We now have {{active_subscriber_count}} active subscribers! Thank you all for being part of my newsletter. Please share it with your friends and colleagues, and let’s keep growing the community.
Let’s now dive into this week’s top insights! 🚀
Table of Contents
🔓 BREACHES & SECURITY INCIDENTS
🇺🇸 TransUnion suffered a data breach that exposed personal information of over 4.4 million people in the United States. The company says the July 28 incident involved a third‑party consumer‑support app and did not include credit reports or core credit data. TransUnion is offering 24 months of free credit monitoring and identity protection to those affected.
🇺🇸 A whistleblower says DOGE employees uploaded the Social Security database to a vulnerable cloud — The move allegedly left sensitive personal data exposed.
🇯🇵 Nissan confirmed a data breach at its design unit Creative Box after suspicious access to a server. The Qilin ransomware group says it stole about 4 TB of files, including 3D car designs, reports, and photos, and posted samples online.
Nissan says it blocked access, reported the incident to police, is investigating, and the leak affects only Nissan.
🇫🇷 French retailer Auchan says a cyberattack exposed personal data from several hundred thousand customer loyalty accounts. Exposed data include names, addresses, emails, phone numbers, and loyalty card numbers, but not bank details, passwords, or PINs. Auchan notified the CNIL, sent breach notices to affected customers, and warned them to watch for phishing.
🇺🇸 Aspire Rural Health System said about 138,386 people were affected by a data breach — Hackers had access from Nov. 4, 2024 to Jan. 6, 2025 and stole files with personal and health information. The BianLian ransomware group claimed responsibility, but it’s unclear what happened to the stolen data.
🇺🇸 Farmers Insurance disclosed a data breach affecting more than 1 million people — The breach came through a third-party vendor and exposed names, addresses, dates of birth, driver’s license numbers, and the last four digits of Social Security numbers. Farmers says it was not directly targeted, is investigating, and it’s unclear if the vendor suffered a ransomware attack.
→ More breaches:
🔗 Partners and Affiliates
With its user-friendly interface, robust security features, and commitment to privacy, NordVPN continues to be a popular choice for individuals seeking online protection and unrestricted internet access.
Special Offer: get up to 73% off with a 2-year plan!
🥷🏻 CYBERCRIME, CYBER ESPIONAGE, APT’s
🇺🇸 🇨🇳 The FBI says the Chinese-backed group called Salt Typhoon has hacked at least 200 U.S. companies and firms in 80 countries. The hackers targeted company routers to steal network traffic and call records for senior U.S. officials. The FBI warns the threat is ongoing and urged encrypted messaging while giving technical guidance to defenders.
🇺🇸 ☎️ The FCC blocked more than 1,200 voice providers from U.S. phone networks for failing to follow anti-robocall rules. They failed to properly certify STIR/SHAKEN caller authentication and robocall mitigation plans. It is the FCC’s largest enforcement action, but old phone systems and overseas scammers still let many robocalls through.
🇵🇰 🇮🇳 Pakistan-linked APT36 is again targeting Indian government and defense organizations. In August 2025 it used phishing ZIPs with Linux .desktop files that fetch a dropper from Google Drive and install persistent malware. The move to Linux payloads and cloud-based delivery shows increased sophistication and a push to diversify access vectors.
🗓️ {Cyber,Info}Sec Events: My list of past and future {cyber,info}sec related events — Feel free to contribute by submitting issues or pull requests (and don’t forget to star the project); Thanks! 😉
👨🏻⚖️ 👀 GOVERNMENT, POLITICS, AND PRIVACY
🤖 👀 They're watching — OpenAI now scans ChatGPT conversations and routes worrying chats to human reviewers. If reviewers find an imminent threat to others, they may notify law enforcement, though OpenAI says it won't refer self-harm cases. Critics say this monitoring is confusing and contradicts the company's privacy promises.
🇺🇸 🥷🏻 Google says it is forming a cyber "disruption unit" to proactively and legally disrupt hacker operations. This comes as U.S. officials and companies debate using more offensive cyber tactics but face legal, ethical, and capability barriers. Supporters say offense is needed to deter attacks; critics warn of escalation and limits.
🇺🇸 Senator Ron Wyden said the federal judiciary showed negligence and incompetence after a hack exposed confidential court documents. Hackers with reported ties to Russia breached the CM/ECF and PACER filing systems using vulnerabilities known since 2020. Authorities call the breach a severe national security threat and warn the court system faces constant, sophisticated attacks.
🔗 Partners and Affiliates

🌐 Stay connected and secure on the go with Airalo's global eSIMs — Use the code NEWTOAIRALO15 if you’re new to Airalo to get an additional 15% discount.
🦠 MALWARE & THREATS
⚠️ ‼️ ghrc.io is a typo-squatted site that pretends to be the GitHub container registry — It asks container tools to send credentials to its token endpoint, which can steal logins. If you logged into ghrc.io, change your password, revoke any PATs, and check for suspicious activity.
📧 MixShell Malware Delivered via Contact Forms — Attackers use company "Contact Us" forms to start believable, weeks-long conversations with manufacturing staff. They send fake NDAs and weaponized ZIPs that run an LNK/PowerShell loader to deploy MixShell, an in-memory malware using DNS-based command-and-control. The campaign targets U.S. supply-chain manufacturers, risks IP theft, fraud and disruptions, and hides behind legitimate services.
🤖 ESET found PromptLock, a proof-of-concept ransomware that uses OpenAI’s gpt-oss:20b via Ollama to generate malicious Lua scripts on the fly. It can list, steal, and encrypt files with SPECK 128-bit, and its AI-generated artifacts change each run, making detection harder. This shows LLMs and prompt-injection or model-routing flaws let attackers build more evasive malware with less skill.
🏦 🎠 The Anatsa Android banking trojan now targets over 830 banking and cryptocurrency apps worldwide. It spreads through fake apps on Google Play and uses accessibility, overlay, and anti-analysis tricks to steal logins and perform fraud. Zscaler found 77 malicious apps with over 19 million downloads and urges users to check app permissions.
🤖 🧰 AI, CRYPTO, TECH & TOOLS
🌐 Anthropic released Claude for Chrome, an extension that lets the AI control websites and act for users. Researchers warn web pages can trick such AI agents, with tests showing they were fooled nearly a quarter of the time. Anthropic is limiting the launch to a paid research preview for 1,000 Max-plan subscribers while it studies the risks.
🐛 🧠 VULNERABILITIES, RESEARCH, AND THREAT INTELLIGENCE
➝ From the Patching Department:
🔓 👀 A critical bug in the TheTruthSpy phone spyware lets anyone reset passwords and hijack accounts, exposing victims’ private phone data. TheTruthSpy and its sister apps have a long history of breaches and rebrands, showing they can’t be trusted to protect people. The operators haven’t fixed the flaw and thousands of unknowingly monitored victims remain at risk.
🔓 More than 28,200 Citrix NetScaler instances are vulnerable to a critical zero-day RCE (CVE-2025-7775) that is being actively exploited. Citrix released firmware updates and urges immediate upgrades, saying no workaround exists. CISA added the flaw to its KEV and ordered federal agencies to patch or stop using affected products by August 28.
🕸️ DSLRoot, Proxies, and the Threat of ‘Legal Botnets’ — DSLRoot is a residential proxy service that pays people to plug devices into their home Internet. Its operators have ties to shady forum accounts and software that can control routers and scan nearby Wi‑Fi. Researchers warn this creates a “legal botnet” that can be abused and puts unwitting hosts at risk.
💥 A Git bug (CVE-2025-48384) can let attackers write files and trigger code execution by abusing submodule paths that end with a carriage return. It affects macOS and Linux, and proof-of-concept exploit code appeared after Git released patches. CISA added the flaw to its KEV list and urges immediate patching by September 15.
📍 🚗 A researcher found more than 1,300 public TeslaMate servers leaking Tesla vehicle data and detailed location histories. TeslaMate is a self-hosted logger that stores trips, battery and charging info, and other sensitive data. The researcher warned users to enable authentication and firewalls because many dashboards were accidentally exposed.
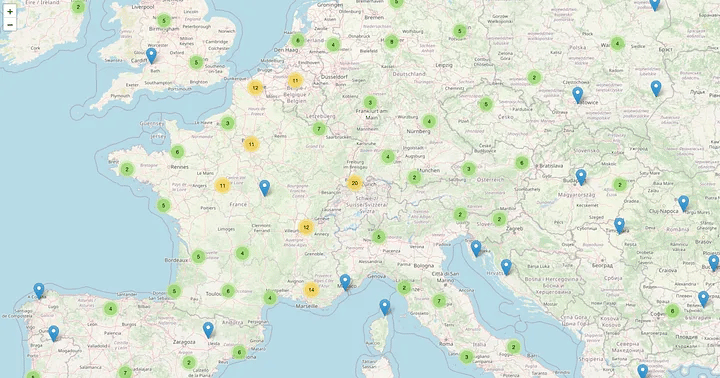
Figure: teslamap.io | Map created from exposed TeslaMate instances/s3yfullah.medium.com
🛰️ ICS, OT & IoT
🐛 🔓 A zero-day in FreePBX admin panels has been actively exploited since August 21 — Sangoma released an EDGE patch and will issue a full security update, but some users may be unable to install it. Admins should block public ACP access, check for IOCs (missing/modified /etc/freepbx.conf, .clean.sh, suspicious logs, unknown ampuser), and restore pre‑Aug 21 backups and rotate credentials if compromised.
💬 CONNECT
Follow me on Mastodon for quick daily updates and bite-sized content.
Prefer using an RSS feed? Add Infosec MASHUP to your feed here.
Enjoying our newsletter? Forward it to a colleague—
it’s one of the best ways to support us.
Thanks for reading today’s newsletter, and if you're enjoying it and want to support my work, you can buy me a coffee ☕ over at https://www.buymeacoffee.com/0x58
See you next time!
-X.




