The story that should not get buried under this week's patch pile is a quiet one from the ICS/OT section: attackers used Claude and ChatGPT to assist an intrusion into a water utility in Monterrey. The OT breach ultimately failed — but that's almost beside the point. What the Dragos report actually documents is AI being used as a competent recon assistant: autonomously identifying a vNode SCADA/IIoT interface, recommending a password-spray attack, and generating a Python toolkit on the fly. No novel exploit. No nation-state budget. Just patience and a chat window.
This is the part of the AI-in-security conversation that tends to get lost between the breathless vendor marketing and the "fully autonomous AI attacks are not yet observed" reassurances. The threat doesn't need to be autonomous to be meaningful. Lowering the reconnaissance floor — making OT infrastructure more legible to attackers who previously lacked the domain knowledge to navigate it — is already a significant capability shift. The Monterrey incident didn't succeed. The next one will be run by someone who learned from it.
Let’s now dive into this week’s top insights! 🚀
Table of Contents
🔓 BREACHES & SECURITY INCIDENTS
🇪🇸 👗 Hackers stole data from Zara-related databases, exposing information for about 197,400 people — The breach came from a former tech provider and reportedly included emails, locations, purchases, and support tickets. The ShinyHunters group claims responsibility and leaked a 140GB archive.
🔓 Trellix says part of its source code repository was breached but gave few details — They are investigating with forensic experts and have notified law enforcement. The incident may be linked to a wider supply-chain campaign tied to groups like TeamPCP and Lapsus$.
🎓 Education tech company Instructure says a cyberattack exposed user data — The extortion group ShinyHunters claims it stole hundreds of millions of records and listed Instructure on its leak site. Instructure is investigating, patching systems, and asking customers to reauthorize API access.
🥷🏻 CYBERCRIME, CYBER ESPIONAGE, APT’s
🦶 🍑 Hackers have been breaking into systems already compromised by a cybercrime group called TeamPCP and kicking TeamPCP out. The new group, dubbed PCPJack, then steals credentials and spreads across cloud services to sell access or extort victims. Researchers think PCPJack aims to make money and may be rival hackers or ex-TeamPCP members.
🇨🇦 💬 Toronto police arrested three men and laid 44 charges for running an SMS blaster that sent spammy, phishing texts to tens of thousands of devices across the city. The device spoofed cell towers, exploited old 2G networks, and was operated from the back of a vehicle to steal logins and disrupt phone and 911 service. Authorities say turning off 2G or using Lockdown Mode on Apple devices can block such attacks.
🇺🇸 ⚖ Two American men were jailed for 18 months for hosting laptop farms that let North Korean IT workers pose as U.S.-based employees. Their schemes affected about 70 U.S. companies and funneled roughly $1.2 million to the regime. Authorities say these cases show they will punish people who help North Korea evade sanctions and steal from U.S. firms.
🇷🇴 ⚖ 🇺🇸 A 53-year-old Romanian, Gavril Sandu, was extradited to the U.S. for a 2009–2010 hacking and vishing scheme. He is accused of stealing financial data, cloning cards, and withdrawing funds as a money mule. Sandu faces up to 30 years in prison after a 17-year gap between the crimes and his extradition.
🫥 🇮🇷 Iran-linked APT MuddyWater staged an intrusion that looked like a Chaos ransomware attack but did not encrypt files. Attackers used social engineering via Microsoft Teams, AnyDesk and DWAgent to steal credentials, move laterally, and exfiltrate data. Chaos artifacts were likely false flags to hide state-sponsored espionage.
🇹🇼 🚅 A 23-year-old Taiwanese student was arrested for triggering emergency brakes on four high-speed trains by hacking the TETRA radio system using SDR equipment and handheld radios. The attack halted trains for 48 minutes and exploited unchanged radio parameters that allowed impersonation. He faces up to 10 years in prison and is out on bail while authorities investigate.
🇱🇻 ⚖ 🇺🇸 A Latvian national, Deniss Zolotarjovs, was sentenced to 8.5 years in the U.S. for helping the Karakurt ransomware gang extort dozens of companies. He negotiated “cold case” extortions and used stolen personal and health data to pressure victims. Authorities say his actions contributed to losses likely in the hundreds of millions and could lead to more prosecutions.
🗓️ {Cyber,Info}Sec Events — A community-maintained list of infosec conferences worldwide. Subscribe to the ICS calendar feed to get events straight into your calendar, or follow @[email protected] on Mastodon for weekly digests. Contributions and ⭐ welcome!
👨🏻⚖️ 👀 GOVERNMENT, POLITICS, AND PRIVACY
🇺🇸 👀 Rep. Summer Lee asked the Commerce Department for a briefing on U.S. use of commercial spyware after ICE admitted using Paragon’s Graphite. She is worried the Trump administration and U.S. investors may enable use of NSO Group’s Pegasus. Lawmakers cite past abuses and want details on communications and potential federal use.
🇺🇸 📍 ⚖ Kochava agreed to stop selling sensitive location data to settle an FTC lawsuit — The proposed order bans sharing location info tied to places like clinics, churches, shelters and daycares without users' clear consent. The company must verify suppliers' permissions, let people see who bought their data, and allow easy opt-out.
🔎 🇺🇸 🩺 An investigation found nearly all 20 state health insurance marketplaces shared applicants’ data with ad tech companies like Google, Meta, LinkedIn, Snap, and TikTok. Trackers on these sites exposed sensitive details, including race, sex, ZIP codes, and family incarceration information. Some states removed or paused trackers after the findings, highlighting widespread privacy risks on government health sites.
🇪🇺 ❌ 💰 🇨🇳 The European Commission will block EU funding for solar panel inverters from high-risk suppliers like Huawei. Officials say this aims to prevent foreign interference that could disrupt electricity grids. China, Russia, North Korea and Iran are affected, with Chinese firms holding about 80% of the inverter market.
🇪🇺 👀 The EFF urges the EU’s Digital Fairness Act to stop manipulative design and surveillance-driven business models. They want stronger privacy protections, bans on dark patterns, and limits on data profiling and pay-for-privacy. The law should also boost user control by preventing lock-in, unfair post-sale restrictions, and promoting interoperability.
🦠 MALWARE & THREATS
🇺🇸 🎣 Microsoft warned of a sophisticated phishing campaign that used fake "code of conduct" emails to lure victims to malicious sites. The attacks targeted mostly U.S. organizations, hitting healthcare, finance, professional services, and tech, with over 35,000 attempts. The scheme uses CAPTCHAs and an adversary-in-the-middle trick to steal session tokens and bypass MFA.

Figure: Campaign recipients by country and industry/Microsoft.com
🐧 A new Linux malware called Quasar Linux (QLNX) targets developers and DevOps environments to steal credentials and persist stealthily. It uses a dynamic rootkit, PAM backdoors, fileless techniques, and seven persistence methods to hide and maintain access. By harvesting developer and cloud credentials, it can enable supply-chain attacks like trojanized packages.
🇨🇳 🔙 🚪 Kaspersky says a backdoor was planted in the Windows disc tool Daemon Tools in a widespread supply-chain attack. The company links the attack to a Chinese-language hacking group that used the backdoor to install further malware on targeted organizations in Russia, Belarus and Thailand. Disc Soft is investigating while the attack appears still active and thousands of users may be at risk.
🇰🇵 🎮 North Korea-linked ScarCruft hacked a gaming platform used by ethnic Koreans and inserted the BirdCall backdoor. The supply-chain attack added an Android strain so BirdCall now targets both Windows and Android. The malware steals files, messages, screenshots, and audio and uses cloud services for command-and-control.
💬 📲 A new CloudZ RAT plugin called Pheno hijacks Microsoft Phone Link on Windows to steal SMS messages and one-time passwords without touching the phone. Researchers found Pheno reads Phone Link’s local SQLite database to intercept codes and notifications. Users should avoid SMS OTPs and use authenticator apps or hardware keys.
🐍 🔙 🚪 China-linked group Silver Fox used tax-themed phishing to target organizations in India, Russia and other countries. Phishing emails delivered a Rust-based loader that installed ValleyRAT and a new Python backdoor called ABCDoor. ABCDoor gives attackers persistence, remote control, data theft, and updates via HTTPS.
🤖 🧰 AI, CRYPTO, TECH & TOOLS
🤔 A researcher found that Microsoft Edge decrypts and loads all saved passwords into memory at startup. This means plaintext credentials can remain in system memory for the whole browser session. The risk is mainly to systems where an attacker already has high privileges, and Microsoft says this behavior is intentional.
🐛 A critical unauthenticated bug in Ollama (CVE-2026-7482 aka Bleeding Llama) lets attackers read heap memory and steal sensitive data like prompts, API keys, and environment variables. About 300,000 internet-accessible Ollama deployments are exposed because the service often runs without authentication and listens on all interfaces. Update to Ollama 0.17.1, restrict network access, and add authentication or a proxy immediately.
⬇ Google Chrome quietly writes a 4 GB AI model file to users' profiles without asking — This download happened automatically on many devices and can fill disks or consume months of mobile data. This mass push raises privacy, transparency, legal, and climate concerns and calls for clear notices, easy removal, and reporting of the environmental cost.
🇷🇺 💸 A popular crypto exchange called Grinex shut down after a reported cyberattack and lost about $13 million — Experts say Russian sanctions evasion will keep using new platforms and a ruble-pegged stablecoin called A7A5. The takedown adds friction but won’t stop the shadow finance networks.
🇺🇸 🪖 🤖 The Pentagon made deals with seven tech firms so their AI can be used on classified military networks. The tools aim to help with decision-making, targeting, and logistics but raise concerns about oversight, privacy, and civilian harm. One major AI company, Anthropic, is absent after a dispute over limits on military use.
🐛 🧠 VULNERABILITIES, RESEARCH, AND THREAT INTELLIGENCE
➝ From the Patching Department:
🐧 A new unpatched Linux kernel flaw called Dirty Frag lets local users gain root on many major distributions — It chains two page-cache write bugs (xfrm-ESP and RxRPC) so it works in different environments. A one‑command PoC exists, and admins should block esp4, esp6, and rxrpc until patched.
💥 📆 A critical PAN-OS firewall zero-day (CVE-2026-0300) has been exploited for nearly a month to run code as root on exposed PA- and VM-series devices. Attackers used EarthWorm and ReverseSocks5 to tunnel and maintain access, and they cleaned logs after compromising devices. Palo Alto is issuing patches soon and urges admins to restrict or disable the User-ID Authentication Portal until fixed.
🐛 The vm2 Node.js library has a dozen critical vulnerabilities that let attackers break out of its JavaScript sandbox and run arbitrary code on hosts. Affected versions up to 3.11.1 are patched across updates, with the latest fix in 3.11.2. Users should update vm2 immediately to stay protected.
👿 A critical FreeBSD DHCP client bug (CVE-2026-42511) lets a local attacker run code as root by sending crafted DHCP data. It affects all supported FreeBSD versions and can fully compromise systems when a rogue DHCP server is on the same network. FreeBSD has released patches—admins should update immediately or enable DHCP snooping to block rogue servers.
💥 The critical cPanel authentication bypass (CVE-2026-41940) was actively exploited from about Feb 23, 2026, but only publicly disclosed on April 28. Around 1–1.5 million internet-facing cPanel hosts were potentially vulnerable, and many were quickly used in ransomware and botnet campaigns. Any server accessible without firewalling between Feb 23 and Apr 28 should be treated as possibly compromised and fully investigated.
🌱 💥 A critical unauthenticated RCE bug (CVE-2026-22679) in Weaver E-cology was exploited from mid-March to run discovery commands and fetch PowerShell payloads. Attackers used an exposed debug API to execute system commands but failed to gain persistence. Users should install the vendor update (build 20260312) immediately.
🛰️ ICS, OT & IoT
🇵🇱 🚰 Poland’s Internal Security Agency reports a rise in cyberattacks on industrial control systems at water treatment plants in 2024–2025. Attackers exploited weak passwords and internet-exposed systems to alter equipment and risk water supplies in five municipalities. ABW blames foreign-linked hacktivist/APT groups, including Russia-linked APT28/APT29 and Belarus-linked UNC1151.
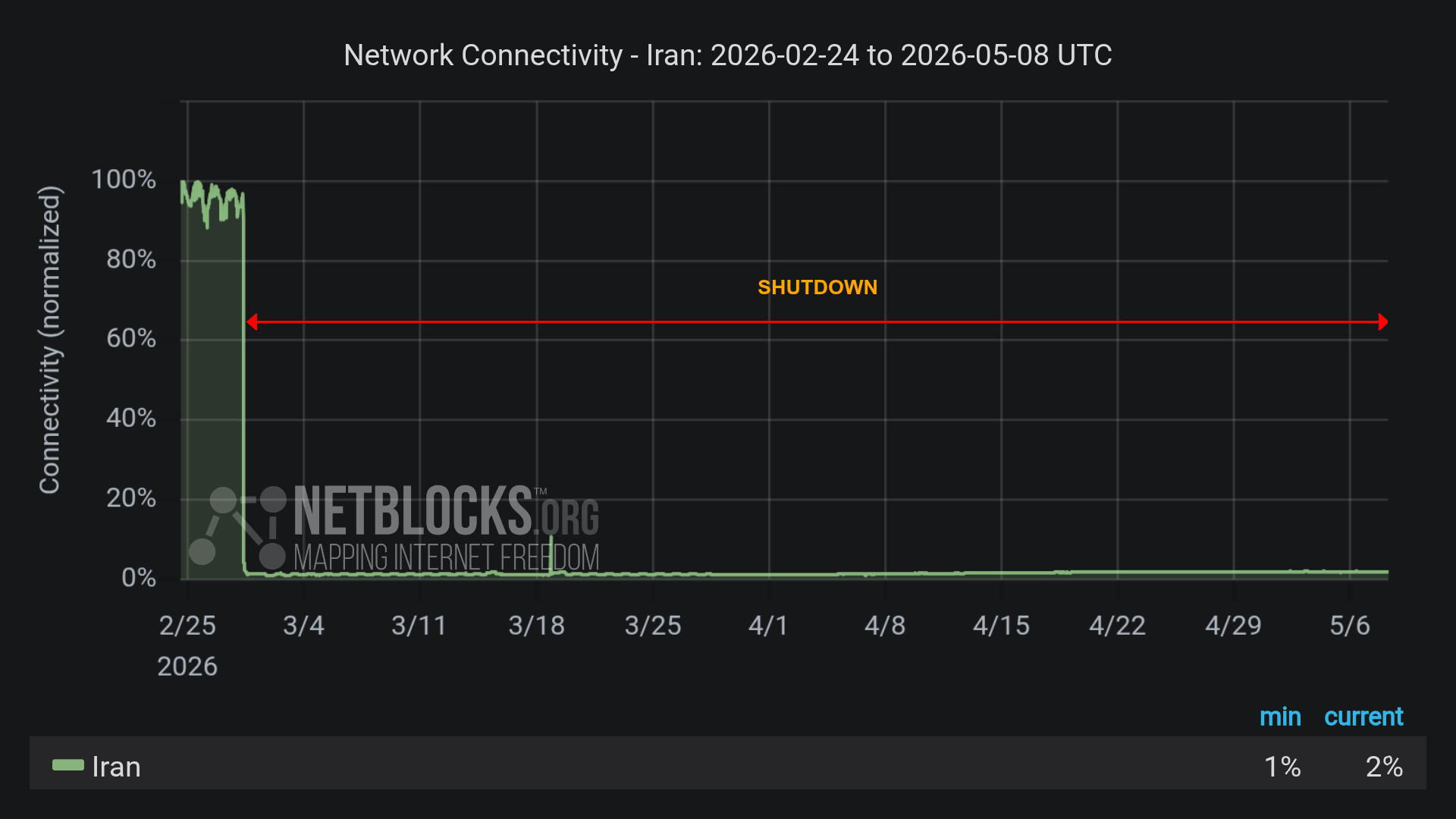
🤖 🚰 Cyber attackers used Anthropic’s Claude and OpenAI GPT to plan and speed up an intrusion into a Monterrey water utility in January 2026. Claude autonomously found a vNode SCADA/IIoT interface, recommended a password-spray attack, and helped build a large Python toolkit, though the OT breach failed. Dragos warns AI can make industrial systems more visible to attackers even if fully autonomous attacks are not yet observed.
💬 CONNECT
Follow me on Mastodon for quick daily updates and bite-sized content.
Prefer using an RSS feed? Add Infosec MASHUP to your feed here.
Enjoying our newsletter? Forward it to a colleague—
it’s one of the best ways to support us.
Thanks for reading today’s newsletter, and if you're enjoying it and want to support my work, you can buy me a coffee ☕ over at https://www.buymeacoffee.com/0x58
See you next time!
-X.