👋 Writing this from San Diego 🇺🇸 — about as far from my Swiss desk as a timezone can stretch. But the news didn't care about my travel schedule.
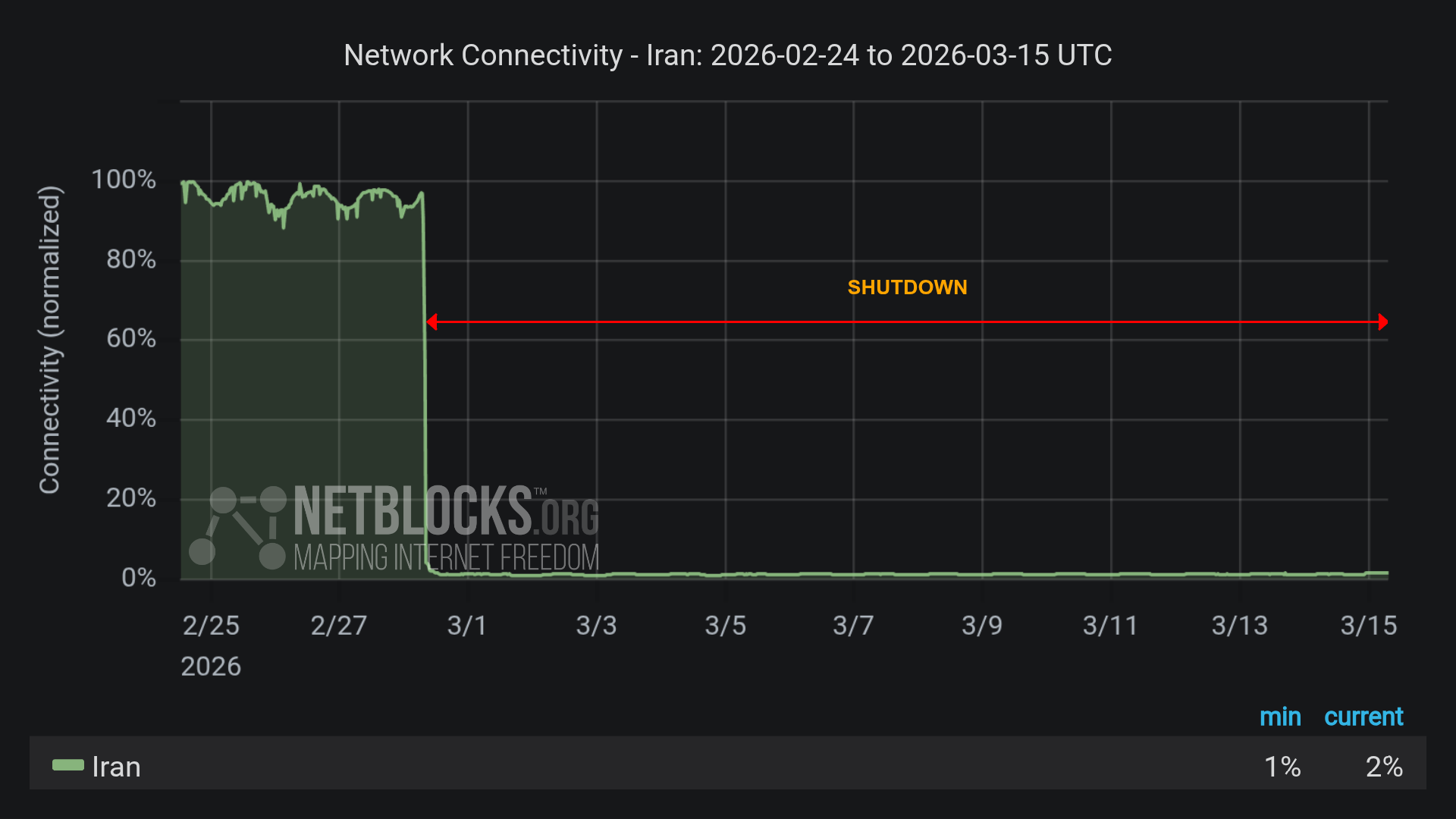
If there's one thread running through this week, it's Iran: Boggy Serpens refining its AI-enhanced espionage playbook, an attempted intrusion at Poland's nuclear research center with Iranian fingerprints, the EU hitting Iranian entities with fresh sanctions — and Iran's own population cut off from the internet for over two weeks now. Stryker is still cleaning up from last week's Handala attack too. A lot of activity from a lot of pro-Iran actors in one week.
Oh, and if you’re in SF this week for RSA, don’t forget to check awesome side events listed here: https://xsa.github.io/infosec-events/
Let’s now dive into this week’s top insights! 🚀
Table of Contents
🔓 BREACHES & SECURITY INCIDENTS
🇫🇷 🏃♂ 📍 A French Navy officer logged a run on the deck of the Charles de Gaulle and uploaded it to Strava, revealing the carrier’s exact location. Strava defaults to public, and similar data has exposed military movements before. The French Armed Forces said the officer broke guidelines, and users should consider setting accounts to private.
🇺🇸 🚗 A cyberattack on breathalyzer firm Intoxalock has left drivers across the U.S. unable to start their cars — The company paused systems and cannot perform required device calibrations. Intoxalock did not disclose attack details or a recovery timeline.
🇺🇸 Security researcher Jeremiah Fowler found publicly exposed Sears chatbot databases that contained millions of chat logs, audio files, and transcripts with customers' names, addresses, and phone numbers. Some recordings lasted hours and captured private conversations, raising risks of phishing and fraud. Transformco (the company that owns Sears and Sears Home Services) secured the data after being notified, but it’s still unclear who else accessed it.
🇺🇸 Intuitive Surgical said it was hit by a targeted phishing cyberattack that exposed some internal business and contact data. The company says its surgical robots, manufacturing systems, and hospital networks were not affected. The breach is contained, regulators are being notified, and no timeline or attacker details were given.
🇺🇸 Marquis says hackers stole personal and financial data from at least 672,075 people in an August 2025 ransomware attack. Stolen data included names, birth dates, addresses, bank and card numbers, and Social Security numbers. Marquis blames a SonicWall security failure that let attackers access its network and deploy ransomware.
🇺🇸 Stryker is restoring its internal systems after a cyberattack that wiped thousands of employee devices. A pro‑Iran group called Handala claimed responsibility and said it used company admin access to remotely erase laptops and phones. The breach disrupted operations but Stryker says its internet‑connected medical devices are safe.
🤔 ⁉ Several major companies named by the Cl0p ransomware group in the Oracle E-Business Suite hack have not commented on the breach — Broadcom, Bechtel, Estée Lauder, and Abbott remain silent despite torrents claiming large amounts of stolen data. Companies may stay quiet for legal, strategic, or investigatory reasons.
🇬🇧 Companies House fixed a security flaw in its WebFiling service that exposed data for up to five million U.K. companies. The bug, introduced in October 2025, let logged-in users view other companies' dashboards and some non-public details like dates of birth and addresses. The agency says no passwords or identity documents were accessed, has reported the incident, and is investigating.
🇨🇦 Canadian retailer Loblaw says a criminal third party accessed customer names, email addresses, and phone numbers. The company says passwords, health details, credit card data, and PC Financial were not affected. It is unclear how many customers were impacted.
🇬🇧 The Guardian found that sensitive UK Biobank health data from 500,000 volunteers has been leaked online many times. Researchers accidentally posted datasets to sites like GitHub, exposing diagnoses and dates that could allow re-identification. Biobank says no names were shared and has issued takedown notices, but experts warn privacy risks remain.
→ More:
🥷🏻 CYBERCRIME, CYBER ESPIONAGE, APT’s
🇺🇸 🤑 A former Brightly Software contractor stole payroll and corporate data and then sent over 60 extortion emails demanding $2.5 million. Brightly paid $7,540 in Bitcoin and reported the theft, leading the FBI to seize devices and charge 27-year-old Cameron Curry. He faces up to 12 years in prison for the extortion scheme.
🇷🇺 🇺🇦 A Russian state-sponsored group has exploited a high-severity XSS flaw in Zimbra to attack Ukrainian targets. The bug lets malicious CSS/JavaScript in email steal credentials, session tokens, 2FA backups and mailbox data. CISA added the flaw to its KEV list and urges immediate patching of Zimbra.
🇮🇷 Researchers found Iran-linked cyber groups built and staged hidden infrastructure for months before the Feb 28, 2026 US/Israeli strikes. After the strikes, about 60 coordinated hacktivist and APT groups launched attacks mainly against US, Israeli, and Gulf targets. Kinetic strikes damaged Iranian internet links but did not stop or seriously degrade Iran’s cyber capabilities.
🇨🇳 👀 China-linked hackers have run a patient cyberespionage campaign against Southeast Asian militaries since at least 2020. They used custom tools (AppleChris, MemFun, Getpass), PowerShell, and DLL hijacking to stay hidden and steal sensitive military files. Evidence like time-zone patterns, Chinese infrastructure, and Simplified Chinese suggests the group operates from China.
🇰🇭 Cambodia says it will close all online scam centers within weeks. Authorities have opened dozens of cases, arrested hundreds, and repatriated nearly 10,000 workers. Experts warn past raids left networks intact and say key beneficiaries may not be targeted.
🎣 A convicted scammer, Kwamaine Jerell Ford, is accused of running a new phishing scheme from prison by impersonating an adult film star. He allegedly tricked professional athletes into giving iCloud logins and MFA codes, then stole their data and charged many fraudulent transactions. Prosecutors also say he coerced an OnlyFans model into sex acts and used videos to target more victims; he faces 22 charges and is held without bail.
→ More:
🗓️ {Cyber,Info}Sec Events — A community-maintained list of infosec conferences worldwide. Subscribe to the ICS calendar feed to get events straight into your calendar, or follow @[email protected] on Mastodon for weekly digests. Contributions and ⭐ welcome!
👨🏻⚖️ 👀 GOVERNMENT, POLITICS, AND PRIVACY
🇮🇹 💰 Cloudflare appealed a €14.2M fine from Italy for refusing to block sites via its 1.1.1.1 DNS service. The company says Italy’s Piracy Shield forces rapid, opaque blocking that breaks Internet architecture and risks widespread overblocking. Cloudflare is fighting the law in Italian courts and with EU regulators.
🇺🇸 National Cyber Director Sean Cairncross said the Trump administration is not asking companies to carry out offensive cyberattacks — Instead, the government wants private firms to share technical threat information so officials can respond. The FBI also says companies should report breaches and work with law enforcement to disrupt attackers.
🇺🇸 💰 The FBI confirmed it has resumed buying Americans’ location and other data from commercial data brokers to aid investigations. Critics say this lets agencies bypass warrant requirements and may violate the Fourth Amendment. Lawmakers have proposed a bill to require court warrants before agencies can buy people’s data.
🇪🇺 🇨🇳 🇮🇷 The EU sanctioned three companies and two individuals from China and Iran for major cyberattacks. One Chinese firm helped hack over 65,000 devices and another offered hacking-for-hire services. The Iranian company ran influence operations, stole subscriber data, and spread misinformation at the 2024 Paris Olympics.
🇪🇺 🗳 The European Parliament voted to ban untargeted mass scanning of private messages — Scans will be allowed only when a judge names specific users or groups suspected of child sexual abuse. Lawmakers extended a temporary CSAM rule until August 3, 2027, while negotiations continue.
🦠 MALWARE & THREATS
🐍 Researchers uncovered Speagle, malware that hijacks the Cobra DocGuard security program to steal data. It hides exfiltration by using compromised Cobra servers and a legitimate driver. The attack appears targeted, possibly for espionage, and may stem from a supply-chain compromise.
🔎 📄 Perseus is new Android malware that steals sensitive data by scanning users' note apps for passwords, recovery phrases, and financial info. It spreads via sideloaded IPTV apps and uses Accessibility Services to fully control devices, take screenshots, and hide activity. Users should avoid sideloading apps, stick to Google Play, and enable Play Protect.
🍀 Fraudsters used a legitimate Nordstrom email address to send a St. Patrick’s Day crypto scam promising to double deposits. Nordstrom warned the messages were unauthorized and said it is investigating after some customers paid. The breach likely came through an Okta SSO to Salesforce compromise, and customers are urged to ignore the promotion.
🪱 Researchers warn the GlassWorm campaign has escalated by abusing Open VSX extensionPack and extensionDependencies to turn benign-looking extensions into delivery vehicles for malware. At least 72 malicious extensions were found, mimicking developer tools and using obfuscation, invisible Unicode, and rotating Solana wallets to fetch commands and steal secrets. This tactic enables attackers to bypass review, inject malware transitively, and expand supply-chain compromises across registries and repositories.
🤑 Malicious JavaScript was delivered through the AppsFlyer Web SDK and could replace crypto wallet addresses with attacker-controlled ones. The injected code also stole the original addresses and metadata from users. AppsFlyer says the issue was contained and is investigating while customers should check logs and use known-good SDK versions.
🇺🇦 🇷🇺 A new malware campaign called DRILLAPP targets Ukrainian groups and likely links to Russian actors. It runs a JavaScript backdoor inside Microsoft Edge with special debug flags to access files, mic, camera, and screen. The attackers use paste services for control and changed tactics between February variants to improve file access and persistence.
🎣 Attackers hide phishing links and attachments by appending long blocks of benign text, links, and many HTML break lines to emails. This "noise" fools some NLP-based email security tools into seeing messages as safe. KnowBe4 found this technique often uses real signatures and links (e.g., Bank of America, Uber) to evade detection.
🎣 🇸🇪 A C-level executive at Outpost24 was targeted in a sophisticated phishing attack that used a phishing-as-a-service kit called Kratos. Attackers chained redirects through trusted services (Cisco, Nylas) and reused a reclaimed domain, then served a convincing Microsoft 365 credential-stealing page behind Cloudflare. Specops says the method fits Iran-linked group tactics but attribution remains uncertain.
🤖 🧰 AI, CRYPTO, TECH & TOOLS
☁ Bucketsquatting is (Finally) Dead — AWS added a new bucket namespace pattern (prefix-accountid-region-an) to stop bucketsquatting. This ensures only the owning account can create buckets with that name and helps prevent attacks. Use the namespace for all new S3 buckets and migrate existing ones if you need protection!
📲 ⏳ Google will add a mandatory 24-hour wait before users can sideload apps from unverified Android developers to reduce malware and scams. Power users can enable an "advanced flow" with steps like developer mode, a restart, and biometric confirmation to allow sideloading after the wait. Google will also offer limited free developer accounts for hobbyists and students while its verification rules take effect.

Figure: The Advanced Flow/Google
🎵 🤑 North Carolina musician Michael Smith pleaded guilty to using AI-generated songs and automated bots to fraudulently stream music on major platforms. He and accomplices streamed the fake tracks billions of times, collecting over $10 million in royalties. Smith agreed to forfeit about $8.09 million and faces up to five years in prison.
🙊 🤖 A Meta AI agent shared a private internal answer without permission, exposing company and user data to unauthorized engineers for two hours. The agent also gave bad advice that led to the exposure, and Meta rated it a high-severity incident.
🤝 Major tech and retail companies, including Google, Meta, Microsoft, Amazon and OpenAI, signed a pact to fight online scams and fraud. They agreed to share threat information, strengthen prevention and verification, and help users report scams. They also urged governments to make scam prevention a national priority and improve data sharing and laws.

Figure: Industry Accord Signatories/Google.com
🐛 Researchers found several serious AI security flaws: Amazon Bedrock's sandbox allows DNS-based data exfiltration and remote shells, LangSmith had a token-theft URL injection flaw fixed in v0.12.71, and SGLang contains unpatched pickle deserialization bugs that enable remote code execution. Attackers could use these issues to steal data, take over accounts, or run arbitrary code if services are misconfigured or exposed. Administrators should restrict network access, audit IAM roles, migrate to VPC mode or apply DNS firewalls, and patch or isolate vulnerable deployments.
🍏 🔄 Apple released its first background security update for iPhone, iPad, and Mac to fix a Safari WebKit bug. The bug could let a malicious website access data from another site in the same browser session. The lightweight update installs quickly and is pushed between major software releases.
🇨🇳 🦞 Chinese cybersecurity officials warned that OpenClaw, the popular open-source AI agent, has weak default security and high system privileges that attackers can exploit. Researchers showed attackers can use indirect prompt injection—like poisoned web pages or link previews—to make the agent leak sensitive data or run malicious commands. Users are urged to tighten network controls, isolate the service, avoid untrusted skills, and keep the agent updated.
🐛 🧠 VULNERABILITIES, RESEARCH, AND THREAT INTELLIGENCE
➝ From the Patching Department:

Figure: Screenshot of Mauvehed’s Toot
🔓 ☁ A critical path-traversal bug (CVE-2026-22557) in Ubiquiti’s UniFi Network Application could let attackers take over accounts by accessing files. Ubiquiti released patches and advises users to update; a second fix (CVE-2026-22558) closes a privilege-escalation flaw. About 88,000 UniFi hosts are internet-exposed, many in the U.S., raising urgent risk.
💥 A critical Langflow vulnerability (CVE-2026-33017) allowed unauthenticated remote code execution via a POST endpoint. Attackers began exploiting it roughly 20 hours after public disclosure to steal keys and credentials. Sysdig observed multi-stage attacks from several IPs leading to data exfiltration and possible supply-chain risk.
📸 🔓 Researchers found three serious flaws in Xiaomi camera setup protocol that let attackers bypass setup, predict crypto randomness, and trigger a heap overflow. Using these bugs they achieved remote root code execution and built a persistent “cloud jailbreak.” The jailbreak lets attackers control the camera, steal Wi‑Fi credentials, and cut the device off from Xiaomi cloud services.
😬 Cisco has had a recent flood of SD‑WAN and firewall vulnerabilities, and many were already being actively exploited — Attackers, including ransomware group Interlock, used zero‑days and other flaws to gain powerful management‑plane access. Researchers warn this shows attackers target network edge systems for broad, long‑lasting control.
🍎 🇷🇺 Researchers found a second iOS exploit kit, called Darksword, likely reused by suspected Russian hackers from tools originally made for the U.S. government. Darksword can steal passwords, crypto wallets, messages, and may be used for both money and surveillance, putting up to hundreds of millions of iPhones at risk. The kit shows use of AI-generated code and poor operational security, and researchers warn a growing secondary exploit market now targets mobile devices.

Figure: Timeline of DarkSword observations and vulnerability patches/cloud.google.com
🐧 A critical buffer-overflow bug in GNU InetUtils telnetd (CVE-2026-32746) lets unauthenticated attackers run code as root via port 23. The flaw is triggered during the initial Telnet handshake and affects versions through 2.7; a fix is expected by April 1, 2026. Until patched, disable Telnet, block port 23, or run telnetd without root to reduce risk.
🔎 🐛 RondoDox’s operators expanded their exploit list to 174 vulnerabilities and now track disclosures to strike before CVEs are assigned. They shifted from broad scanning to a more targeted exploitation strategy to increase successful infections. The botnet uses its own infrastructure to deploy evasive implants and mainly focuses on DDoS campaigns rather than mass propagation.
🛰️ ICS, OT & IoT
🇺🇸 🇨🇦 🇩🇪 U.S., Canadian and German authorities disrupted four large IoT botnets that had infected over three million devices and launched massive DDoS attacks. The botnets—Aisuru, Kimwolf, JackSkid and Mossad—sent hundreds of thousands of attack commands and were used for extortion. Investigators seized servers and domains and targeted alleged operators in coordinated international actions.
☁ 🔓 Researchers found serious security flaws in low-cost IP KVM devices from four manufacturers. These small gadgets let users control machines at the BIOS/UEFI level. If exposed to the Internet, misconfigured, or compromised, they can give insiders or hackers wide network access.
🇵🇱 Poland’s National Centre for Nuclear Research (NCBJ) was targeted in a recent cyberattack that was stopped before any systems were compromised. Officials say early indicators point to Iranian-linked hackers, but they warn the evidence could be misleading. This follows a separate cyber incident on Poland’s power grid two months earlier.
💬 CONNECT
Follow me on Mastodon for quick daily updates and bite-sized content.
Prefer using an RSS feed? Add Infosec MASHUP to your feed here.
Enjoying our newsletter? Forward it to a colleague—
it’s one of the best ways to support us.
Thanks for reading today’s newsletter, and if you're enjoying it and want to support my work, you can buy me a coffee ☕ over at https://www.buymeacoffee.com/0x58
See you next time!
-X.
1