage, APT’s
💥💥 WP Automatic WordPress plugin hit by millions of SQL injection attacks
Hackers have started to target a critical severity vulnerability in the WP Automatic plugin for WordPress to create user accounts with administrative privileges and to plant backdoors for long-term access.
Currently installed on more than 30,000 websites, WP Automatic lets administrators automate content importing (e.g. text, images, video) from various online sources and publishing on their WordPress site.
The exploited vulnerability is identified as as CVE-2024-27956 and received a severity score of 9.9/10.
🇺🇸 DOJ Arrests Founders of Crypto Mixer Samourai for $2 Billion in Illegal Transactions
The U.S. Department of Justice (DoJ) on Wednesday announced the arrest of two co-founders of a cryptocurrency mixer called Samourai and seized the service for allegedly facilitating over $2 billion in illegal transactions and for laundering more than $100 million in criminal proceeds.
To that end, Keonne Rodriguez, 35, and William Lonergan Hill, 65, have been charged with conspiracy to commit money laundering and conspiracy to operate an unlicensed money transmitting business from 2015 through February 2024. Rodriguez and Hill face a maximum sentence of 25 years in prison each.
🇰🇵 🇰🇷 DPRK hacking groups breach South Korean defense contractors
The police discovered several instances of successful breaches of defense companies in South Korea involving the hacking groups Lazarus, Andariel, and Kimsuky, all part of the North Korean hacking apparatus.
According to the announcement, the attackers breached the organizations by leveraging vulnerabilities in targets' or their subcontractors' environments to plant malware capable to exfiltrate data.
🇷🇺 🇺🇸 Russian hacking group claims responsibility for cyberattack on Indiana wastewater plant
A video by a Russian hacking group claiming responsibility for last week’s cyberattack on Tipton West Wastewater Treatment Plant in Indiana surfaced on social media Thursday. It’s evidence of the latest cyberattack by nation state cybercriminals targeting water facilities in small towns across the United States.
The “People’s Cyber Army of Russia” took credit last Saturday for the incident on the messaging app Telegram. A message accompanying the video read: “We continue to look partially cover our series of work on US infrastructure. Today, we’ll look at Indiana. Let’s consider the work on municipal water treatment plants. Enjoy watching, friends.”
🕵🏻♂️ ArcaneDoor hackers exploit Cisco zero-days to breach govt networks
The hackers, identified as UAT4356 by Cisco Talos and STORM-1849 by Microsoft, began infiltrating vulnerable edge devices in early November 2023 in a cyber-espionage campaign tracked as ArcaneDoor.
Even though Cisco has not yet identified the initial attack vector, it discovered and fixed two security flaws—CVE-2024-20353 (denial of service) and CVE-2024-20359 (persistent local code execution)—that the threat actors used as zero-days in these attacks.
Cisco became aware of the ArcaneDoor campaign in early January 2024 and found evidence that the attackers had tested and developed exploits to target the two zero-days since at least July 2023.
Related: Nation-state hackers exploit Cisco firewall 0-days to backdoor government networks

🇩🇪 🇨🇳 German Authorities Issue Arrest Warrants for Three Suspected Chinese Spies
The full names of the defendants were not disclosed by the Office of the Federal Prosecutor (aka Generalbundesanwalt), but it includes Herwig F., Ina F., and Thomas R.
"The suspects are strongly suspected of working for a Chinese secret service since an unspecified date before June 2022," the Generalbundesanwalt said.
Thomas R. is believed to have acted as an agent for China's Ministry of State Security (MSS), gathering information about innovative technologies in Germany that could be used for military purposes.
🇷🇺 🇺🇦 Russian Sandworm hackers targeted 20 critical orgs in Ukraine
The attacks occurred in March and in some cases the hackers were able to infiltrate the targeted network by poisoning the supply chain to deliver compromised or vulnerable software, or through the software provider's ability to access organization's systems for maintenance and technical support.
🇷🇺 🇺🇸 Russian FSB Counterintelligence Chief Gets 9 Years in Cybercrime Bribery Scheme
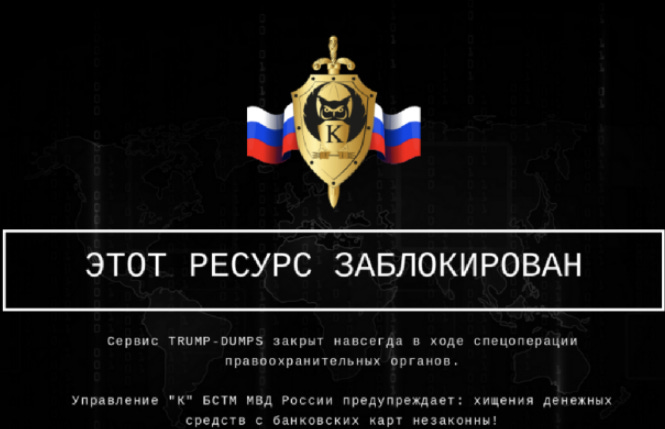
The head of counterintelligence for a division of the Russian Federal Security Service (FSB) was sentenced last week to nine years in a penal colony for accepting a USD $1.7 million bribe to ignore the activities of a prolific Russian cybercrime group that hacked thousands of e-commerce websites. The protection scheme was exposed in 2022 when Russian authorities arrested six members of the group, which sold millions of stolen payment cards at flashy online shops like Trump’s Dumps.
🇷🇺 🦠 Windows vulnerability reported by the NSA exploited to install Russian malware
When Microsoft patched the vulnerability in October 2022—at least two years after it came under attack by the Russian hackers—the company made no mention that it was under active exploitation. As of publication, the company’s advisory still made no mention of the in-the-wild targeting. Windows users frequently prioritize the installation of patches based on whether a vulnerability is likely to be exploited in real-world attacks.
On Monday, Microsoft revealed that a hacking group tracked under the name Forest Blizzard has been exploiting CVE-2022-38028 since at least June 2020—and possibly as early as April 2019. The threat group—which is also tracked under names including APT28, Sednit, Sofacy, GRU Unit 26165, and Fancy Bear—has been linked by the US and the UK governments to Unit 26165 of the Main Intelligence Directorate, a Russian military intelligence arm better known as the GRU. Forest Blizzard focuses on intelligence gathering through the hacking of a wide array of organizations, mainly in the US, Europe, and the Middle East.
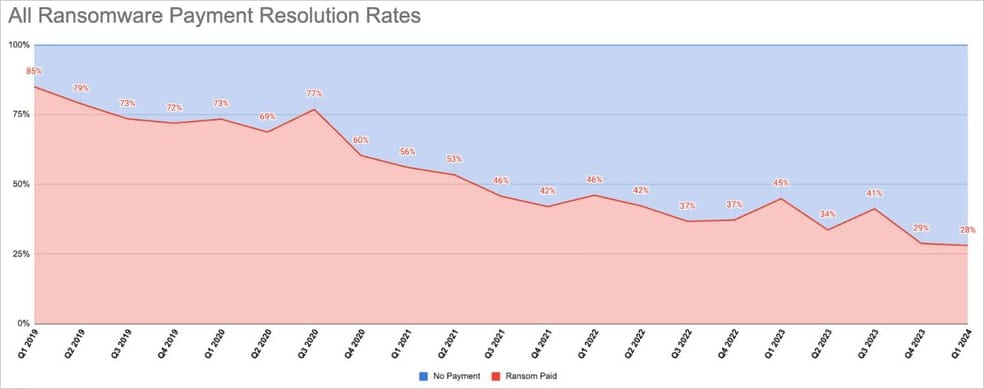
💸 ⬇️ Ransomware payments drop to record low of 28% in Q1 2024
This figure was 29% in Q4 2023, and Coveware's stats show that diminishing payments have remained steady since early 2019.
This decrease is due to organizations implementing more advanced protective measures, mounting legal pressure not to meet the crooks' financial demands, and cybercriminals repeatedly breaching promises not to publish or resale stolen data if a ransom is paid.
Government, Politics, and Privacy
🇺🇸 💸 CISA ransomware warning program has sent out more than 2,000 alerts
“The warning pilot is focused on reducing the prevalence of ransomware by using our vulnerability scanning tools to let businesses know if they have vulnerabilities that need to be patched,” Easterly said at an event hosted by the Institute for Security and Technology.
Easterly said that since the pilot was launched in January of last year, it has expanded to include CISA’s database of known exploited vulnerabilities as well as common misconfigurations that can be linked to ransomware attacks.
🇺🇸 👀 U.S. Imposes Visa Restrictions on 13 Linked to Commercial Spyware Misuse
The U.S. Department of State on Monday said it's taking steps to impose visa restrictions on 13 individuals who are allegedly involved in the development and sale of commercial spyware or who are immediately family members of those involved in such businesses.
"These individuals have facilitated or derived financial benefit from the misuse of this technology, which has targeted journalists, academics, human rights defenders, dissidents and other perceived critics, and U.S. Government personnel," the department said.
Related: Spain Reopens a Probe Into a Pegasus Spyware Case After a French Request to Work Together
🇮🇷 🇺🇸 Iranian nationals charged with hacking U.S. companies, Treasury and State departments
$10 million rewards offered for information regarding the accused, who are allegedly connected to a pair of IRGC front companies.
The Biden administration should adopt less-strict standards about what triggers a proposed prohibition on data brokers selling bulk sensitive information to adversarial foreign entities, industry groups argued in public comments due last week.
Among their biggest suggestions is that any potential rules should make exceptions for anonymized data. Another is that they should raise the volume threshold for what counts as bulk information.
ICS & OT
🐛 🔓 Siemens Industrial Product Impacted by Exploited Palo Alto Firewall Vulnerability
In an advisory published late last week, Siemens revealed that its Ruggedcom APE1808 devices configured with a Palo Alto Networks virtual next-generation firewall (NGFW) could be affected by CVE-2024-3400.
Siemens is preparing updates for the affected product and in the meantime has provided workarounds and mitigations.
Malware & Threats
🦠 👀 Researchers sinkhole PlugX malware server with 2.5 million unique IPs
Since last September, the sinkhole server received over 90,000 requests every day from infected hosts in more than 170 countries.
Since September 2023, when Sekoia captured the unique IP address associated with the particular C2, it has logged over 2,495,297 unique IPs from 170 countries interacting with its sinkhole.
This action enabled the security firm to analyze traffic, map infections, prevent malicious exploitation of clients, and devise effective disinfection plans.
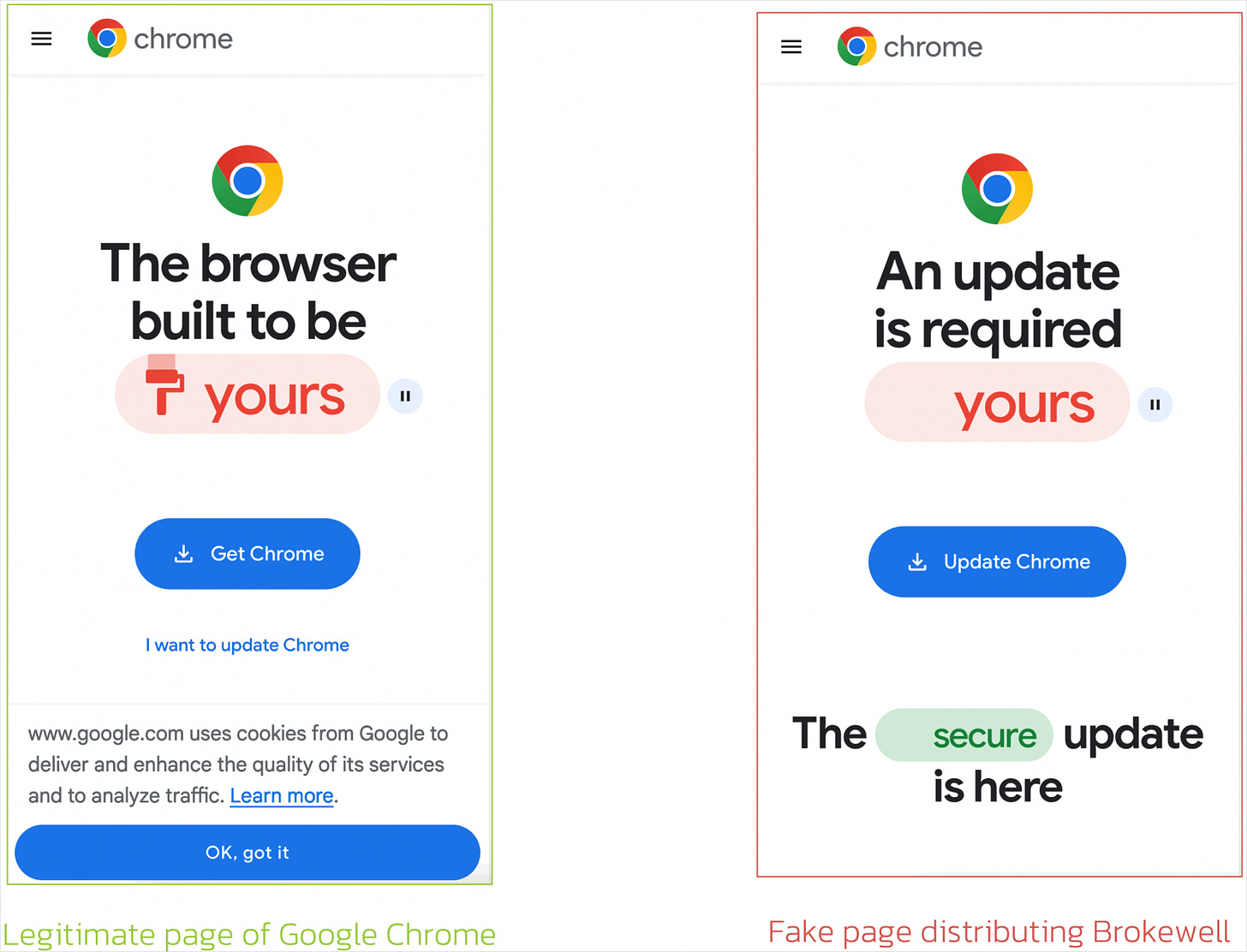
🦠 🤖 New Brokewell malware takes over Android devices, steals data
Security researchers have discovered a new Android banking trojan they named Brokewell that can capture every event on the device, from touches and information displayed to text input and the applications the user launches.
The malware is delivered through a fake Google Chrome update that is shown while using the web browser. Brokewell is under active development and features a mix of extensive device takeover and remote control capabilities.
🦠 🇷🇺 Russia's APT28 Exploited Windows Print Spooler Flaw to Deploy 'GooseEgg' Malware
According to new findings from the tech giant's threat intelligence team, APT28 – also called Fancy Bear and Forest Blizzard (formerly Strontium) – weaponized the bug in attacks targeting Ukrainian, Western European, and North American government, non-governmental, education, and transportation sector organizations.
AI, Tech & Tools
🍪 Google Postpones Third-Party Cookie Deprecation Amid U.K. Regulatory Scrutiny
Google has once again pushed its plans to deprecate third-party tracking cookies in its Chrome web browser as it works to address outstanding competition concerns from U.K. regulators over its Privacy Sandbox initiative.
Privacy Sandbox refers to a set of initiatives that offers privacy-preserving alternatives to tracking cookies and cross-app identifiers in order to serve tailored ads to users.
🤖 ⚖️ School athletic director arrested for framing principal using AI voice synthesis
On Thursday, Baltimore County Police arrested Pikesville High School's former athletic director, Dazhon Darien, and charged him with using AI to impersonate Principal Eric Eiswert, according to a report by The Baltimore Banner. Police say Darien used AI voice synthesis software to simulate Eiswert's voice, leading the public to believe the principal made racist and antisemitic comments.
🤖 🇻🇦 Cisco Systems Joins Microsoft, IBM in Vatican Pledge to Ensure Ethical Use and Development of AI
Cisco Systems chief executive Chuck Robbins signed the document, known as the Rome Call, and met privately with Pope Francis, the Vatican said.
The pledge outlines key pillars of ethical and responsible use of AI. It emphasizes that AI systems must be designed, used and regulated to serve and protect the dignity of all human beings, without discrimination, and their environments. It highlights principles of transparency, inclusion, responsibility, impartiality and security as necessary to guide all AI developments.
📨 Proton has introduced Dark Web Monitoring for credential leaks for everyone with a paid Proton plan. Dark Web Monitoring scans hidden parts of the internet for Proton Mail email addresses that have ended up in illegal data markets.
Vulnerabilities, Research, and Threat Intelligence
🪱 Researchers develop malicious AI ‘worm’ targeting generative AI systems
Researchers have created a new, never-seen-before kind of malware they call the “Morris II” worm, which uses popular AI services to spread itself, infect new systems and steal data. The name references the original Morris computer worm that wreaked havoc on the internet in 1988.
The worm demonstrates the potential dangers of AI security threats and creates a new urgency around securing AI models.
🐛 🩹 Maximum severity Flowmon bug has a public exploit, patch now
Proof-of-concept exploit code has been released for a top-severity security vulnerability in Progress Flowmon, a tool for monitoring network performance and visibility.
The security issue has the maximum severity score of 10/10 and was discovered by researchers at Rhino Security Labs. It is currently tracked as CVE-2024-2389.
An attacker can exploiting the vulnerability can use a specially crafted API request to gain remote, unauthenticated access to the Flowmon web interface and execute arbitrary system commands.
🧠 Research Shows How Attackers Can Abuse EDR Security Products
Looking to prove that this is indeed possible, SafeBreach security researcher Shmuel Cohen dissected the inner workings of Palo Alto Networks’ Cortex extended detection and response (XDR) platform to identify weaknesses that could allow him to abuse the security tool. The issues were addressed by the vendor several months ago.
🦠🦠 Hackers infect users of antivirus service that delivered updates over HTTP
Hackers abused an antivirus service for five years in order to infect end users with malware. The attack worked because the service delivered updates over HTTP, a protocol vulnerable to attacks that corrupt or tamper with data as it travels over the Internet.
The unknown hackers, who may have ties to the North Korean government, pulled off this feat by performing a man-in-the-middle (MiitM) attack that replaced the genuine update with a file that installed an advanced backdoor instead, said researchers from security firm Avast today.