[InfoSec MASHUP] Week 26/2024
Julian Assange released; Supply Chain Attack on WordPress plugins; US automotive dealers nightmare; Kaspersky ban impact; MOVEit flaw exploited; LockBit lied!
Partners and Affiliates
🔐 NordVPN x Saily (Jun 12 - Aug 7) ✈️
Save up to 73% + get free travel data! Users buying a 2-year NordVPN plan will get up to 20GB of free travel data from Saily:
Basic plan - 1GB; Standard & Plus plans - 3GB; Complete plan - 10GB; Ultimate plan - 20GB
Claim your gift right away. New NordVPN users will be able to claim their Saily travel data using a coupon code via the Saily app.
Breaches & Security Incidents
🔓 🇺🇸 The LockBit ransomware group falsely claimed to have breached the US Federal Reserve and stolen 33 terabytes of data. In reality, the cyberattack targeted Evolve Bank & Trust, a US financial institution. Evolve confirmed the data theft and is working with law enforcement. This misleading claim appears to be a tactic by LockBit to maintain relevance after law enforcement actions disrupted their operations earlier this year.
🔓 🇺🇸 ID Verification Service for TikTok, Uber, X, exposed Driver Licenses - “My personal reading of this situation is that an ID Verification service provider was entrusted with people's identities and it failed to implement simple measures to protect people's identities and sensitive ID documents,” Mossab Hussein, chief security officer at cybersecurity firm spiderSilk, and who alerted 404 Media to the exposed credentials, said.
🔓 🇮🇩 Indonesia has confirmed a cyberattack on its national data center, compromising sensitive government and citizen information. The attack involved a ransomware demand of $8 million, which Indonesia has refused to pay.
🔓 🇺🇸 Neiman Marcus has disclosed a data breach in which a hacker accessed its systems and stole customer information. The stolen data, which includes sensitive personal details, is being offered for sale by the hacker. Neiman Marcus is notifying affected customers and working with cybersecurity experts to investigate and address the breach.
🔓 🇺🇸 LivaNova USA has disclosed a data breach affecting 130,000 individuals. The breach involved unauthorized access to personal information, including names, addresses, Social Security numbers, and health information. LivaNova is notifying those affected and offering complimentary credit monitoring and identity protection services.
🔓 🇺🇸 At least six major automotive dealers, including Lithia Motors, Group 1 Automotive, Penske Automotive Group, Sonic Automotive, Asbury Automotive Group, and AutoNation, have reported disruptions due to a ransomware attack on CDK Global, a software provider for the automotive industry. The attack, attributed to the BlackSuit ransomware group, led CDK to shut down most of its systems as a precaution. BlackSuit, a rebrand of the Royal ransomware operation, demanded tens of millions of dollars in ransom. The group has a history of high-profile attacks and is believed to be linked to the notorious Conti ransomware gang. Despite the significant impact, neither CDK Global nor its parent company, Brookfield Business Partners, have commented on the situation or the ransom demands.
🔓 🇺🇸 A warning has been issued to chemical facilities about potential data theft following a breach of the Cybersecurity and Infrastructure Security Agency's (CISA) CSAT (Chemical Security Assessment Tool). The breach may have exposed sensitive information submitted by these facilities for security assessments, potentially compromising their security posture and confidentiality. CISA has alerted affected facilities to review their submitted data for any signs of misuse or unauthorized access.
🇰🇵 💰 North Korean hackers have breached 1,590 cryptocurrency wallets belonging to CoinStats users. CoinStats, a popular cryptocurrency portfolio manager, discovered the breach on June 18, 2024. The attackers exploited a vulnerability in the app's third-party integration with decentralized wallets. The breach allowed them to siphon off crypto assets from affected wallets. CoinStats has since patched the vulnerability and is cooperating with law enforcement and cybersecurity experts to investigate the incident. Users are advised to secure their accounts and enable two-factor authentication to prevent further unauthorized access.
🔓 🇦🇺 A hacker claims to have stolen 30 million customer records from TEG, an Australian ticket-selling giant. The data breach allegedly involves sensitive information such as names, email addresses, phone numbers, and ticket purchase details. The hacker, who posted the stolen data for sale on a dark web forum, is demanding a ransom for the information. TEG, which owns Ticketek and several other ticketing platforms, has not yet confirmed the breach but is reportedly investigating the situation. This incident raises significant concerns about data security and the protection of customer information within the ticketing industry.
➝ More breaches:
Infosys McCamish says LockBit stole data of 6 million people
Chicago Children’s Hospital Says 791,000 Impacted by Ransomware Attack
Designed Receivable Solutions Data Breach Impacts 585,000 People
Push Notification Fatigue Leads to LA County Health Department Data Breach
BlackSuit ransomware gang claims attack on KADOKAWA corporation
Cybercrime, Cyber Espionage, APT’s
🇺🇸 ❌ Google has disrupted over 175,000 instances of YouTube and Blogger accounts linked to the China-based influence operation Dragonbridge. Known for its low-quality content promoting Chinese political narratives, Dragonbridge's activities include using spam networks and inauthentic accounts to post content on various social platforms. Despite scaling operations, the group has seen minimal real engagement, with most videos receiving few or no views. Dragonbridge continues to experiment with new tactics, including generative AI, to spread its messaging.
🇺🇸 🇷🇺 A federal grand jury in Maryland indicted Amin Timovich Stigal, a 22-year-old Russian, for collaborating with Russia's military intelligence (GRU) to conduct cyberattacks against Ukraine prior to the 2022 invasion. Stigal is accused of using malware disguised as ransomware, known as “WhisperGate,” to target Ukrainian military and civilian systems. He faces charges of conspiracy to hack and destroy government data, with a potential five-year prison sentence. The U.S. State Department has offered a $10 million reward for information on Stigal. He allegedly managed computer environments used in WhisperGate campaigns against Ukrainian, NATO, and U.S. networks since 2021. In May 2022, the U.S. and allied countries attributed the WhisperGate attacks, including a disruption of Viasat communications, to the Russian government.
🇨🇳 Chinese hackers have intensified their cyberattacks on Taiwanese organizations, according to cybersecurity firm TeamT5. The firm noted a significant increase in cyber espionage activities targeting Taiwanese entities, including government agencies, high-tech companies, and critical infrastructure sectors. These attacks are primarily focused on stealing sensitive information and intellectual property. The escalation comes amid rising tensions between China and Taiwan, with hackers employing advanced techniques to breach security defenses.
🇻🇳 🇺🇸 Three Vietnamese members of the FIN9 hacking group have been charged in the United States for their involvement in a series of cyberattacks targeting businesses. The individuals, believed to be part of a sophisticated cybercrime syndicate, are accused of deploying malware to steal payment card information from retail, hospitality, and entertainment sectors. The stolen data was then sold on the dark web, leading to significant financial losses for the affected companies. This action highlights the ongoing efforts by U.S. authorities to combat international cybercrime and hold perpetrators accountable.
🇷🇺 🎣 The ExCobalt cyber gang has been actively targeting Russian diplomats and government officials with spear-phishing attacks. This campaign, discovered by Check Point Research, involves sending malicious emails designed to look like official correspondence from Russian government agencies. The emails contain links to malware hosted on compromised websites. The malware, once downloaded, can steal sensitive information and provide remote access to the attackers. ExCobalt is believed to be using these tactics to gather intelligence and potentially disrupt government operations. The attacks have been ongoing since at least January 2023, highlighting the persistent and evolving nature of cyber threats against state actors.
Government, Politics, and Privacy
🇺🇸 🇷🇺 Kaspersky resellers deride US government ban: ‘Complete bulls—t’ - The ban, implemented due to concerns over Kaspersky's ties to the Russian government, prohibits the sale and use of Kaspersky products in the U.S. This decision affects resellers who now face challenges in removing Kaspersky products from their offerings and finding alternative solutions for their customers. The move underscores the broader geopolitical tensions and the increasing scrutiny on software with potential foreign government links. Resellers must now navigate the logistical and financial implications of this significant change in the cybersecurity landscape.
🇺🇸 🇬🇧 Julian Assange, the founder of WikiLeaks, has been released from a British prison. His release comes after several years of legal battles and imprisonment related to his role in publishing classified documents. Assange had been held in Belmarsh Prison in London, where he faced extradition requests from the United States on charges of espionage and conspiracy to commit computer intrusion. The decision to release Assange marks a significant development in his long-standing legal saga, which has drawn international attention and sparked debates over press freedom and government transparency. His release has been met with mixed reactions, with supporters celebrating his freedom and critics expressing concern over the implications for national security.
➝ WikiLeaks Founder Julian Assange Returns to Australia a Free Man After US Legal Battle Ends
Malware & Threats
🦠 🕸️ The P2PInfect botnet, which targets Redis servers, has added a ransomware module to its operations. Initially dormant, the botnet is now actively deploying ransomware and cryptominers. The ransomware encrypts various file types and appends the '.encrypted' extension, while the cryptominer exploits infected systems to mine Monero. The botnet also includes a rootkit to hide its activities. Researchers believe P2PInfect may be a "botnet for hire," posing a significant threat to Redis servers.
🦠 🌐 A recent supply chain attack has impacted over 100,000 websites by injecting malware via the cdn.polyfill.io domain, which was taken over by the Chinese CDN company Funnull. The attack involves dynamically generated malicious code based on HTTP headers, redirecting users to unwanted sites and potentially leading to broader security threats like data theft. Site owners are advised to remove the cdn.polyfill.io domain from their websites to mitigate risks.
➝ Polyfill claims it has been 'defamed', returns after domain shut down
🦠 🔓 A recently disclosed critical vulnerability (CVE-2024-29973) in discontinued Zyxel NAS devices is being exploited by a Mirai-like botnet. This flaw allows remote code execution via crafted HTTP POST requests. The vulnerability was introduced during a previous patch for a similar issue. Despite the affected NAS products being discontinued, Zyxel released patches due to the severity of the vulnerabilities. Users are urged to update their devices or replace them with supported models.
🔓 💥 Hackers are exploiting a critical authentication bypass flaw in Progress MOVEit Transfer, identified as CVE-2024-5806, just after its disclosure. This vulnerability allows attackers to access and manipulate sensitive data on MOVEit servers. Proof-of-concept exploit code is already available, and ongoing attacks have been reported. Affected MOVEit Transfer versions include 2023.0.0, 2023.1.0, and 2024.0.0, with patches available for each. Organizations are urged to apply updates and mitigations promptly to protect their systems.
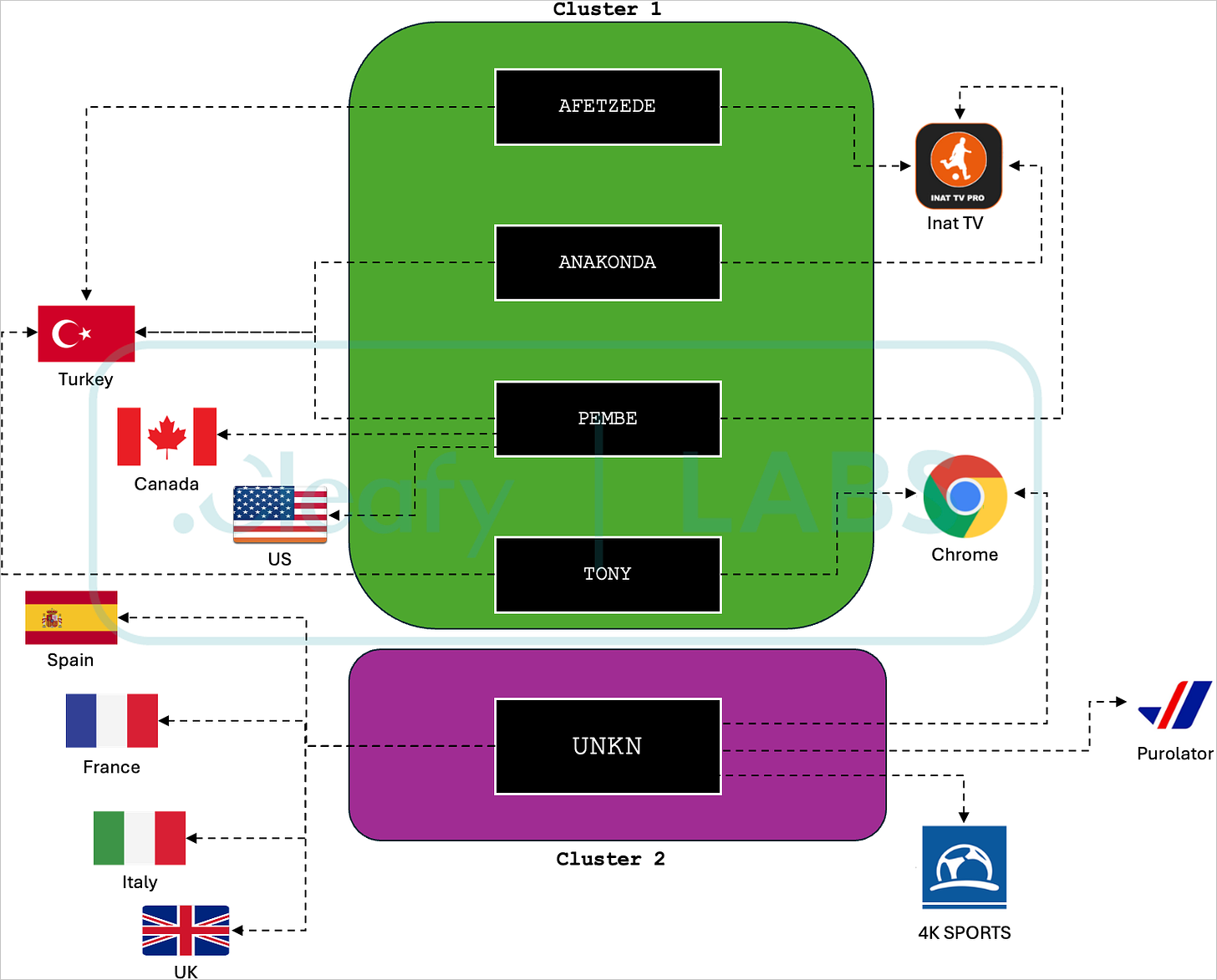
🦠 🏦 New variants of the Medusa malware are targeting Android users across seven countries, including the United States, Canada, and several in Europe. These variants are being distributed through malicious apps found on the Google Play Store. Once installed, the malware can steal sensitive information, such as banking credentials and personal data, and even take control of the infected device. The Medusa malware has evolved with new capabilities, making it more dangerous and harder to detect.
🦠 🤖 Emergence of Rafel malware targeting outdated Android devices in ransomware attacks. Dubbed Rafel RAT (Remote Access Trojan), the malware exploits vulnerabilities in older Android versions to gain control over devices, encrypting files and demanding ransom payments from victims. This malware is particularly concerning because it leverages known security flaws that are no longer patched in older Android versions, making devices vulnerable to compromise. The attacks primarily target users in Southeast Asia, with the malware distributed through malicious apps and APK files.
AI, Tech & Tools
🐛 🤖 A high-severity vulnerability (CVE-2024-5565) in the Vanna.AI library allows remote code execution via prompt injection. The flaw in the "ask" function can be exploited to execute arbitrary commands. Vanna, a Python-based machine learning library, translates user prompts into SQL queries using a large language model. Despite a hardening guide release, users are advised to deploy Vanna in a sandboxed environment to mitigate risks. The issue highlights the dangers of prompt injection in generative AI models.
Vulnerabilities, Research, and Threat Intelligence
Apple Patches AirPods Bluetooth Vulnerability That Could Allow Eavesdropping
Fortra Patches Critical SQL Injection in FileCatalyst Workflow
🐌 💥 Researchers from Graz University have identified a new side-channel attack called SnailLoad, which exploits network latency to spy on users' web activities. This attack does not require direct interaction with the victim's system or execution of malicious code. Instead, it uses latency variations caused by loading assets from an attacker-controlled server to infer what websites or videos a user is accessing. The attack leverages network bottlenecks, typically the last node before a user's router, to measure latency and deduce network activity.
🐛 🔓 GitLab recently addressed a critical security vulnerability that could allow attackers to execute pipeline tasks under another user's account. This flaw, identified as CVE-2023-5009, has a high severity rating with a CVSS score of 9.6. It affects GitLab Community Edition (CE) and Enterprise Edition (EE) versions 13.12 through 16.2.7 and 16.3 through 16.3.4. Exploiting this vulnerability could enable attackers to impersonate users and run automated tasks, potentially leading to unauthorized access to sensitive information, code execution, data modification, or triggering other critical events within the GitLab system. This poses significant risks, including intellectual property theft, data leaks, and potential supply chain attacks.
🔓 🧩 A supply chain attack on several WordPress plugins has impacted up to 36,000 websites. The attack involved unknown threat actors injecting malicious code into plugin updates on WordPress.org. This code created attacker-controlled administrative accounts and inserted SEO spam across the compromised sites. The affected plugins include Social Warfare, BLAZE Retail Widget, Wrapper Link Elementor, Contact Form 7 Multi-Step Addon, and Simply Show Hooks. The malicious injections date back to June 21, 2024, and were active as recently as the morning of the report. Site owners are advised to uninstall these plugins immediately, check for unauthorized admin accounts and malicious content, and monitor connections from suspicious IP addresses.
🐛 🤖 Google has unveiled Project Naptime, a framework designed to enable large language models (LLMs) to conduct vulnerability research, enhancing automated discovery approaches. This initiative aims to mimic the workflow of human security researchers by equipping an AI agent with specialized tools, allowing it to identify and demonstrate security vulnerabilities. Key components of Project Naptime include a Code Browser tool for navigating codebases, a sandboxed Python tool for fuzzing, a Debugger for observing program behavior, and a Reporter for monitoring task progress.
🔓 🚘 The Electronic Frontier Foundation (EFF) has issued a new warning about vulnerabilities in Automated License Plate Readers (ALPRs). Researchers found that certain ALPR systems are susceptible to hacking, which could allow attackers to manipulate or access sensitive data. These vulnerabilities pose significant privacy risks, as ALPRs collect and store large amounts of information about vehicle movements, potentially exposing individuals to surveillance and data breaches. The EFF urges manufacturers to address these security flaws and for entities using ALPRs to implement stronger data protection measures.
ICS, OT & IoT
🐛 🏭 Claroty discovered critical vulnerabilities in Emerson gas chromatographs, including command injection and authentication bypass flaws, which could allow attackers to execute arbitrary commands with root privileges. These devices, used in sectors like healthcare and environmental monitoring, are vulnerable to severe impacts such as disrupting blood testing in hospitals or halting food processing operations. Emerson has issued firmware updates to mitigate these risks and advises isolating affected devices from the internet and ensuring they are on well-protected networks.
🐛 🏭 Siemens recently disclosed multiple vulnerabilities in its SICAM products, which are crucial for the energy sector. These vulnerabilities could potentially allow attackers to execute denial-of-service (DoS) attacks, disrupt operations, and compromise system integrity. The security issues are tracked under several CVE identifiers, indicating the range and severity of the threats. Siemens has released patches and mitigations to address these flaws and recommends users update their systems promptly to mitigate potential risks.