InfoSec MASHUP - Week 18/2024
Change Healthcare compromised through stolen credentials and no MFA; Marriott lied for five years; Dropbox breach; Verizon DBIR 2024; New guidelines and frameworks for (Gen)AI;
Partners and affiliates section
🔐 NordVPN’s Spring Sale Campaign (May 2 - Jun 12)
Special offer update:
🇺🇸 USA & 🇸🇪 Sweden: up to 74% off + 3 months extra
🇬🇧 UK, 🇩🇪 Germany, 🇳🇱 Netherlands, 🇮🇹 Italy, 🇫🇷 France: up to 73% off + 3 months extra
🌍 Rest: up to 75% off + 3 months extra
Breaches & Security Incidents
🔓 🇺🇸 Panda Restaurants discloses data breach after corporate systems hack
"After a thorough investigation, we determined that certain information maintained on our corporate systems was accessed by the unauthorized actor between March 7-11, 2024," Panda said in notification letters sent to affected individuals.
"With the support of third-party experts, we then began a thorough review of the data affected to identify the specific information and individuals impacted. On April 15, we concluded our review of impacted data and determined that your personal information was involved."
🔓 📦 Dropbox Data Breach Impacts Customer Information
Dropbox Sign, formerly known as HelloSign, enables users to send, receive and manage legally binding e-signatures.
According to Dropbox, a threat actor gained access to the Sign production environment and accessed customer information, including email addresses, usernames, phone numbers, hashed passwords, data on general account settings, and authentication data such as API keys, OAuth tokens and multi-factor authentication.
🇺🇸 🫣 Marriott admits it falsely claimed for five years it was using encryption during 2018 breach
For more than five years, Marriott has defended a massive 2018 data breach by arguing that its encryption level (AES-128) was so strong that the case against it should be dismissed. But attorneys for the hotel chain admitted in an April 10 hearing that it had never used AES-128 during the time of the breach.
In fact, it hadn’t been using any encryption at all at the time but rather had been using secure hash algorithm 1 (SHA-1), which is a hashing mechanism and not encryption.
🔓 🇺🇸 Change Healthcare hackers broke in using stolen credentials — and no MFA, says UHG CEO
UnitedHealth CEO Andrew Witty provided the written testimony ahead of a House subcommittee hearing on Wednesday into the February ransomware attack that caused months of disruption across the U.S. healthcare system.
According to Witty’s testimony, the criminal hackers “used compromised credentials to remotely access a Change Healthcare Citrix portal.” Organizations like Change use Citrix software to let employees access their work computers remotely on their internal networks.
Related: UnitedHealth CEO tells Senate all systems now have multi-factor authentication after hack
Related: Data stolen in Change Healthcare attack likely included U.S. service members, executive says
🔓 🇺🇸 Kaiser Permanente Data Breach Impacts 13.4 Million Patients
“Information that could indicate a member or patient was signed into a Kaiser Permanente account or service, information showing how a member or patient interacted with and navigated through the website and mobile applications” was also compromised, the company said.
“No usernames, passwords, Social Security numbers, financial account information, or credit card numbers were included in the transmission to these third parties,” Kaiser Permanente said.
Cybercrime, Cyber Espionage, APT’s
📞 ❌ Police shuts down 12 fraud call centres, arrests 21 suspects
Law enforcement shut down 12 phone fraud call centers in Albania, Bosnia and Herzegovina, Kosovo, and Lebanon, behind thousands of scam calls daily.
Dozens of German law enforcement officers, aided by hundreds of counterparts from other countries (i.e., Albania, Bosnia and Herzegovina, Kosovo, and Lebanon), carried out numerous raids on April 18, identifying 39 suspects and arresting 21 individuals.
They also confiscated evidence, including data carriers, documents, cash, and other assets, valued at roughly €1 million.
🇺🇦 🇺🇸 Ukrainian REvil Hacker Sentenced to 13 Years and Ordered to Pay $16 Million
Yaroslav Vasinskyi (aka Rabotnik), 24, along with his co-conspirators part of the REvil ransomware group orchestrated more than 2,500 ransomware attacks and demanded ransom payments in cryptocurrency totaling more than $700 million.
"The co-conspirators demanded ransom payments in cryptocurrency and used cryptocurrency exchangers and mixing services to hide their ill-gotten gains," the U.S. Department of Justice (DoJ) said.
🇫🇷 💸 French hospital CHC-SV refuses to pay LockBit extortion demand
The Hôpital de Cannes - Simone Veil (CHC-SV) in France announced it received a ransom demand from the Lockbit 3.0 ransomware gang, saying they refuse to pay the ransom.
On April 17, the 840-bed hospital announced a severe operational disruption caused by a cyberattack that forced it to take all computers offline and reschedule non-emergency procedures and appointments.
Yesterday, the establishment announced on X that it has received a ransom demand by the Lockbit 3.0 ransomware operation, which it forwarded to the Gendarmerie and the National Agency for Information Systems Security (ANSSI).
🇷🇺 💸 Bitcoin Forensic Analysis Uncovers Money Laundering Clusters and Criminal Proceeds
A forensic analysis of a graph dataset containing transactions on the Bitcoin blockchain has revealed clusters associated with illicit activity and money laundering, including detecting criminal proceeds sent to a crypto exchange and previously unknown wallets belonging to a Russian darknet market.
🇺🇸 🇷🇺 Ex-NSA Employee Sentenced to 22 Years for Trying to Sell U.S. Secrets to Russia
"This sentence should serve as a stark warning to all those entrusted with protecting national defense information that there are consequences to betraying that trust," said FBI Director Christopher Wray.
Jareh Sebastian Dalke, 32, of Colorado Springs was employed as an Information Systems Security Designer between June 6 to July 1, 2022, during which time he had access to sensitive information.
🇨🇳 China-Linked 'Muddling Meerkat' Hijacks DNS to Map Internet on Global Scale
A previously undocumented cyber threat dubbed Muddling Meerkat has been observed undertaking sophisticated domain name system (DNS) activities in a likely effort to evade security measures and conduct reconnaissance of networks across the world since October 2019.
"Muddling Meerkat demonstrates a sophisticated understanding of DNS that is uncommon among threat actors today – clearly pointing out that DNS is a powerful weapon leveraged by adversaries," the company said in a report shared with The Hacker News.
🇧🇾 Hackers Claim to Have Infiltrated Belarus’ Main Security Service
The authorities have not commented on the claim, but the website of the Belarusian KGB was opening with an empty page on Friday that said it was “in the process of development”.
Seeking to back up its claim, the Belarusian Cyber-Partisans group published a list of the website’s administrators, its database and server logs on its page in the messaging app Telegram.
Government, Politics, and Privacy
An updated version of the methodology to be used in the Child Sexual Abuse Regulation, leaked by the news portal Contexte, reveals more details on the approach pursued by the Belgian Council Presidency: The text doubles-down on services that allow people to protect themselves. If services are used through pseudonyms, VPNs, encryption or without an account, they will score worse on the risk scale, and will be more likely to be served a detection order mandating scanning of all communications content.
Pirate Party Member of the European Parliament and digital freedom fighter Patrick Breyer comments: “Basic services such as Signal, TOR, encrypted email services like ProtonMail, torrenting platfroms are being demonized by this methodology. Privacy-friendly communication services are to become the most extremely monitored. […]”
🇫🇮 ⚖️ Man Who Mass-Extorted Psychotherapy Patients Gets Six Years
A 26-year-old Finnish man was sentenced to more than six years in prison today after being convicted of hacking into an online psychotherapy clinic, leaking tens of thousands of patient therapy records, and attempting to extort the clinic and patients.
On October 21, 2020, the Vastaamo Psychotherapy Center in Finland became the target of blackmail when a tormentor identified as “ransom_man” demanded payment of 40 bitcoins (~450,000 euros at the time) in return for a promise not to publish highly sensitive therapy session notes Vastaamo had exposed online.
🇺🇸 🇨🇳 How TikTok Grew From a Fun App for Teens Into a Potential National Security Threat
Starting in 2017, when the Chinese social video app merged with its competitor Musical.ly, TikTok has grown from a niche teen app into a global trendsetter. While, of course, also emerging as a potential national security threat, according to U.S. officials.
On Wednesday, President Joe Biden signed legislation requiring TikTok parent ByteDance to sell to a U.S. owner within a year or to shut down. It’s not clear whether that law will survive an expected legal challenge or that ByteDance would agree to sell.
🇺🇸 💰 FCC takes $200 million bite out of wireless carriers for sharing location data
“These carriers failed to protect the information entrusted to them,” FCC Chairwoman Jessica Rosenworcel said in a statement. “Here, we are talking about some of the most sensitive data in their possession: customers’ real-time location information, revealing where they go and who they are.”
🇬🇧 Smart gadgets: Tougher rules for sellers of internet-enabled devices in the UK
Manufacturers will have to follow stricter rules if they want to sell "smart" gadgets in the UK after a new law came into effect.
It is designed to ensure there is better security around devices such as baby monitors, televisions and speakers that are linked to the internet.
ICS & OT
🇷🇺 💦 Pro-Russia hacktivists attacking vital tech in water and other sectors, agencies say
“The pro-Russia hacktivist activity appears mostly limited to unsophisticated techniques that manipulate ICS equipment to create nuisance effects,” according to the agencies. “However, investigations have identified that these actors are capable of techniques that pose physical threats against insecure and misconfigured OT environments.”
The hacktivists have carried out disruptions “causing water pumps and blower equipment to exceed their normal operating parameters,” and “in each case, the hacktivists maxed out set points, altered other settings, turned off alarm mechanisms, and changed administrative passwords.”
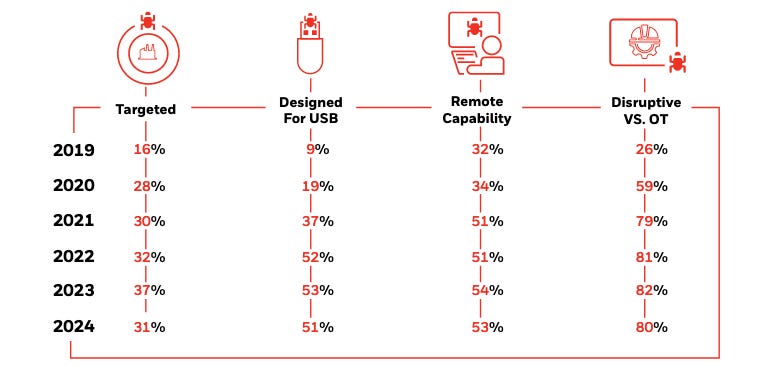
🔑 🦠 USB Malware Attacks on Industrial Orgs Becoming More Sophisticated
Industrial giant Honeywell has published its sixth annual report on the threat posed by USB-borne malware to industrial organizations, warning of an increase in sophistication.
The report is based on analysis conducted by the company’s Global Analysis, Research and Defense (GARD) team using data collected by a security product designed to detect and block malware on USB drives used in customers’ industrial environments.
Malware & Threats
🇰🇵 🎣 NSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
"The DPRK [Democratic People's Republic of Korea] leverages these spear-phishing campaigns to collect intelligence on geopolitical events, adversary foreign policy strategies, and any information affecting DPRK interests by gaining illicit access to targets' private documents, research, and communications," NSA said.
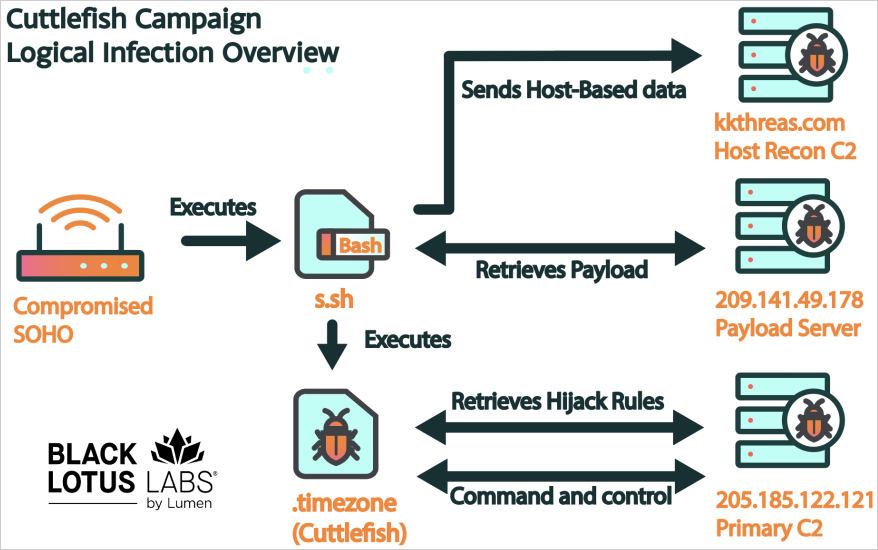
🦠 🐟 New Cuttlefish malware infects routers to monitor traffic for credentials
Lumen Technologies' Black Lotus Labs examined the new malware and reports that Cuttlefish creates a proxy or VPN tunnel on the compromised router to exfiltrate data discreetly while bypassing security measures that detect unusual sign-ins.
The malware can also perform DNS and HTTP hijacking within private IP spaces, interfering with internal communications and possibly introducing more payloads.
🦠 🚢 Millions of Docker repos found pushing malware, phishing sites
The researchers discovered almost 4.6 million repositories containing no Docker images—which couldn't be run using a Kubernetes cluster or a Docker engine—and linked approximately 2.81 million to three large malicious campaigns.
Each of these campaigns used different tactics to create and distribute the malicious repositories. The "Downloader" and "eBook Phishing" campaigns created fake repositories in batches, while the "Website SEO" campaign created a few repositories daily and used a single user per repository.
🦠 🤖 Android Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
"Wpeeper is a typical backdoor Trojan for Android systems, supporting functions such as collecting sensitive device information, managing files and directories, uploading and downloading, and executing commands," researchers from the QiAnXin XLab team said.
The ELF binary is embedded within a repackaged application that purports to be the UPtodown App Store app for Android (package name "com.uptodown"), with the APK file acting as a delivery vehicle for the backdoor in a manner that evades detection.
💥 Okta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
These unprecedented attacks, observed over the last month, are said to be facilitated by "the broad availability of residential proxy services, lists of previously stolen credentials ('combo lists'), and scripting tools," the company said in an alert published Saturday.
"These attacks all appear to be originating from TOR exit nodes and a range of other anonymizing tunnels and proxies," Talos noted at the time, adding targets of the attacks comprise VPN appliances from Cisco, Check Point, Fortinet, SonicWall, as well as routers from Draytek, MikroTik, and Ubiquiti.
AI, Tech & Tools
Google Announces Passkeys Adopted by Over 400 Million Accounts
Passkey support comes to Word, Excel, and more for all consumer Microsoft accounts
🤖 🇯🇵 Japan’s Kishida Unveils a Framework for Global Regulation of Generative AI
Japanese Prime Minister Fumio Kishida unveiled an international framework for regulation and use of generative AI on Thursday, adding to global efforts on governance for the rapidly advancing technology.
Kishida made the announcement in a speech at the Paris-based Organization for Economic Cooperation and Development.
“Generative AI has the potential to be a vital tool to further enrich the world,” Kishida said. But “we must also confront the dark side of AI, such as the risk of disinformation.”
🤖 🔐 CISA unveils guidelines for AI and critical infrastructure
The guidelines are meant to address both the opportunities made possible by artificial intelligence for critical infrastructure — which spans 16 sectors, including farming and information technology — and the ways it could be weaponized or misused. CISA instructs operators and owners of critical infrastructure to govern, map, measure, and manage their use of the technology, incorporating the National Institute of Standards and Technology’s AI risk management framework.
Related: Critics question tech-heavy lineup of new Homeland Security AI safety board
📱 Google Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
"In 2023, we prevented 2.28 million policy-violating apps from being published on Google Play in part thanks to our investment in new and improved security features, policy updates, and advanced machine learning and app review processes," Google's Steve Kafka, Khawaja Shams, and Mohet Saxena said.
"To help safeguard user privacy at scale, we partnered with SDK providers to limit sensitive data access and sharing, enhancing the privacy posture for over 31 SDKs impacting 790K+ apps."
Vulnerabilities, Research, and Threat Intelligence
🗒️ 🔎 Verizon DBIR 2024 Shows Surge in Vulnerability Exploitation, Confirmed Data Breaches
For the 2024 DBIR, Verizon analyzed more than 30,000 security incidents and over 10,000 confirmed data breaches. The number of incidents and confirmed breaches has doubled compared to the previous year.
Verizon has highlighted that the exploitation of vulnerability was an initial point of entry in 14% of breaches, which represents a 180% increase compared to the previous year. This surge was partly fueled by the MOVEit attacks and other zero-days leveraged by ransomware groups.
🐛 🚨 Maximum-severity GitLab flaw allowing account hijacking under active exploitation
A change GitLab implemented in May 2023 made it possible for users to initiate password changes through links sent to secondary email addresses. The move was designed to permit resets when users didn’t have access to the email address used to establish the account. In January, GitLab disclosed that the feature allowed attackers to send reset emails to accounts they controlled and from there click on the embedded link and take over the account.
While exploits require no user interaction, hijackings work only against accounts that aren’t configured to use multifactor authentication. Even with MFA, accounts remained vulnerable to password resets, but the attackers ultimately are unable to access the account, allowing the rightful owner to change the reset password. The vulnerability, tracked as CVE-2023-7028, carries a severity rating of 10 out of 10.
🐛 🚨 Critical Vulnerabilities in Judge0 Lead to Sandbox Escape, Host Takeover
Three critical-severity vulnerabilities in the Judge0 open source service could allow attackers to perform sandbox escapes and completely take over the host machine, according to a warning from cybersecurity firm Tanto Security.
The company documented the flaws in an advisory that warns that Judge0 versions prior to 1.13.1 are impacted by CVE-2024-28185, CVE-2024-28189, and CVE-2024-29021, three issues that allow attackers to achieve code execution outside the sandbox and escalate their privileges to completely take over the Judge0 system.
The company said CVE-2024-28185 (CVSS 10/10) exists because the application does not account for symlinks stored in the sandbox directory, allowing an attacker to create the symlink and exploit a Judge0 function where a run_script is written to the sandbox directory when executing a submission.
🇮🇷 Iranian hackers impersonate journalists in social engineering campaign
A hacking group linked to the intelligence wing of Iran’s Revolutionary Guard Corps impersonated journalists and human rights activists as part of a social engineering campaign, according to research released Wednesday by Mandiant and Google Cloud.
The news organizations impersonated in the operation include The Washington Post, The Economist and The Jerusalem Post, and Mandiant’s researchers assess that the campaign was carried out by the hacking crew known as APT42. The group also spoofed prominent Washington think tanks, including the Aspen Institute, the McCain Institute and the Washington Institute.
🐛 💰 Google now pays up to $450,000 for RCE bugs in some Android apps
Google has increased rewards for reporting remote code execution vulnerabilities within select Android apps by ten times, from $30,000 to $300,000, with the maximum reward reaching $450,000 for exceptional quality reports.
The company made these changes to the Mobile Vulnerability Rewards Program (Mobile VRP) and they apply to what it describes as Tier 1 applications.
The list of in-scope apps includes Google Play Services, the Android Google Search app (AGSA), Google Cloud, and Gmail.
🐛 R language flaw allows code execution via RDS/RDX files
Researchers at HiddenLayer recently discovered a vulnerability in R, tracked as CVE-2024-27322 (CVSS v3: 8.8), that enables attackers to run arbitrary code on target machines when the victim opens R Data Serialization (RDS) or R package files (RDX).
The vulnerability exploits the way R handles serialization ('saveRDS') and deserialization ('readRDS'), particularly through promise objects and "lazy evaluation."
Attackers can embed promise objects with arbitrary code in the RDS file metadata in the form of expressions, which are evaluated during deserialization, resulting in the code's execution.