We now have {{active_subscriber_count}} subscribers! Thank you all for being part of my newsletter. Please share it with your friends and colleagues, and let’s keep growing the community.
Let’s now dive into this week’s top insights! 🚀
Table of Contents
🔓 BREACHES & SECURITY INCIDENTS
🇬🇧 Royal Mail Group suffered a significant data breach, with 144GB of sensitive information stolen and shared by a hacker known as “GHNA.” The breach, linked to a 2021 malware infection of a third-party employee, exposes customer details, internal documents, and operational data. This incident highlights the ongoing risks of supply chain vulnerabilities and the increasing threat posed by AI in cybercrime.
🗣️ Oracle is facing backlash for mishandling two data breaches, including one involving patient data from its healthcare subsidiary, Oracle Health. Despite reports of breaches, Oracle has denied any wrongdoing and has been criticized for a lack of transparency. Cybersecurity experts are urging the company to communicate clearly about the incidents to regain customer trust. [More on Bloomberg.com]
🇺🇸 A data breach at Chord Specialty Dental Partners has affected over 170,000 people due to unauthorized access to employee email accounts. The breach exposed personal information, including names, addresses, and financial details. Chord is offering credit monitoring services to those impacted, but has not confirmed any misuse of the data.
🔗 Partners and Affiliates
🔐 NordVPN Spring Campaign 🌷 (March 19 — May 19)
With its user-friendly interface, robust security features, and commitment to privacy, NordVPN continues to be a popular choice for individuals seeking online protection and unrestricted internet access.
Special Offer: up to 77% off + 3 extra months on selected 2-year plans.
🥷🏻 CYBERCRIME, CYBER ESPIONAGE, APT’s
❌ Europol has dismantled Kidflix, a streaming platform that offered child sexual abuse material, seizing 72,000 videos in a major operation called Operation Stream. The investigation involved 38 countries and identified 1,393 offenders, with 79 arrests made so far. Kidflix had about 1.8 million users and allowed payments in cryptocurrency for accessing its content.

Figure: Website Seizure Banner/europol.int
🇺🇸 The U.S. Department of Justice has charged Canadian hacker Aubrey Cottle, known as "Kirtaner," for defacing the Texas Republican Party's website in 2021 and stealing personal data. Cottle allegedly accessed the site through a breach and later released the stolen data online. He faces up to five years in prison for identity theft and has claimed his actions were political activism against far-right extremism.
🇺🇸 The U.S. Department of Justice seized over $8.2 million in cryptocurrency tied to 'romance baiting' scams, where victims are tricked into investing in fake platforms. Many victims, including five from different states, lost a total of over $5.2 million, with one individual losing around $663,352. The scammers are believed to be linked to human trafficking groups in Cambodia and Myanmar, using manipulation and threats to extort more money from their victims.
🗓️ {Cyber,Info}Sec Events: My list of past and future {cyber,info}sec related events — Feel free to contribute by submitting issues or pull requests. Thanks! 😉
👨🏻⚖️ 👀 GOVERNMENT, POLITICS, AND PRIVACY
🇺🇸 ⚖️ A U.S. federal judge has allowed a lawsuit against the Department of Government Efficiency (DOGE) and Elon Musk to continue. The lawsuit, led by the Electronic Frontier Foundation and two labor unions, aims to stop the government from sharing personal records of millions of Americans. The judge's ruling means the case can move forward, but it does not guarantee a win for the plaintiffs.
🇺🇸 🎓 Senate Minority Leader Chuck Schumer is proposing a new bill to provide security training for Trump's White House staff after the Signalgate scandal. The bill, called the Operational Security (OPSEC) Act of 2025, aims to improve how officials handle classified information. Schumer's plan includes creating a new office for training and oversight by Congress to prevent future security issues.
🇺🇸 📍 T-Mobile's tracking app, SyncUP, mistakenly showed some parents the real-time locations of random children instead of their own. One parent, Jenna, expressed concern after seeing the locations and names of other kids, while she couldn't track her own children. T-Mobile acknowledged the issue but has not yet provided a solution, and other users have reported similar problems with the app.
🇺🇸 National Security Adviser Michael Waltz and his team used personal Gmail accounts for government communications, raising concerns about data security. This practice was highlighted after a journalist was mistakenly included in a sensitive group chat discussing military operations. Despite the controversy, President Trump has chosen not to fire Waltz, citing a desire to avoid giving media critics a victory.
🇪🇺 🇺🇸 Apple has been fined €150 million by France's competition authority for unfair practices related to its App Tracking Transparency (ATT) framework. The regulator found that Apple's consent process for tracking users was too complex and favored its own apps over third-party ones. Despite the fine, Apple claims that its ATT prompt is consistent and has support from consumers and privacy advocates.

Figure: The ATT Framework/autoritedelaconcurrence.fr
🇪🇺 The European Union will invest €1.3 billion in cybersecurity, artificial intelligence, and digital skills from 2025 to 2027. This funding will strengthen cyber resilience for critical infrastructures like hospitals and support the new Digital Identity Wallet. Additionally, it will enhance access to AI applications and improve digital skills training.
🤷🏻♂️ Why? A prominent computer scientist named Xiaofeng Wang has gone missing and his contact information has been removed by Indiana University. The FBI has raided his homes, but the reason for this action is unclear. Wang is known for his work in cryptography and cybersecurity and has been a respected figure at the university for over 20 years.
🔗 Partners and Affiliates

🌐 Stay connected and secure on the go with Airalo's global eSIMs — Use the code NEWTOAIRALO15 if you’re new to Airalo to get an additional 15% discount.
🦠 MALWARE & THREATS
🐧 Researchers have identified a malware called Outlaw that targets Linux servers using SSH brute-force attacks to install cryptojacking software. This malware can spread itself and maintain control over infected systems by adding its own SSH keys. Outlaw has been active since at least late 2018 and uses various techniques to exploit vulnerabilities and evade detection.
🇺🇦 CERT-UA has reported multiple cyberattacks targeting Ukrainian state systems, using phishing emails to steal sensitive data. The attacks involved links to legitimate services that download malware called WRECKSTEEL, which collects files and captures screenshots. These incidents are part of an ongoing campaign attributed to a threat group known as UAC-0219.
🇷🇺 🇺🇦 Russian hacking group called Gamaredon is using phishing tactics to distribute a malware known as Remcos RAT to targets in Ukraine. They disguise malicious files as Microsoft Office documents related to troop movements to trick recipients into opening them. This campaign aims to gather personal information and conduct espionage against Ukrainian organizations.
🇷🇺 Russian hacking group called Water Gamayun is exploiting a security vulnerability in Microsoft Windows (CVE-2025-26633) to deliver two new types of malware named SilentPrism and DarkWisp. They use malicious files disguised as legitimate software to gain access to victims' systems and steal sensitive data. Their tactics involve advanced techniques to maintain control and avoid detection while executing various malicious operations.
🧩 Hackers are using the "mu-plugins" directory in WordPress to hide malicious code, allowing them to take control of sites and redirect visitors to fake websites. This method is concerning because mu-plugins are not visible in the usual plugin interface, making them harder to detect during security checks. Site owners should keep their plugins updated and regularly check for malware to protect against these threats.
🐊 A new Android banking trojan called Crocodilus can take over devices and steal personal data. It uses advanced techniques like remote control, keylogging, and overlay attacks to capture sensitive information, including one-time passwords. The malware targets users in Spain and Turkey, allowing attackers to perform fraudulent transactions using stolen credentials.
🤖 🧰 AI, CRYPTO, TECH & TOOLS
🔐 Is Androind getting a Lockdown Mode? Android 16 introduces Advanced Protection Mode, which blocks sideloading, disables 2G connections, and enables Memory Tagging Extension for better security. This feature is designed for users at high risk of hacking and enhances their protection by requiring a security key for Google account sign-ins. It also allows apps to implement additional security measures, improving overall safety on Android devices.
🔐 Secret Protection: In 2024, GitHub reported 39 million leaked secrets, highlighting the frequent accidental exposure of sensitive information in code. To help protect these secrets, GitHub introduced new standalone security products, including Secret Protection, which is free for public repositories. Organizations can now assess their code security and prevent leaks without needing to upgrade to more expensive plans.
💰 Fedi: The Nivenly Foundation has launched a new security fund to protect the fediverse by rewarding individuals who report security vulnerabilities in apps like Mastodon and Pixelfed. The fund offers payouts based on the severity of the vulnerabilities, encouraging responsible disclosure to keep users safe. This initiative aims to educate project leaders on best security practices and reduce the need for drastic measures like defederation.
🇨🇳 A new report reveals that five VPN apps in the App Store are linked to the Chinese military, with three of them having over a million downloads. These apps are associated with Qihoo 360, a company sanctioned by the US for military ties. Apple has removed two of the apps, but the status of the remaining three is still uncertain.
🤖 Autonomy: Agentic systems, which often use large language models, can be risky if untrusted data is introduced, potentially leading to adversary-controlled actions. NVIDIA’s Agentic Autonomy framework helps assess these risks and implement security measures based on the complexity of the system. By classifying systems into different autonomy levels, it becomes easier to identify risks and apply appropriate security controls.
🔗 Partners and Affiliates
⚡️ Unlock Your Peak Performance – First Month FREE!
Optimize your sleep, recovery, and performance with WHOOP. Perfect for cybersecurity pros who need to stay focused and ahead of the threat. Try it out, get a free WHOOP 4.0 and one month free.
🪳 🧠 VULNERABILITIES, RESEARCH, AND THREAT INTELLIGENCE
➝ From the Patching Department:
🩹 Fix of the Fix: Google's Quick Share had vulnerabilities that allowed attackers to bypass user approval and execute malicious actions. Although Google issued patches, cybersecurity firm SafeBreach found that these fixes were incomplete, leaving the application still vulnerable to attacks. A new fix has been rolled out, resolving all identified issues in Quick Share for Windows.
🧨 24k, not Gold: GreyNoise has reported a significant increase in login scanning attempts on Palo Alto Networks' systems, with nearly 24,000 unique IP addresses involved. This activity suggests a coordinated effort to find vulnerabilities, potentially indicating new threats on the horizon. Organizations using these products are advised to secure their login portals and review their security logs.

Figure: Spike in Scanning/greynoise.io
🧳 A mysterious individual is offering cybersecurity experts up to $100,000 a month to hack Chinese websites. The recruiter, using fake accounts, claims to work for the Indian government and asks for web shells from any Chinese domains. Experts are confused by the bizarre recruitment tactics and speculate that it may be a troll or a cover for a different malicious intent.
🇰🇵 Skills Shortage? DPRK IT workers are expanding their operations globally, particularly in Europe, while posing as legitimate remote employees. They use deceptive tactics to infiltrate companies and are increasingly engaging in extortion against larger organizations. The rise of these workers poses significant risks to businesses, especially those using bring-your-own-device policies that lack traditional security measures.
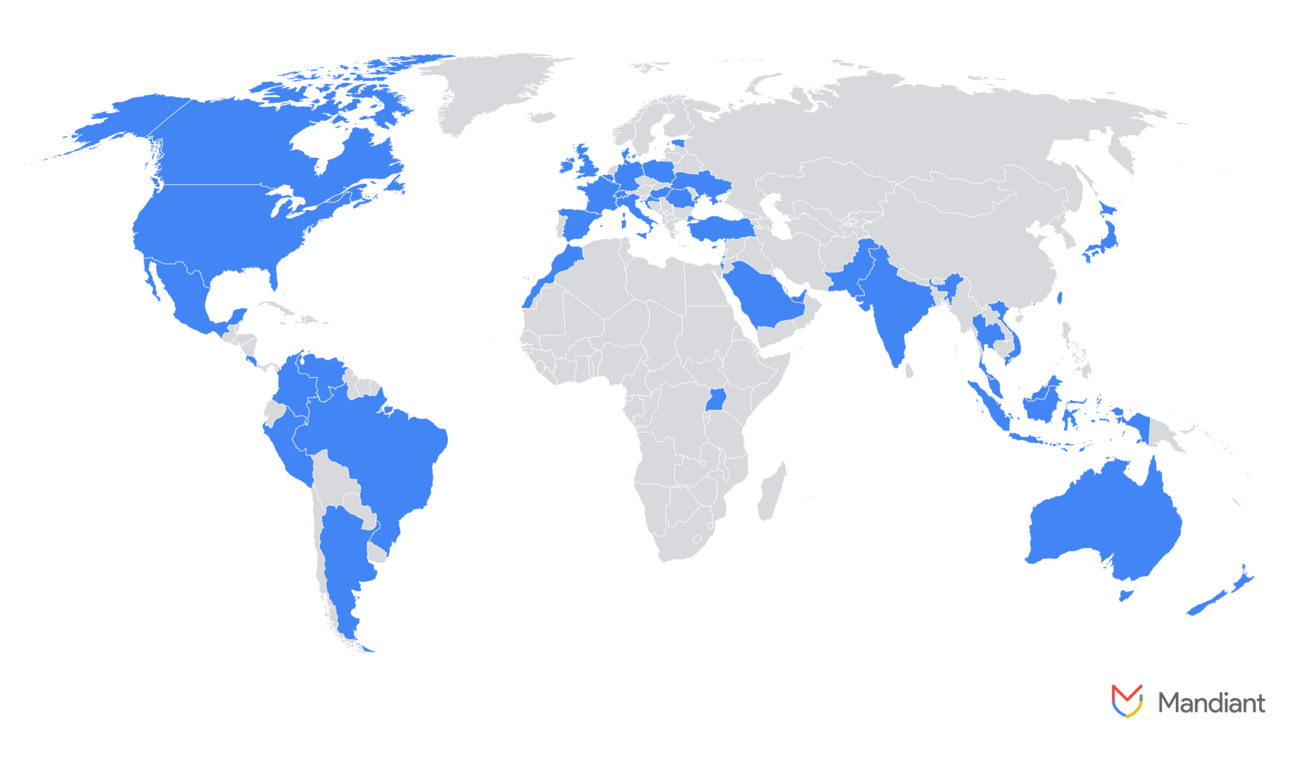
Figure: List of countries impacted by DPRK IT workers/cloud.google.com
🐛 💥 Unhappy: CrushFTP reported that a recently fixed vulnerability is being exploited by attackers, with many unpatched instances still in use. The company criticized security firms for quickly releasing details about the flaw, which led to its rapid exploitation. CrushFTP urges users to update their software to protect against these attacks.
🛰️ ICS, OT & IoT
Nothing this week 🤷🏻♂️🤷🏻♂️
💬 CONNECT
Follow me on Mastodon for quick daily updates and bite-sized content.
Prefer using an RSS feed? Add Infosec MASHUP to your feed here.
Thanks for reading today’s newsletter, and if you're enjoying it and want to support my work, you can buy me a coffee ☕ over at https://www.buymeacoffee.com/0x58
See you next time!
-X.




