We now have {{active_subscriber_count}} active subscribers! Thank you all for being part of my newsletter. Please share it with your friends and colleagues, and let’s keep growing the community.
💜 A quick personal note — I recently looked at my newsletter stats and noticed that a good chunk of you open and read this every single week. I just wanted to say: thank you. Genuinely. This is a solo effort, and knowing that some of you look forward to it every weekend makes it worthwhile.
If you ever want to share feedback, suggest a topic, or just say hi — hit reply. I read everything.
📲 Your iPhone has a green dot. It means the camera is on — Apple put it there so you'd know. Hardware-level, they said. Can't be bypassed, they implied. Predator didn't get the memo.
Jamf Threat Labs published a detailed breakdown last week—and it’s worth your time this week-end—of how Intellexa's spyware defeats both the camera and microphone indicators with a single hook — one instruction that sets the self pointer to NULL, exploiting a quirk of Objective-C where messages to nil are simply... ignored. No dot. No warning. No trace. The device works normally. You just have no idea you're being watched.
The technical elegance is, honestly, impressive — if you can set aside the part where it's used to surveil journalists, activists, and politicians.
The good news, if you can call it that: your iPhone needs to be fully compromised first — kernel access, code injection into SpringBoard, the works. Predator doesn't walk in through the front door. It needs a zero-day chained exploit to get there. The bad news: Intellexa has a track record of finding them.
Sanctioned by the US, flagged by Google, dissected by researchers — and somehow still very much in business. Predator is the cockroach of the spyware industry, and this week we got a very good look at its internals.

Figure: Monster in Predator movie/20th Century Studios
Let’s now dive into this week’s top insights! 🚀
Table of Contents
🔓 BREACHES & SECURITY INCIDENTS
🇺🇸 A January 2025 ransomware attack on Conduent has exposed personal data for at least 25 million people in the U.S. The stolen data includes names, birthdates, addresses, Social Security numbers, and medical and insurance information. Conduent has given few details and even hid its incident notice from search engines.
🇳🇱 The ShinyHunters extortion gang claims it breached Dutch telecom Odido and stole millions of user records. Odido confirmed a February breach of its customer contact system affecting about 6.2 million customers but said passwords, call details, and billing data were not exposed. ShinyHunters posted leaked data and alleged it includes internal files and plaintext passwords, while Odido denies those additional claims.
🇨🇳 Chinese hackers used a secret backdoor in Pulse Secure VPN software owned by Ivanti to breach dozens of organizations. The compromise affected at least 119 customers and included U.S. and European military contractors. Cuts after private equity takeovers are blamed for weakening Ivanti’s security, and agencies were later ordered to disconnect Ivanti VPNs due to active exploits.
🇺🇸 🏥 Nearly 140,000 people may be affected by a data breach tied to Vikor Scientific (now Vanta Diagnostics). The breach appears to have originated at billing vendor Catalyst RCM, whose compromised credentials exposed names, DOBs, payment and medical details. It’s unclear if 139,964 is the final total, and some parties have not confirmed the full number.
🇺🇸 🏥 A ransomware attack forced the University of Mississippi Medical Center to close about three dozen clinics and cancel elective procedures. Staff are working offline while investigators, including the FBI, try to restore systems and determine if patient data was stolen. Hospitals and emergency rooms stayed open and patients with urgent needs are being contacted.
👁 A huge unsecured database tied to IDMerit exposed about one billion sensitive identity records from at least 26 countries. The leaked data included names, birthdates, addresses, national IDs and verification logs, risking identity theft and targeted fraud. The server was later secured, but the incident highlights weak vendor security and major risks from third-party identity systems.
→ More Breaches and Incidents:
🥷🏻 CYBERCRIME, CYBER ESPIONAGE, APT’s
🇪🇺 Europol launched Project Compass to combat The Com, a global network of mostly young cybercriminals who commit violence, extortion, and child exploitation. The operation, backed by 28 countries, has helped identify 179 perpetrators, arrest 30, and find dozens of victims. Authorities say international information-sharing and sustained efforts are key to protecting victims and disrupting the group.
🇷🇺 🇪🇺 A Russia-aligned group called UAC-0050 (Mercenary Akula) used a spoofed Ukrainian domain and a phishing email to deliver RMS remote-access malware to a European financial institution. The attackers used layered archives and a fake PDF executable to bypass defenses and gain stealthy access for intelligence gathering or financial theft. This incident suggests the group may be expanding targeting beyond Ukraine to Western entities that support it.
🇨🇳 👀 Google says it disrupted a long-running China-linked cyberespionage campaign that targeted telecoms and governments in dozens of countries. The attackers used a new backdoor called GridTide and hid commands in cloud services like Google Sheets to steal or monitor sensitive data. Google, Mandiant and partners took down the malware infrastructure, disabled attacker accounts, and notified victims.
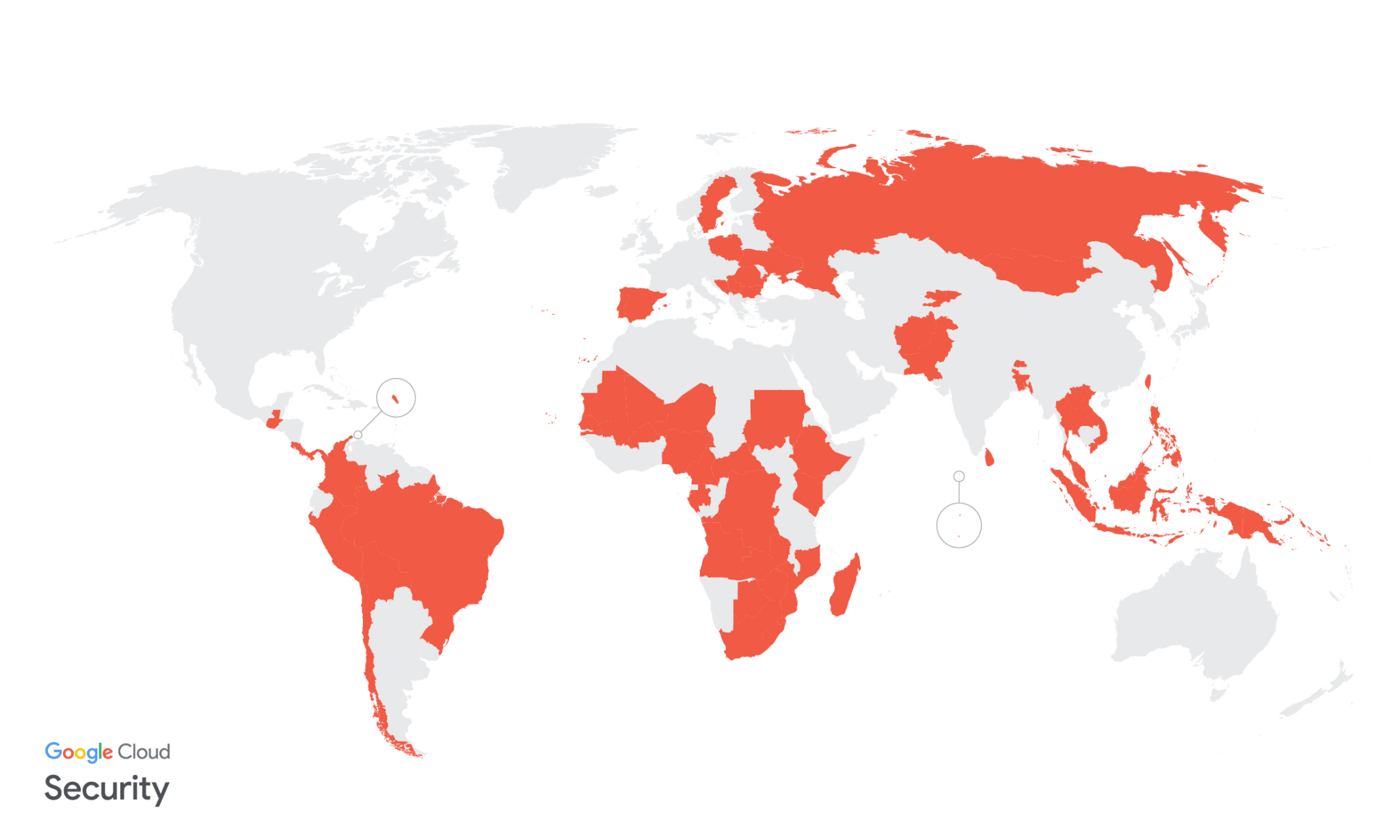
Figure: Countries with suspected or confirmed UNC2814 victims/Google.com
🇺🇸 The U.S. Department of Justice seized $61 million in Tether tied to “pig butchering” crypto scams. Scammers lured victims via dating and social apps, coerced workers in scam compounds, and laundered stolen funds through many wallets. Tether says it has frozen about $4.2 billion in assets linked to illicit activity, including nearly $250 million since June 2025.
🇺🇸 🇷🇺 The U.S. Treasury sanctioned Russian zero-day broker Operation Zero, its founder Sergey Zelenyuk, and related companies and associates for buying and selling stolen software exploits. Officials say Operation Zero bought tools stolen from a U.S. defense contractor and sold them to unauthorized users, posing national security risks. The sanctions also target UAE-linked firms tied to high-paying zero-day markets.
🇺🇸 🇷🇺 A former L3Harris executive was sentenced to 87 months in prison for selling eight zero-day exploits to a Russian broker. He admitted stealing the exploits from Trenchant and received about $1.3 million in cryptocurrency. Prosecutors said the theft caused $35 million in losses and restitution proceedings continue.
🇰🇵 North Korean state-backed Lazarus actors are now using Medusa ransomware to mount extortion campaigns. They have targeted U.S. healthcare and other organizations, sometimes unsuccessfully, and demanded about $260,000 on average. Researchers found tools and indicators linking these attacks to Lazarus but cannot yet pinpoint a single sub-group.
🇪🇸 Spanish police arrested four suspected members of "Anonymous Fénix", a hacktivist group blamed for DDoS attacks on government sites. The group targeted Spanish and some South American institutions, spiking after deadly Valencia floods. Authorities seized the group’s social accounts and closed its Telegram channel.
🗓️ {Cyber,Info}Sec Events — A community-maintained list of infosec conferences worldwide. Subscribe to the ICS calendar feed to get events straight into your calendar, or follow @[email protected] on Mastodon for weekly digests. Contributions and ⭐ welcome!
👨🏻⚖️ 👀 GOVERNMENT, POLITICS, AND PRIVACY
🍏 ✅ NATO has approved Apple iPhone and iPad for handling classified information at the "NATO RESTRICTED" level. The devices are now listed in NATO’s vetted product catalog and can access Mail, Calendar, and Contacts securely without special software. Germany’s security agency (BSI) tested and validated the devices, which Apple says met NATO requirements.
🇬🇷 🧑⚖ A Greek court sentenced Intellexa founder Tal Dilian and three associates to eight years in prison for illegal wiretapping and privacy violations. The group was tied to a 2022 scandal where spyware called Predator was used to spy on politicians, journalists, businesspeople, and officials. The U.S. had already sanctioned Intellexa and some executives, and the sentence is stayed pending appeal while authorities investigate further.
🇺🇸 🙊 CISA is in trouble — CISA has lost a large share of its staff and key programs, weakening its cyber defenses and coordination. Political hostility and leadership delays have deepened the problem and eroded trust with industry and local governments. Experts warn CISA may not have the capacity to handle major cyber crises without rebuilding its workforce.
🇬🇧 💰 The UK ICO fined Reddit £14.47 million for collecting and using data from children under 13 without proper safeguards. Reddit only added weak age checks in July 2025, which the regulator said were easy to bypass. Reddit will appeal, arguing most UK users are adults and that stronger ID checks hurt privacy.
🎦 🚗 🇺🇸 People across the U.S. are destroying Flock license-plate surveillance cameras in protest. Critics say the cameras help immigration authorities track and deport people. Cities and activists are cutting, smashing, or demanding removal of the cameras.
🖼 🤖 Data protection authorities from across the globe have published a Joint Statement on AI-Generated Imagery — Global privacy authorities warn against AI systems that create realistic images or videos of real people without consent. They urge organizations to follow data protection laws, add strong safeguards, be transparent, and remove harmful content quickly. Regulators call for proactive engagement to protect privacy, dignity, and vulnerable people.
🪪 🇬🇧 Discord is making age verification mandatory and will use either facial age checks or ID to control access. UK users say Discord changed its promise: some selfies and IDs may be sent to vendor Persona and stored up to seven days instead of always staying on-device. Users worry about data security and Persona’s backers, and Discord has been contacted for comment.
🦠 MALWARE & THREATS
🕹 🎠 Cybercriminals are distributing trojanized gaming tools through browsers and chat apps to install a Java-based remote access trojan (RAT). The malware uses stealthy loaders, Microsoft Defender exclusions, and persistence to enable data theft, remote control, and additional payloads. New RAT families like Steaelite, DesckVB, and KazakRAT bundle theft and ransomware features for powerful, easy-to-use attacker dashboards.
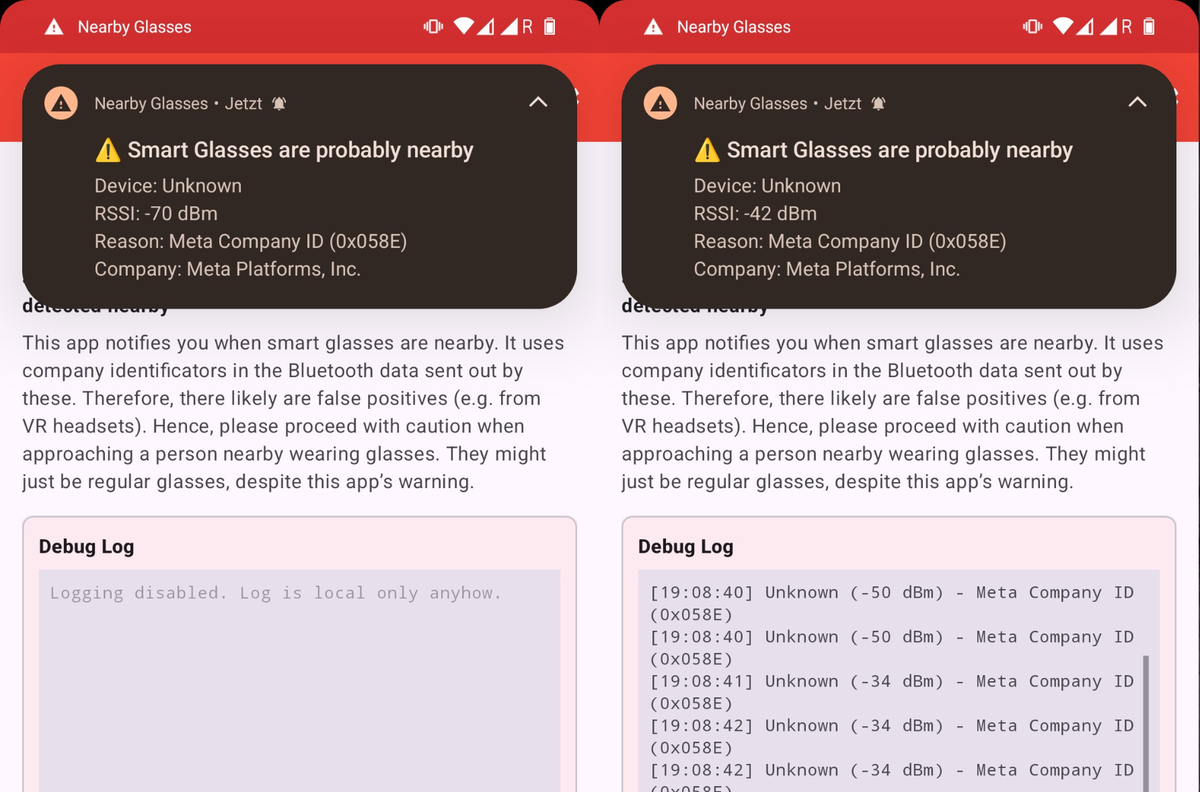
👀 📲 Predator spyware hides iOS camera and microphone recording indicators by hooking a SpringBoard function that blocks sensor status updates. It uses kernel-level access and technique like PAC redirection to bypass permission checks and keep feeds streaming to operators. Jamf’s analysis shows traces of the malware in SpringBoard and mediaserverd despite no visible status-dot indicators.
🪦 Arkanix Stealer was a short-lived malware-as-a-service that surfaced in October 2025 and vanished by December. It stole wide-ranging data — browsers, apps, VPNs, Telegram/Discord, files, wallets — and offered a control panel and post-exploitation tools. Kaspersky says the campaign was a one-shot effort for quick profit, with servers and Discord taken down.
🪱 Researchers found a worm-like campaign (SANDWORM_MODE) using at least 19 malicious npm packages to steal crypto keys, API tokens, and CI/GitHub secrets. The malware also uses a malicious GitHub Action, can wipe home directories, and injects a fake MCP server to trick AI coding tools and harvest LLM keys and SSH/AWS/NPM credentials. Users should remove the listed packages, rotate tokens and secrets, and check repos and workflows for unexpected changes.
🤖 🧰 AI, CRYPTO, TECH & TOOLS
🐛 Researchers found serious vulnerabilities in Anthropic's Claude Code that let attackers run commands and steal API keys by simply opening malicious repositories. The flaws abused config files and MCP servers to bypass consent and send authenticated requests to attacker-controlled endpoints. If exploited, attackers could access project files, modify cloud data, and incur unexpected API costs.
❌ Anthropic has removed the core pledge in its safety policy that barred training new AI models unless safety could be guaranteed in advance. The company says the change reflects practical realities, more transparency, and plans for regular risk reports and safety roadmaps. Critics warn the move weakens constraints and could make managing catastrophic AI risks harder.
🇨🇳 Anthropic says three Chinese AI labs used fake accounts to send 16 million prompts to its Claude model to steal capabilities. The startup calls this “distillation” and warns it can remove safety guards and enable cyberattacks, surveillance, or disinformation. Anthropic urges stronger export controls and says the activity violated its terms.
🐛 🧠 VULNERABILITIES, RESEARCH, AND THREAT INTELLIGENCE
➝ From the Patching Department:
🩹 SolarWinds patched four critical Serv‑U flaws that can allow attackers to gain root or admin access. All four bugs require attackers to already have high privileges, limiting but not eliminating risk. Thousands of Serv‑U servers are exposed online and the software has been repeatedly targeted by threat actors.
⚠ Attackers have been exploiting two Cisco SD-WAN zero-days since 2023 to gain long-term access to network edge devices. Authorities, including CISA and the Five Eyes, issued emergency guidance and threat-hunt steps after discovering the ongoing campaign. Officials warn the attacks are highly targeted and require urgent patching and forensic checks.
⏱ CrowdStrike found attackers are moving through networks much faster, with average breakout time down to 29 minutes and some attacks taking seconds. Attackers increasingly use living-off-the-land tactics, stolen credentials, and cloud or edge device flaws to avoid detection. Nation-state and criminal groups are exploiting more zero-days and AI-driven techniques, widening threats and stressing defenders.
🧠 📲 Security researchers found 1,575 vulnerabilities in ten popular Android mental health apps with over 14.7 million installs. Many flaws could expose therapy data, intercept logins, or let attackers read local files and spoof app behavior. Some apps claim encryption or privacy but still use insecure coding and outdated protections.
✈ 🪖 The Dutch Defense Secretary said the F-35’s software and cloud systems could be “jailbroken” like an iPhone to accept third-party updates. Experts warn doing so would be legally risky and would not replace U.S. maintenance, mission planning, or spare-part support. The comment highlights tensions for foreign F-35 operators reliant on U.S. control and logistics.
🇷🇺 A Russian-speaking hacker used AI tools to help breach over 600 FortiGate firewalls across 55 countries in five weeks. The attacker relied on exposed management interfaces and weak credentials, then used AI-assisted scripts to automate reconnaissance and lateral movement. Amazon warns AI services are lowering the bar for attackers and urges admins to remove internet-exposed interfaces and enable MFA.
🛰️ ICS, OT & IoT
🌱 Gardyn indoor smart gardens had two critical and two high-severity security flaws that could allow remote attackers to take control. Gardyn and CISA say patches and app/firmware updates have been released and most devices should be updated automatically. Researchers estimate about 138,000 devices were affected but there is no evidence the flaws were exploited in the wild.
🔓 🛜 Researchers found a new Wi‑Fi attack called AirSnitch that can break encryption and expose data. The flaw affects home, office, and enterprise networks and exploits weaknesses in Wi‑Fi design. This shows many devices and users remain vulnerable despite past security improvements.
💬 CONNECT
Follow me on Mastodon for quick daily updates and bite-sized content.
Prefer using an RSS feed? Add Infosec MASHUP to your feed here.
Enjoying our newsletter? Forward it to a colleague—
it’s one of the best ways to support us.
Thanks for reading today’s newsletter, and if you're enjoying it and want to support my work, you can buy me a coffee ☕ over at https://www.buymeacoffee.com/0x58
See you next time!
-X.