The Hacktivist Mirror Problem
When bombs fall, keyboards follow. The Handala attack on Stryker — 200,000 systems claimed wiped, 50TB stolen, timed explicitly to the US-Israeli assault on Iran — is textbook retaliation hacktivist logic. But here's the thing nobody wants to say out loud: it barely matters whether the group is genuinely aggrieved civilians or a state front wearing a keffiyeh. The effect is identical. The deniability is the point.
Governments have learned that a "spontaneous" hacktivist campaign does more reputational work than an official cyberunit ever could — and when the targeting is this clean, "spontaneous" deserves serious scare quotes. We saw it with pro-Russian groups after Ukraine. We saw it with pro-Palestinian groups after Gaza. We're seeing it again now with Iran. The pattern is consistent enough to be a doctrine at this point.
What makes it strategically interesting — and analytically treacherous — is the deliberate ambiguity it manufactures. A group claiming to represent bombed civilians carries far more narrative weight than one that's transparently state-linked. Attribution becomes a second-order problem: even if the group is genuinely independent, states benefit from the chaos and quietly let it run. Sometimes they seed it. Sometimes they just watch. The outcome for the victim is the same either way.
The targeting logic follows a reliable playbook too. Not purely military or intelligence targets — those carry too much legal and escalatory risk. Instead: corporations with visible ties to the aggressor country, ideally ones with symbolic weight or defense adjacency. Stryker, with its $450M U.S. military contract and the same name as an Army armored carrier, checked every box. The selection wasn't random. It was a message dressed as an attack.
For defenders, none of this is new — but the tempo is accelerating. Geopolitical flashpoints are now predictable threat amplifiers with a measurable lag between event and campaign. Your company's government contracts, your country of incorporation, your defense-adjacent partnerships — these are part of your attack surface whether you've modelled them that way or not. The groups carrying the flag may be real, fake, or somewhere in the uncomfortable middle. It doesn't matter. The wiper doesn't care about the ideology behind it.
Let’s now dive into this week’s top insights! 🚀
Table of Contents
🔓 BREACHES & SECURITY INCIDENTS
🇬🇧 🏦 🙊 A technical glitch at Lloyds Banking Group let some Lloyds, Halifax and Bank of Scotland app users see other customers' transactions and personal details. The bank says the error was fixed quickly and apologised, while regulators are investigating. Customers reported seeing accounts, payments and even National Insurance numbers that were not theirs.
🇮🇱 🚉 🇮🇷 A cyberattack hacked advertising screens at Herzliya and Tel Aviv Hashalom stations and showed fake Iranian missile alerts. Authorities say the signs were from a private network, not connected to railway infrastructure, and were taken offline. National cybersecurity teams are investigating while Israel Railways works to restore and expand service.
🇮🇷 🇺🇸 Stryker, a major medical device maker, suffered a severe global cyberattack that shut down many systems and wiped devices. An Iranian hacktivist group called Handala claimed credit and said they erased servers and stole data. The company is working to restore operations while investigating the incident.
🛞 Tire maker Michelin confirmed it was hit in the large Oracle E-Business Suite (EBS) cyberattack tied to the Cl0p group. Investigators found an EBS zero-day was exploited and some files were accessed, but Michelin says only a small, non-sensitive data set was affected and no ransomware was used. The attackers have posted hundreds of gigabytes of alleged Michelin data online.
🤖 Researchers at CodeWall used an autonomous AI agent to hack McKinsey’s internal chatbot, Lilli, and gained full read-write access in about two hours. The agent exploited exposed API endpoints and an SQL injection to access millions of messages, files, user accounts, and writable system prompts. McKinsey patched the issues quickly, but the incident shows agentic AI can enable fast, automated cyberattacks.
🇺🇸 Ericsson Inc. says a service provider was hacked and some employee and customer data was stolen. The provider found the breach in April 2025 and finished an investigation in February 2026. Affected people are being offered free identity protection and compensation coverage.
🇨🇳 Salt Typhoon, a China-linked hacking group, has breached dozens of major phone and internet companies worldwide. They stole call logs, texts, and audio from senior officials and compromised telecom infrastructure. Officials say the campaign spans the Americas, Europe, Asia, Africa, and Oceania and risks serious national security harm.
☁ Hackers from the ShinyHunters group claim they have been stealing data from misconfigured Salesforce Experience Cloud sites by abusing the /s/sfsites/aura API. Salesforce says the issue is due to customer guest-user settings, not a platform vulnerability, and advises auditing guest permissions and disabling API access for guests. ShinyHunters says they found ways to bypass record limits and urges disabling public access, which would remove guest access entirely.
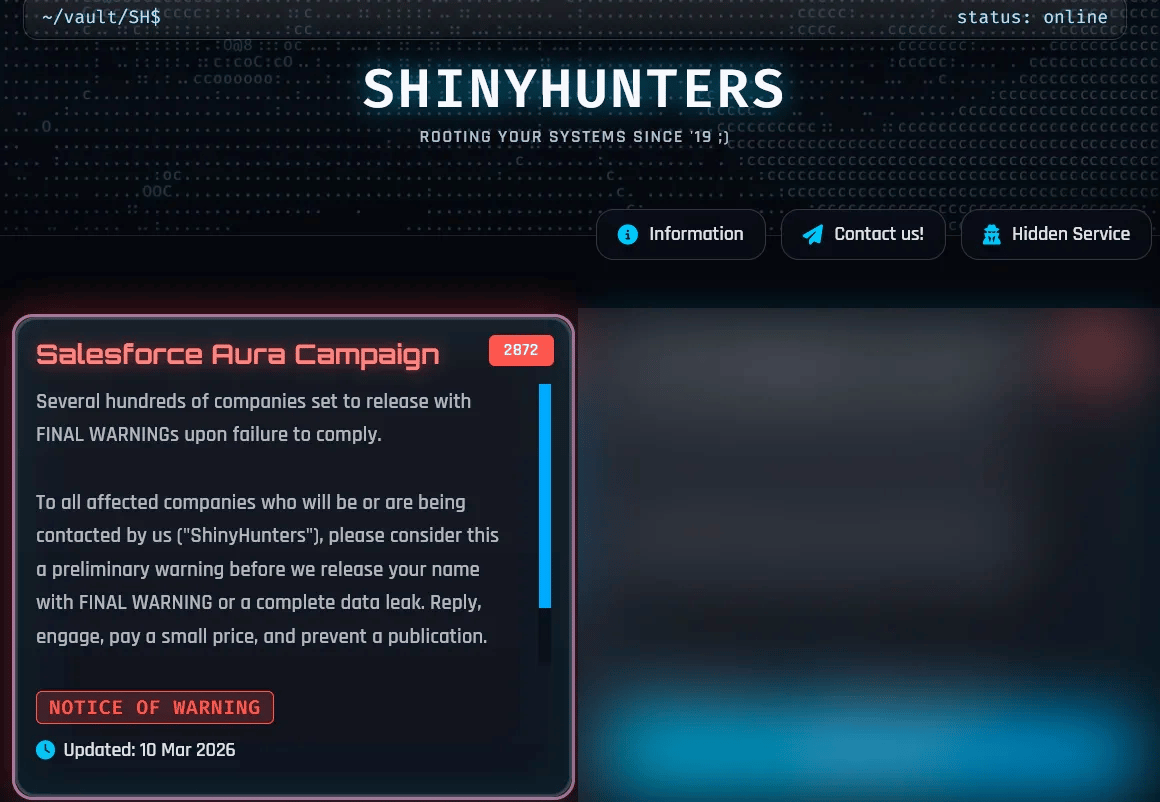
Figure: ShinyHunters Salesforce Aura campaign/BleepingComputer
→ More:
🥷🏻 CYBERCRIME, CYBER ESPIONAGE, APT’s
❌ Interpol-led Operation Synergia III sinkholed tens of thousands of IP addresses and seized servers tied to global cybercrime. Authorities in 72 countries made 94 arrests, seized 212 devices, and are still investigating 110 more suspects. Investigations also found over 33,000 phishing sites and large fraud rings in Togo and Bangladesh.
❌ Law enforcement from many countries dismantled SocksEscort, a global proxy network used for large-scale fraud — The botnet hijacked hundreds of thousands of routers and IoT devices and took in millions of dollars. Authorities seized domains, servers, and cryptocurrency to disrupt the operation.
🇺🇸 ⚖ The U.S. charged former DigitalMint employee Angelo Martino for secretly helping BlackCat ransomware operators and sharing negotiation details. He and accomplices allegedly ran attacks on many U.S. organizations and took ransoms, sometimes paying BlackCat a cut. DigitalMint fired the employees and says it cooperated with law enforcement.
🇺🇸 A foreign hacker broke into the FBI’s New York field office in 2023 and accessed files about Jeffrey Epstein — The breach exploited a vulnerable server at the Child Exploitation Forensic Lab. The FBI says it contained the incident and stopped the hacker’s access.
🗓️ {Cyber,Info}Sec Events — A community-maintained list of infosec conferences worldwide. Subscribe to the ICS calendar feed to get events straight into your calendar, or follow @[email protected] on Mastodon for weekly digests. Contributions and ⭐ welcome!
👨🏻⚖️ 👀 GOVERNMENT, POLITICS, AND PRIVACY
🇫🇮 🇷🇺 🇨🇳 Finland’s 2026 security report warns that Russia and China are actively using cyber espionage against Finnish government, companies, and critical infrastructure. Both countries exploit supply chains, cloud services, and poorly protected consumer devices to steal information and hide their tracks. These operations raise risks for national security, influence campaigns, and Western dependence on Chinese technology.
🇺🇸 🇷🇺 🇨🇳 📲 Researchers say a powerful iPhone-hacking toolkit called Coruna was likely built by L3Harris’s Trenchant unit and sold to U.S. government customers. The tools leaked, were traded by brokers, and ended up used by Russian spies in Ukraine and by Chinese cybercriminals. The case links stolen contractor tools and a former employee who sold exploits to outside parties.
🇪🇺 🎣 An EU court adviser says banks must immediately refund customers for unauthorised transactions unless they have good reason to suspect customer fraud. The opinion came from a case about a phishing attack where a customer’s login was stolen and the bank refused a refund. Banks can later try to recover money if they prove the customer acted with intent or gross negligence.
🦠 MALWARE & THREATS
🔎 🎮 The FBI is investigating a hacker who hid malware inside several games on Steam. The suspected titles include BlockBlasters, Chemia, Dashverse/DashFPS, Lampy, Lunara, PirateFi, and Tokenova. Steam has removed similar malware-laced games before, but some users may have been infected.
🔙 🚪 Researchers found a new backdoor called Slopoly, likely generated with AI, used in an Interlock ransomware attack to steal data. Slopoly is a simple PowerShell client that beacons to a C2 server, runs commands, and keeps persistence. IBM X-Force links the attack to a financially motivated group known as Hive0163 and says AI tools are speeding custom malware development.
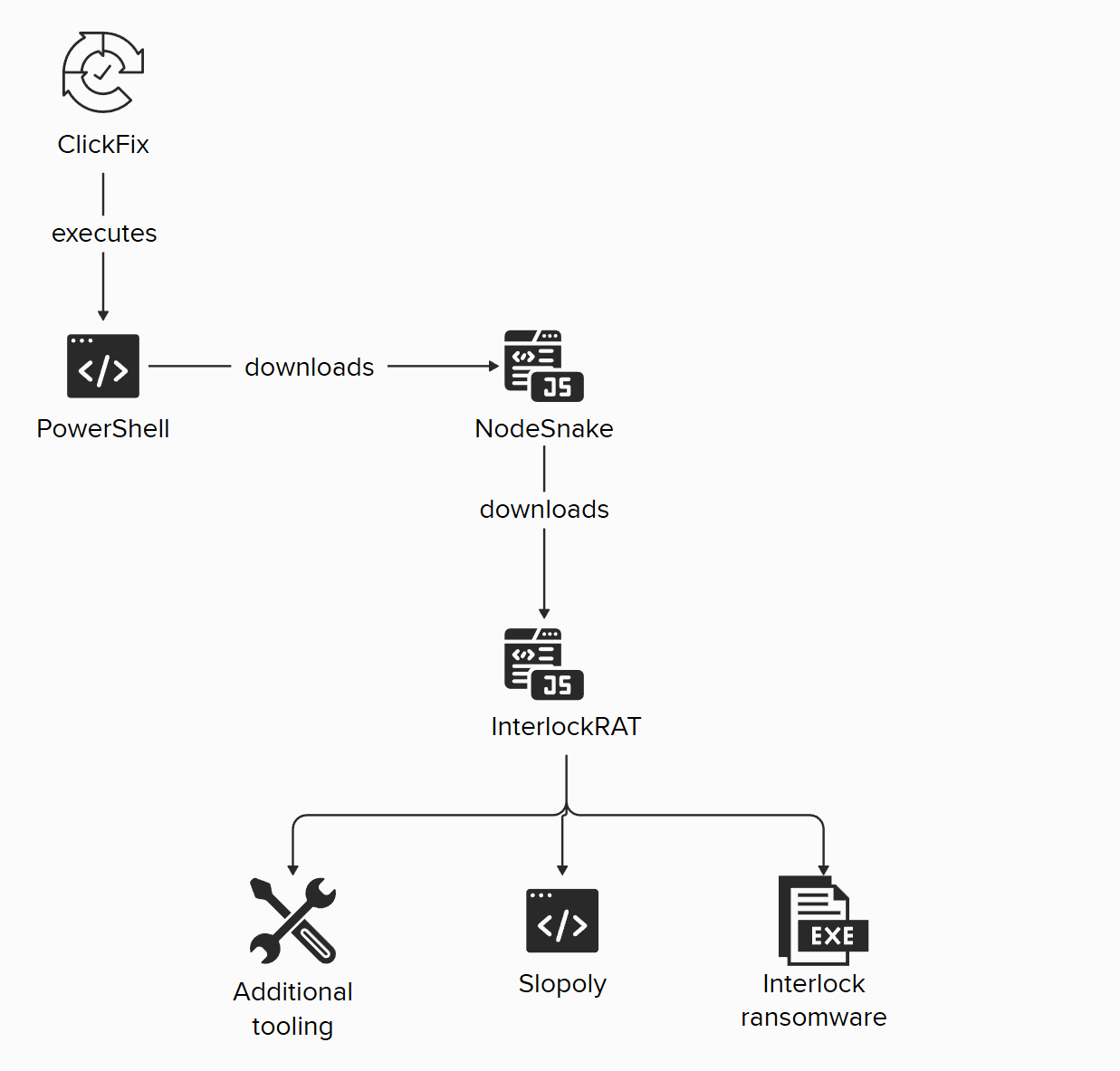
Figure: simplified infection chain/ibm.com
🥷 The PhantomRaven campaign pushed dozens of malicious npm packages that steal developer data by using remote dependencies to bypass scans. Endor Labs found 88 new packages across disposable accounts, with most still live and sending harvested credentials and system info to attacker servers. Developers should only use trusted packages and avoid copy-pasting unvetted code or AI suggestions.
🎣 🎅 A phishing campaign tricks victims into mounting a malicious ISO that looks like a resume and runs hidden PowerShell to load malware. The malware side‑loads a tampered DLL, contacts C2, and injects BlackSanta. BlackSanta kills antivirus and EDR at the kernel level to enable credential theft and data exfiltration.
🛜 Researchers found KadNap malware has infected over 14,000 edge devices, mainly Asus routers, to build a stealthy proxy botnet. It uses a peer-to-peer Kademlia DHT to hide its control infrastructure and resist takedowns. Users are urged to update, reboot, change default passwords, and replace unsupported routers.
🦞 🎠 Researchers found a malicious npm package named @openclaw-ai/openclawai that pretended to be an OpenClaw installer but installs a RAT called GhostLoader. It tricks users with a fake CLI and Keychain prompt, then steals macOS credentials, browser data, crypto wallets, SSH keys, iMessage/Notes, and more. The malware persists, monitors the system, clones authenticated browser sessions, and exfiltrates data to a C2 server and other channels.
🔙 🚪 Hackers used Microsoft Teams to social-engineer employees at financial and healthcare organizations into starting Quick Assist remote sessions. They installed signed MSI files and sideloaded a malicious DLL that decrypts and runs the A0Backdoor malware. A0Backdoor hides C2 traffic in DNS MX queries to steal host data and receive commands.
🇷🇺 💬 Russian state hackers are running a global campaign to hijack Signal and WhatsApp accounts of officials, military staff, journalists and others. They trick users into giving verification codes or abuse linked-device features to take over accounts and read messages. Dutch intelligence warns not to use these apps for sensitive information and gives steps to spot and remove compromised accounts.
🧩 Two Chrome extensions became malicious after ownership changed, allowing attackers to inject code, push malware, and steal browser and device data. The plugins delivered runtime JavaScript from a remote server to execute hidden payloads and trick users into running a Windows executable. Users should remove these extensions and avoid unverified browser add-ons.
→ More:
🤖 🧰 AI, CRYPTO, TECH & TOOLS
🎣 ⏱ Researchers showed they could trick Perplexity's Comet AI browser into a phishing scam in under four minutes by feeding back the browser's own reasoning to a GAN. The attack trains a fake page until the AI stops flagging it, shifting the target from users to the AI agent. Experts warn prompt injection and agentic "blabbering" make such attacks hard to fully eliminate.

🤝 🤑 OpenAI is acquiring AI security startup Promptfoo to boost its safety tools. Promptfoo makes a platform that tests LLMs for attacks like prompt injections and data leaks. OpenAI will add these features to its Frontier platform and keep improving Promptfoo’s open-source tools.
🤯 🔓 💬 Instagram ending support for end-to-end encrypted messaging after 8 May 2026 - https://help.instagram.com/491565145294150
Figure: Instagram warning pop-up about the end of support of end-to-end encrypted messaging/https://hachyderm.io/@pheonix/116221805295722939
📺 🥸 YouTube is expanding its AI deepfake detection to a pilot group of politicians, government officials, and journalists. Eligible users can verify their identity, see detected AI-generated likenesses, and request removal under YouTube policies. The company aims to balance preventing harmful impersonation with protecting free expression and plans broader rollout.
🦞 How AI Assistants are Moving the Security Goalposts — AI assistants that act autonomously on users' computers are becoming popular and powerful. They blur lines between data and code and create big new security risks like credential exposure, prompt-injection, and automated attacks.
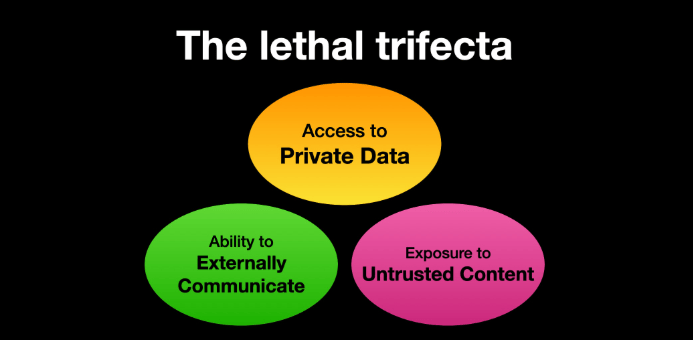
Figure: The lethal trifecta/krebsonsecurity.com
🐛 🧠 VULNERABILITIES, RESEARCH, AND THREAT INTELLIGENCE
➝ From the Patching Department:
💰 🐛 Google paid over $17 million in 2025 to 747 security researchers through its Vulnerability Reward Program. This was a record amount and a more than 40% increase from 2024. Google also expanded AI and open-source reward programs and paid millions across Android, Chrome, and Cloud programs.
🐛 A critical vulnerability (CVE-2026-29000) in the pac4j Java security library lets attackers bypass authentication using public RSA keys. The flaw affects many frameworks and is easy to exploit with a public proof-of-concept. Patches were released quickly, but downstream projects and users remain at risk until they update.
🧩 An SQL injection flaw in the Elementor Ally plugin (CVE-2026-2313) lets unauthenticated attackers steal data by injecting SQL via a URL parameter. Elementor patched it in version 4.1.0, but only ~36% of sites updated, leaving 250,000+ sites vulnerable. Site owners should update Ally and WordPress immediately.
🐛 Researchers found critical bugs in the n8n workflow platform that could let attackers run commands and expose stored credentials. One bug lets public form inputs execute code, and another lets authenticated users escape the expression sandbox. n8n patched the issues and urges updates or temporary restrictions on node use and workflow permissions.
🛰️ ICS, OT & IoT
🩹 ICS Patch Tuesday — Major ICS vendors — Siemens, Schneider Electric, Mitsubishi Electric, and Moxa — released Patch Tuesday advisories fixing multiple vulnerabilities in industrial products. Issues range from critical remote code execution, stored XSS, and hardcoded credentials to DoS and third-party component flaws. CISA and Germany’s VDE-CERT also published advisories for affected ICS and building controllers, some allowing remote full compromise.
💬 CONNECT
Follow me on Mastodon for quick daily updates and bite-sized content.
Prefer using an RSS feed? Add Infosec MASHUP to your feed here.
Enjoying our newsletter? Forward it to a colleague—
it’s one of the best ways to support us.
Thanks for reading today’s newsletter, and if you're enjoying it and want to support my work, you can buy me a coffee ☕ over at https://www.buymeacoffee.com/0x58
See you next time!
-X.