[InfoSec MASHUP] Week 24/2024
165 Snowflake customers compromised; MSFT decided to disable & delay controversial Recall feat.; 23andMe under scrutiny in Canada & UK; Cylance confirms breach via 3rd party; Patch Tuesday;
Partners and Affiliates
🔐 NordVPN x Saily (Jun 12 - Aug 7) ✈️
Save up to 73% + get free travel data! Users buying a 2-year NordVPN plan will get up to 20GB of free travel data from Saily:
Basic plan - 1GB; Standard & Plus plans - 3GB; Complete plan - 10GB; Ultimate plan - 20GB
Claim your gift right away. New NordVPN users will be able to claim their Saily travel data using a coupon code via the Saily app.
Breaches & Security Incidents
🔓 🇺🇸 Keytronic, a major manufacturer of electronic devices, confirmed a data breach after the ransomware group BlackCat (ALPHV) leaked stolen files. The breach was acknowledged in a Form 8-K filing with the U.S. Securities and Exchange Commission (SEC). Keytronic discovered unauthorized activity in late March 2023 and subsequently notified law enforcement and launched an investigation with cybersecurity experts. The company reported that the attackers gained access to certain internal systems and exfiltrated data, including personal information of employees and business information.
🔓 🇺🇸 Ascension, a significant U.S. healthcare provider, has confirmed a ransomware attack resulting in the theft of personal health information (PHI). The breach was discovered on May 25, 2024, when Ascension detected unusual activity within its network. The attack led to the compromise of patient data, including names, addresses, dates of birth, medical records, and Social Security numbers.
🔓 🇺🇸 The New York Times has warned its freelancers about a data breach involving their personal information, which was exposed due to a security incident with a third-party service on GitHub. This breach potentially compromised sensitive data, including payment details and Social Security numbers. The publication urged freelancers to monitor their financial accounts for any suspicious activity and to take precautionary measures to protect their information.
🔓 🇺🇸 Life360, the parent company of Tile, confirmed a data breach that led to an extortion attempt by a hacker. The breach affected data associated with Tile, a popular tracking device company acquired by Life360 in 2021. The hacker obtained data from Tile's servers and demanded a ransom from Life360 to prevent the release of this information. The data exposed included Tile user information but did not compromise any financial data or location history. Life360 has since taken steps to secure its systems and is working with law enforcement to address the situation.
🔓 TechCrunch reports on the mystery surrounding an alleged data breach of a data broker. The breach came to light when a hacker with a history of selling stolen data claimed to have billions of records affecting at least 300 million people. The hacker posted samples of the data, including names, addresses, and social security numbers, but the data broker in question denies any breach occurred. Despite the denial, experts note the data appears authentic and could cause significant harm if sold on the dark web. Investigations are ongoing to verify the claims and understand the potential impact.
🔓 🇺🇸 Arlington, Massachusetts, fell victim to a cyberattack, losing nearly $446,000 through a business email compromise. Cybercriminals used phishing and spoofing techniques to impersonate a vendor for a high school construction project. They convinced town employees to switch payment methods, leading to four fraudulent wire transfers between October and January. Upon discovering the fraud in February, Arlington reported the incident and launched an investigation. While the town recovered a small portion of the funds, it pledged to bolster its cybersecurity defenses.
🔓 🇺🇸 Cylance has confirmed a data breach involving its third-party platform, Fortra's GoAnywhere MFT. The incident exposed some personal information, including names, addresses, and email addresses of customers. The breach occurred due to vulnerabilities in the Fortra platform, which were promptly patched. Cylance, now part of BlackBerry, is collaborating with authorities to investigate and mitigate the impact, emphasizing that its core products and systems were not affected. Affected individuals are being notified directly.
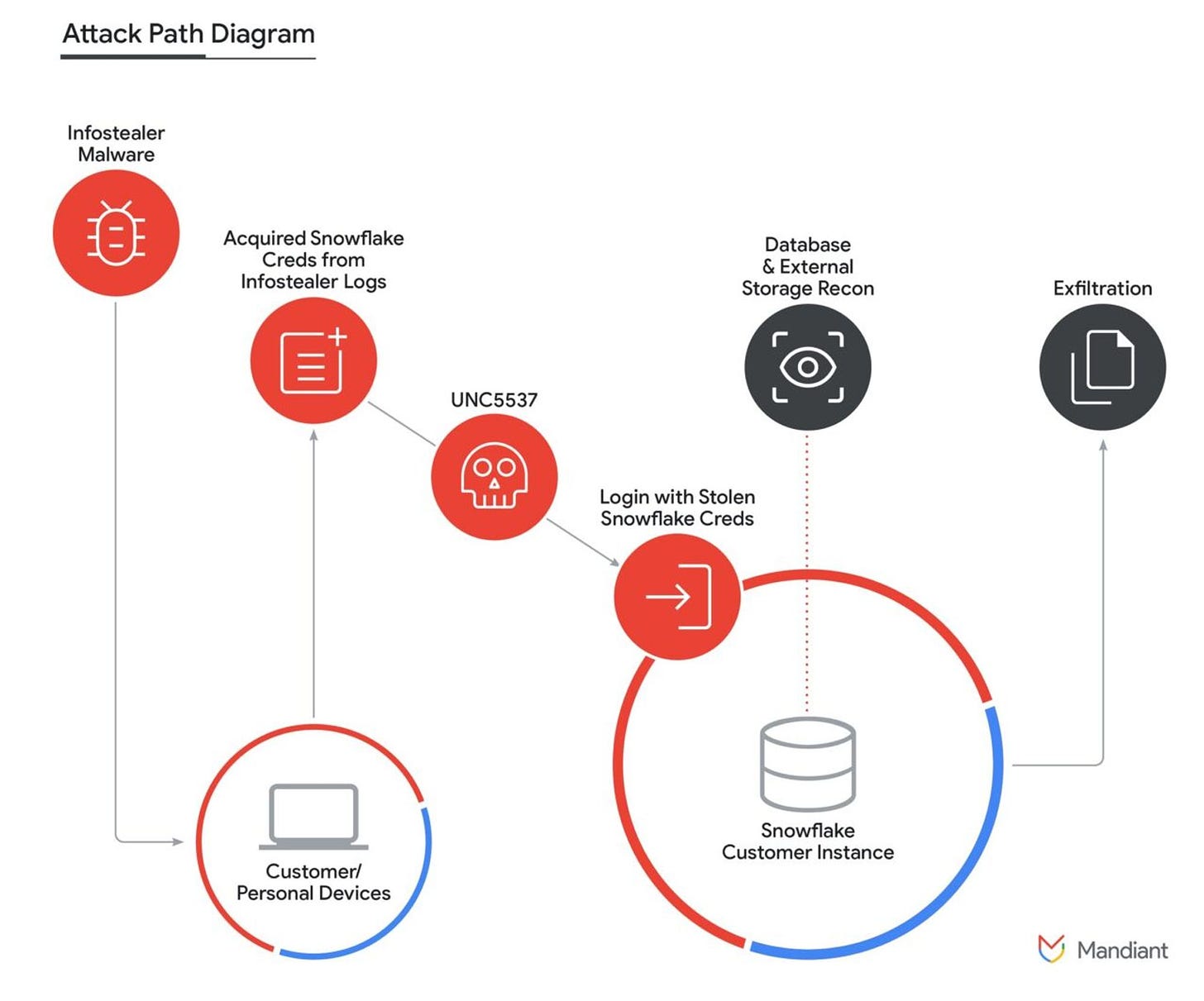
🔓 ❄️ As many as 165 Snowflake customers have been compromised through login credentials stolen by infostealer malware. Notable affected companies include Lending Tree's QuoteWizard, TicketMaster, and Santander. The breaches resulted from a lack of multifactor authentication (MFA), outdated credentials, and the absence of network allow lists. The attackers, tracked as UNC5537 and primarily based in North America, used credentials from malware logs dating back to 2020. They accessed Snowflake accounts via web interfaces and a custom utility called FrostBite. Mandiant, investigating the breaches, stressed the need for robust MFA, credential monitoring, and secure authentication practices to prevent such incidents.
🇬🇧 🇨🇦 Privacy watchdogs in the U.K. and Canada have launched a joint investigation into the data breach at 23andMe, which last year compromised the genetic and ancestry data of 6.9 million users. The breach, undetected for five months, involved hackers accessing around 14,000 accounts via password spraying and scraping data from millions due to an opt-in feature called DNA Relatives. The investigation by the U.K.’s Information Commissioner’s Office (ICO) and Canada’s Office of the Privacy Commissioner (OPC) will assess the extent of the exposed information, the adequacy of 23andMe’s data protection measures, and their notification practices. 23andMe has not commented on the investigation.
Cybercrime, Cyber Espionage, APT’s
🇰🇵 🇧🇷 North Korean hackers, identified as the Lazarus Group, have been targeting Brazilian healthcare entities in a recent campaign. The attackers are deploying a new variant of the sophisticated malware known as "NukeSped" to infiltrate systems and extract sensitive information. This campaign highlights an ongoing trend where North Korean cyber espionage groups expand their focus beyond traditional targets to include healthcare sectors worldwide, aiming to gather intelligence and potentially disrupt operations.
💬 On June 12, BreachForums reappeared on clearnet and Tor. BreachForums back online — or it is a honeypot?
0️⃣ 🔓 The Black Basta ransomware gang has been linked to exploiting a Windows zero-day vulnerability, allowing them to execute attacks before the flaw was publicly disclosed or patched. This connection emphasizes the gang's sophistication and access to advanced techniques for breaching systems. The details of the exploited zero-day and the methods used underline the increasing threats posed by ransomware groups that leverage unknown or unpatched vulnerabilities to target organizations effectively.
🇺🇦 👮🏻♂️ The Ukraine cyber police arrested a ransomware crypter specialist associated with the Conti and LockBit ransomware groups. The suspect, who has ties to these notorious cybercriminal organizations, allegedly provided encryption tools that facilitated ransomware attacks. These groups have been responsible for numerous high-profile cyberattacks globally, leading to significant financial and operational damages. The arrest marks a significant step in international efforts to combat ransomware operations and disrupt the activities of major cybercriminal networks.
🇨🇳 China's state-sponsored hackers have infected around 20,000 Fortinet VPN devices, according to the Dutch intelligence agency AIVD. The campaign, attributed to the Chinese group APT5, targets sensitive sectors, including critical infrastructure, to steal data and maintain long-term access. Fortinet has urged users to update their systems to mitigate the risk.
The state actor installed malware at relevant targets at a later date. This gave the state actor permanent access to the systems. Even if a victim installs security updates from FortiGate, the state actor continues to have this access.
Government, Politics, and Privacy
🇺🇸 🤖 On Thursday [Jun 13, 2024], the U.S. government, led by the Cybersecurity and Infrastructure Security Agency (CISA), conducted its first tabletop exercise focused on artificial intelligence (AI) incident response. This initiative, part of the Joint Cyber Defense Collaborative (JCDC), involved 50 AI experts from 15 companies and various international cyber defense agencies. The exercise aimed to prepare for potential AI-related cybersecurity incidents, understand the necessary information-sharing protocols, and enhance collaboration between the public and private sectors.
The four-hour exercise is a precursor to the development of CISA’s AI security incident collaboration playbook, which will outline AI-specific incident response strategies. Set to be released by the end of 2024, the playbook will include coordination plans between domestic and international partners. This effort is part of broader initiatives by the Biden administration to address AI risks, as highlighted by recent guidelines and the establishment of an AI safety and security board by the Department of Homeland Security.
🪆 🇫🇷 A Russian disinformation campaign dubbed "Matryoshka" targeting the upcoming Paris 2024 Olympics has been identified by the French authorities. The campaign aims to sow discord and distrust by spreading false information and manipulating narratives around the event.
The campaign's tactics are designed to exploit existing social and political tensions, amplifying polarizing issues to create confusion and division among audiences. This effort reflects broader Russian strategies observed in past disinformation operations targeting political events and public institutions globally.
🇺🇸 🇨🇳 Microsoft President Brad Smith faced intense scrutiny from lawmakers regarding Microsoft's operations in China amid rising cybersecurity threats linked to Beijing. During a hearing with the House Homeland Security Committee, Smith was questioned about Microsoft's compliance with China's 2017 national security law, which mandates cooperation with Chinese intelligence agencies. Smith insisted that Microsoft’s cloud business in China ensures American trade secrets remain secure in U.S.-based data centers and stated that Microsoft refuses any requests from the Chinese government to access these centers.
🇺🇸 The Government Accountability Office (GAO) has issued a reminder to the White House about the numerous cybersecurity regulations that need addressing as the 2024 election approaches. Cybersecurity has been on GAO's high-risk list since 1997 due to its vulnerability to waste, fraud, abuse, or mismanagement, necessitating transformation. In its latest update, the GAO highlighted that the White House has yet to implement 567 out of 1,610 cybersecurity-related recommendations made since 2010. Key areas needing attention include establishing a comprehensive cybersecurity strategy with effective oversight, securing federal systems and information, protecting critical infrastructure, and safeguarding privacy and sensitive data.
🇺🇸 The city of Cleveland is working to restore (scrambling) its systems following a cyberattack that disrupted several municipal services. The incident has affected the city's ability to process payments, provide public services, and conduct other administrative tasks. Cleveland officials are collaborating with cybersecurity experts and law enforcement to investigate the breach and mitigate its impact. They are prioritizing the restoration of critical services while ensuring that data security measures are reinforced to prevent future attacks.
Malware & Threats
🦠 🇵🇰 A recent cybersecurity report has revealed that a sophisticated malware campaign, linked to Pakistan, has been targeting Indian government and military personnel. The campaign employs a variety of tactics, including social engineering and spear-phishing, to deliver the Crimson RAT (Remote Access Trojan) and other malware strains. The attackers use fake websites and malicious documents to lure victims, aiming to steal sensitive information and conduct surveillance. This campaign underscores the ongoing cyber tensions between the two nations and highlights the need for enhanced cybersecurity measures to protect critical infrastructure and sensitive data.
🦠 A newly discovered cross-platform malware called NoodleRat has been found targeting both Windows and Linux systems. Researchers from Trend Micro disclosed that the malware is capable of stealing sensitive information, executing remote commands, and running cryptocurrency miners on infected machines. NoodleRat spreads through phishing emails and malicious attachments, disguising itself as legitimate software to evade detection.
The malware's sophisticated features include the ability to download additional payloads, execute shell commands, and establish persistence on compromised systems. It utilizes a combination of techniques to maintain its presence and evade traditional security measures, making it a potent threat to users across different operating systems.
🦠 🥚 The MoreEggs malware, disguised as fake resumes, is targeting companies by delivering malicious payloads via phishing emails. The campaign aims to compromise corporate networks by leveraging social engineering tactics. MoreEggs, known for its stealth and persistence, allows attackers to gain unauthorized access to systems, potentially leading to data theft and other malicious activities.
🦠 💸 The TellYouThePass ransomware group began exploiting a PHP vulnerability, CVE-2024-4577, just days after its public disclosure. This flaw affects Windows servers using Apache and PHP-CGI, allowing remote code execution through manipulated Unicode characters. Although PHP patches were released promptly, attackers quickly targeted vulnerable systems, executing PHP code to deploy ransomware. TellYouThePass ransomware, active since 2019, has a history of exploiting high-profile vulnerabilities. The malware encrypts files, halting processes and communicating with a command-and-control server once executed.
🦠 🇨🇳 Researchers have discovered an updated version of the malware ValleyRAT, used in a new cyber campaign. This version includes advanced features like screenshot capture, process filtering, forced shutdown, and clearing event logs. ValleyRAT is linked to a China-based threat actor and employs a complex, multi-stage infection process to avoid detection. The malware starts with a downloader, fetches various files, and ultimately injects shellcode into "svchost.exe" to contact a command-and-control server. The attack method is designed to evade security tools effectively.
AI, Tech & Tools
🐡 In a recent commit, Damien Miller (djm@) introduced the new sshd(8) configurations options, PerSourcePenalties and PerSourcePenaltyExemptList, to provide a built in facility in sshd(8) itself to penalize undesirable behavior, and to shield specific clients from penalty, respectively [read more on Undeadly.org].
🤖 📷 Microsoft has decided to disable its controversial Windows Recall feature by default on Copilot+ PCs after public backlash: Criticized as a security and privacy risk, Windows Recall, which uses AI to create a searchable digital memory of user activity, was originally enabled by default, requiring users to opt out manually. Security concerns were heightened when researchers demonstrated how malware could exploit Recall data and revealed its inadequate protection. In response, Microsoft announced changes to make the feature opt-in and to enhance data protection. This includes requiring Windows Hello enrollment and "proof of presence" to access Recall snapshots, along with additional encryption measures. Despite the adjustments, Microsoft continues to promote the feature, emphasizing that all data processing occurs locally without cloud involvement.
➝ Ethical hacker releases tool to exploit Microsoft's Recall AI, says it's not 'rocket science'
➝ Microsoft’s Recall puts the Biden administration’s cyber credibility on the line
"Recall will now shift from a preview experience broadly available for Copilot+ PCs on June 18, 2024, to a preview available first in the Windows Insider Program (WIP) in the coming weeks, " reads an update to a recent Windows Recall blog post.
Vulnerabilities, Research, and Threat Intelligence
Adobe Plugs Code Execution Holes in After Effects, Illustrator
Apple Patches Vision Pro Vulnerability Used in Possibly ‘First Ever Spatial Computing Hack’
Exploit for Veeam Recovery Orchestrator auth bypass available, patch now
Microsoft Issues Patches for 51 Flaws, Including Critical MSMQ Vulnerability
SAP Patches High-Severity Vulnerabilities in Financial Consolidation, NetWeaver
SolarWinds Patches High-Severity Vulnerability Reported by NATO Pentester
🔓 🫵🏻 A critical vulnerability has been discovered in ZKTeco's biometric access control system, which is widely used in various industries to secure physical access to buildings and sensitive areas. The vulnerability, allows attackers to bypass authentication and gain unauthorized access to the system. This can lead to potential breaches in secured premises and unauthorized access to sensitive information. "By adding random user data to the database or using a fake QR code, a nefarious actor can easily bypass the verification process and gain unauthorized access," Kaspersky said.
⚠️ 📱 Google has issued a warning about a security vulnerability in the firmware of its Pixel smartphones. This flaw, tracked as CVE-2023-5671, could potentially allow attackers to bypass the lock screen protections, gaining unauthorized access to affected devices. Google recommends users update their devices to the latest security patch to mitigate the risk. This vulnerability underscores the importance of regularly updating device firmware to protect against emerging threats.
🐛 Arm has identified a security flaw, CVE-2024-4610, in the Mali GPU Kernel Driver, exploited in the wild. This use-after-free vulnerability affects Bifrost and Valhall GPU Kernel Drivers (versions r34p0 to r40p0), allowing local non-privileged users to access freed memory. The issue was fixed in version r41p0, released in November 2022, with the latest version being r49p0 from April 2024. Previous similar vulnerabilities, such as CVE-2022-38181 and CVE-2023-4211, were used in targeted attacks on Android devices by commercial spyware vendors. Users should update to the latest driver version to mitigate risks.
🐛 💰 Apple declined to award a bug bounty to Kaspersky Lab after the cybersecurity firm disclosed four zero-day vulnerabilities in iPhone software. These vulnerabilities were allegedly used in a sophisticated state-sponsored espionage campaign targeting Kaspersky employees and Russian diplomats. Despite Kaspersky's belief that their findings were eligible for a bounty, Apple cited their policy in refusing the reward. The refusal comes amid heightened tensions between the U.S. and Russia, exacerbated by Russia's invasion of Ukraine and subsequent sanctions and restrictions imposed by Apple on its products and services in Russia. Kaspersky had disclosed the vulnerabilities publicly, highlighting the complexity of the attack, which involved exploiting an unusual hardware feature. Apple denied any collaboration with any government to facilitate spying and did not comment on the bounty refusal. The situation raises questions about future disclosures by Kaspersky and the broader implications of geopolitical tensions on cybersecurity collaboration.
ICS & OT
ICS Patch Tuesday: Advisories Published by Siemens, Schneider Electric, Aveva, CISA
Rockwell Automation Patches High-Severity Vulnerabilities in FactoryTalk View SE
🐛 Cisco’s Talos research and threat intelligence unit identified 15 high and critical severity vulnerabilities in AutomationDirect's Productivity series PLCs. These vulnerabilities allow for remote code execution or denial-of-service attacks, which can significantly disrupt industrial operations. Typically, these PLCs are not directly internet-exposed, requiring attackers to first infiltrate the organization’s network, although about 50 potentially internet-connected devices were found via Shodan. Some flaws could enable attackers to execute arbitrary code, manipulate device logic, or extract information. Notified by CISA in May, AutomationDirect has released updates and mitigation guidelines. Talos has published detailed advisories on these vulnerabilities.